自從上次“劫持”事情后,項目經理將所有跟安全相關的都推給我了(不算 KPI 又要被白嫖,煩死了)。這次客戶又提了一個服務器安全掃描和漏洞修復的“活”,我這邊順手將過程記錄一下,就當經驗總結跟各位分享一下。
本次掃描的是一臺 Ubuntu Server,用的是 22.04 版本操作系統。據說客戶一直都是用 CentOS 7 ,但由于今年 6 月 30 日后 CentOS 7 不再提供安全維護了,索性新應用的機器全部換成 Ubuntu Server (額…其實我想說換 openEuler 也挺好的,也符合信創標準)。
1. Ubuntu OVAL 數據掃描
由于用的是 Ubuntu 操作系統,為此本次掃描將使用 Canonical (Ubuntu 母公司)安全小組提供的 Ubuntu OVAL 數據,如下圖:
具體就是使用 oscap 讀取 OVAL 數據(USN 和 CVE)進行掃描,為了方便我寫了一個 shell 腳本,如下圖:
# 先從官網下載最新 OVAL 數據
wget https://security-metadata.canonical.com/oval/com.ubuntu.$(lsb_release -cs).usn.oval.xml.bz2
wget https://security-metadata.canonical.com/oval/com.ubuntu.$(lsb_release -cs).cve.oval.xml.bz2# 通過 bunzip2 對壓縮包進行解壓
bunzip2 com.ubuntu.$(lsb_release -cs).usn.oval.xml.bz2
bunzip2 com.ubuntu.$(lsb_release -cs).cve.oval.xml.bz2# 使用 oscap 讀取 oval 數據并產出 html 報告
oscap oval eval --report report_usn.html com.ubuntu.$(lsb_release -cs).usn.oval.xml
oscap oval eval --report report_cve.html com.ubuntu.$(lsb_release -cs).cve.oval.xml
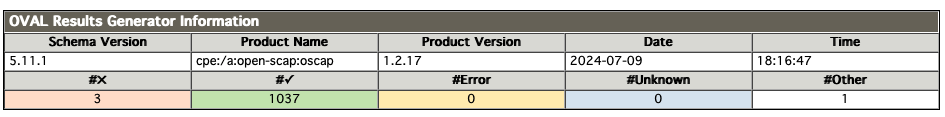
掃描結果如下圖所示:
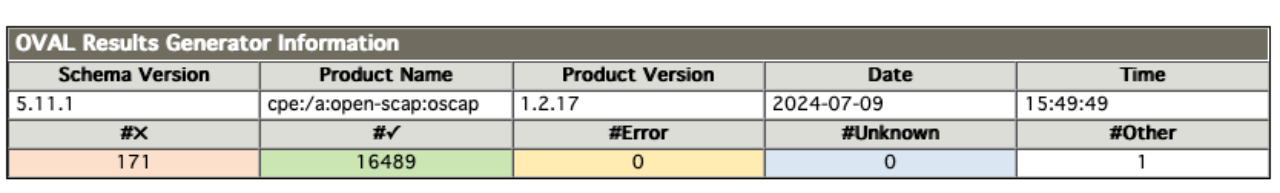
上圖是 CVE 漏洞統計共有 171 個,而 USN 有 11 個,如下圖所示。
2. 修復處理
2.1 基礎修復
面對如此數量的漏洞,第一個想到的辦法肯定是直接通過升級批量修復漏洞。如下圖:
sudo apt update
sudo apt upgrade
sudo apt dist-upgrade
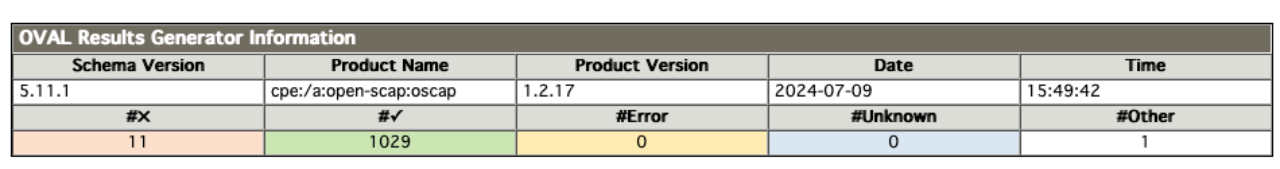
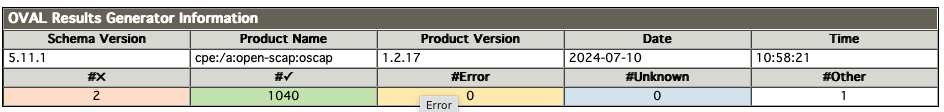
升級后再進行 oscap 掃描得到以下結果:
CVE 減少到 151 個,而 USN 減少到 3 個。
2.2 解除“不更新”標記
以上結果跟我預估有所出入,本以為通過更新能至少解決三分之一的漏洞,但 CVE 只修復了 20 個,有點不太正常。于是我執行了 apt list --upgradable 指令發現仍存在部分可升級內容,如下圖:
ubuntu@VM-0-6-ubuntu:~$ apt list --upgradable
Listing... Done
linux-generic/jammy-updates,jammy-security 5.15.0.113.113 amd64 [upgradable from: 5.15.0.107.107]
linux-headers-generic/jammy-updates,jammy-security 5.15.0.113.113 amd64 [upgradable from: 5.15.0.107.107]
linux-image-generic/jammy-updates,jammy-security 5.15.0.113.113 amd64 [upgradable from: 5.15.0.107.107]
python3-update-manager/jammy-updates 1:22.04.20 all [upgradable from: 1:22.04.9]
ubuntu-minimal/jammy-updates 1.481.2 amd64 [upgradable from: 1.481.1]
ubuntu-server/jammy-updates 1.481.2 amd64 [upgradable from: 1.481.1]
ubuntu-standard/jammy-updates 1.481.2 amd64 [upgradable from: 1.481.1]
update-manager-core/jammy-updates 1:22.04.20 all [upgradable from: 1:22.04.9]
嗯…估計是客戶方運維將這些組件進行了標記,導致不能自動升級。于是嘗試執行 apt-mark showhold 指令來驗證一下自己的猜想,如下圖:
ubuntu@VM-0-6-ubuntu:~$ sudo apt-mark showhold
containerd.io
docker-buildx-plugin
docker-ce
docker-ce-cli
docker-ce-rootless-extras
docker-compose-plugin
docker-scan-plugin
linux-generic
linux-generic-hwe-20.04
linux-generic-hwe-20.04-edge
linux-generic-hwe-22.04
linux-generic-hwe-22.04-edge
linux-headers-generic
linux-headers-generic-hwe-20.04
linux-headers-generic-hwe-20.04-edge
linux-headers-generic-hwe-22.04
linux-headers-generic-hwe-22.04-edge
linux-image-generic
linux-image-generic-hwe-20.04
linux-image-generic-hwe-20.04-edge
linux-image-generic-hwe-22.04
linux-image-generic-hwe-22.04-edge
如上圖所示 linux-generic、linux-headers-generic 和 linux-image-generic 都被標記為“不隨系統更新”,這印證了我的想法,但為什么要這樣做呢?
先不管了,在做完快照備份后接著將 linux-generic、linux-headers-generic 和 linux-image-generic 解除標記,如下圖:
ubuntu@VM-0-6-ubuntu:~$ sudo apt-mark unhold linux-generic* linux-headers-generic* linux-image-generic*
Canceled hold on linux-generic.
Canceled hold on linux-generic-hwe-20.04.
Canceled hold on linux-generic-hwe-22.04.
Canceled hold on linux-generic-hwe-20.04-edge.
Canceled hold on linux-generic-hwe-22.04-edge.
Canceled hold on linux-headers-generic.
Canceled hold on linux-headers-generic-hwe-22.04.
Canceled hold on linux-headers-generic-hwe-22.04-edge.
Canceled hold on linux-headers-generic-hwe-20.04.
Canceled hold on linux-headers-generic-hwe-20.04-edge.
Canceled hold on linux-image-generic.
Canceled hold on linux-image-generic-hwe-22.04.
Canceled hold on linux-image-generic-hwe-22.04-edge.
Canceled hold on linux-image-generic-hwe-20.04.
Canceled hold on linux-image-generic-hwe-20.04-edge.
之后執行分布更新,如下圖:
ubuntu@VM-0-6-ubuntu:~$ sudo apt-get dist-upgrade
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
Calculating upgrade... Done
The following NEW packages will be installed:linux-headers-5.15.0-113 linux-headers-5.15.0-113-generic linux-image-5.15.0-113-generic linux-modules-5.15.0-113-genericlinux-modules-extra-5.15.0-113-generic
The following packages have been kept back:python3-update-manager ubuntu-minimal ubuntu-server ubuntu-standard update-manager-core
The following packages will be upgraded:linux-generic linux-headers-generic linux-image-generic
3 upgraded, 5 newly installed, 0 to remove and 5 not upgraded.
Need to get 113 MB of archives.
After this operation, 583 MB of additional disk space will be used.
再重新掃描一次。嗯…問題依然存在(漏洞數沒有改變,這里就不再截圖展示了)。
2.3 查“漏”補“缺”
因為漏洞數沒有改變,于是再次執行 upgrade 命令得到新的發現,如下圖:
ubuntu@VM-0-6-ubuntu:~$ sudo apt upgrade
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
Calculating upgrade... Done
The following packages have been kept back:python3-update-manager ubuntu-minimal ubuntu-server ubuntu-standard update-manager-core
0 upgraded, 0 newly installed, 0 to remove and 5 not upgraded.
5 not upgrade?提示中明顯標注了 python3-update-manager、ubuntu-minimal、ubuntu-server、ubuntu-standard、update-manager-core 沒有更新。既然沒有更新那就針對這 5 個組件進行 upgrade 操作,如下圖:
ubuntu@VM-0-6-ubuntu:~$ sudo apt upgrade python3-update-manager ubuntu-minimal ubuntu-server ubuntu-standard update-manager-core
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
Calculating upgrade... Done
The following packages will be upgraded:python3-update-manager ubuntu-minimal ubuntu-server ubuntu-standard update-manager-core
5 upgraded, 0 newly installed, 0 to remove and 0 not upgraded.
Need to get 59.1 kB of archives.
After this operation, 6,144 B of additional disk space will be used.
再掃描一次,結果如下:
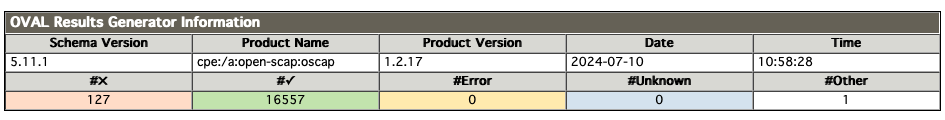
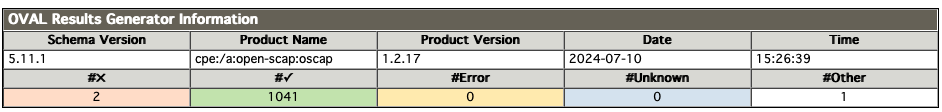
CVE 漏洞減少到 127 個,而 USN 漏洞減少到 2 個。還是有 100+ 的 CVE 漏洞沒有修復完畢,究竟是為什么呢?帶著這些疑問我執行以下語句:
sudo unattended-upgrades --dry-run
本以為還有安全補丁沒有更新,結果直接沒有返回,看來應該做的一切都已經做了。
3. 進一步排查
這 100+ 的 CVE 漏洞究竟為什么無法修復呢?難道是內核導致的?帶著這個疑問我注冊了一個 Canonical Livepatch 的賬號,想通過 livepatch 檢查一下是否跟內核有關,如下圖:
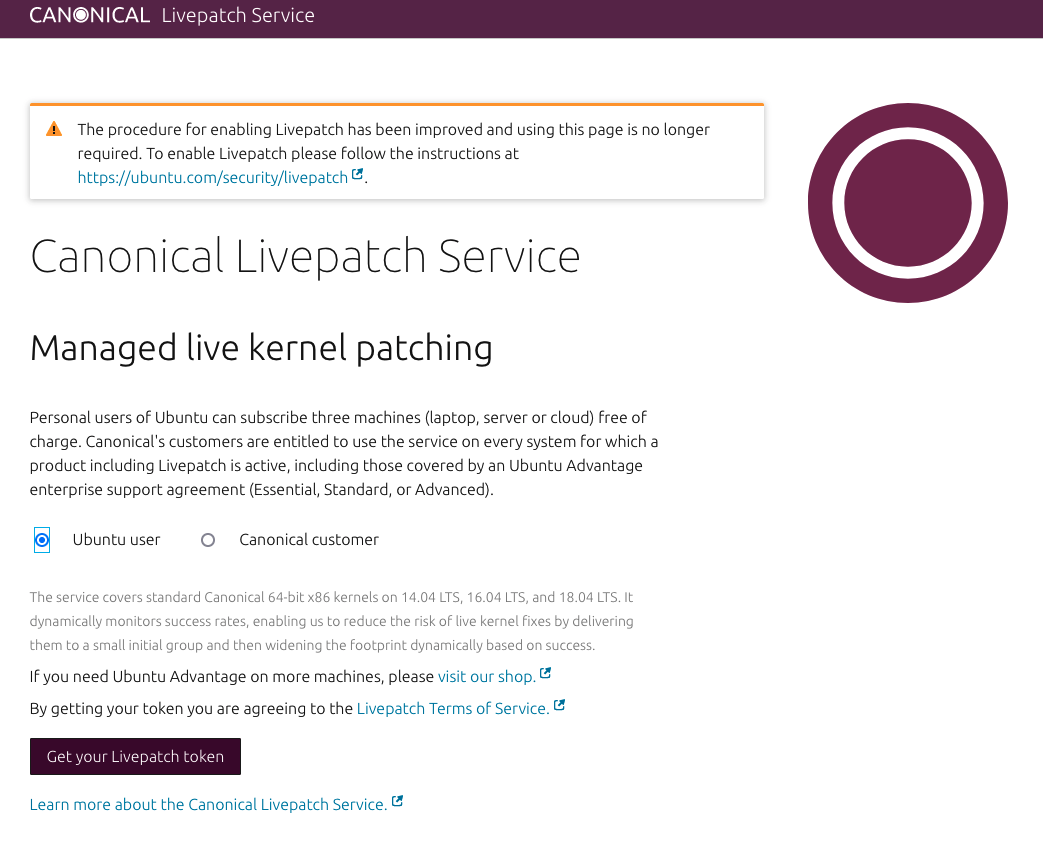
關于 Canonical Livepatch 賬號申請我就不多說了(這個不是重點)。注冊完成后會得到一個 token,這個 token 將用于服務器與 Canonical Livepatch 進行通訊的。但在此之前還需要使用 snap 安裝 canonical-livepatch ,如下圖:
ubuntu@VM-0-6-ubuntu:~/openscap$ sudo snap install canonical-livepatch
canonical-livepatch 10.8.3 from Canonical? installed
ubuntu@VM-0-6-ubuntu:~/openscap$ sudo canonical-livepatch enable <Your Token>
Successfully enabled device. Using machine-token: xxxxx
接著就可以通過 canonical-livepatch 查看一下系統的狀態,如下圖:
ubuntu@VM-0-6-ubuntu:~/openscap$ sudo canonical-livepatch status --verbose
last check: 2 minutes ago
kernel: (unsupported)
server check-in: succeeded
kernel state: ? kernel is not covered by Livepatch
patch state: ? no livepatches available for kernel (unsupported)
tier: updates (Free usage; This machine beta tests new patches.)
machine id: e0fd450343fa48d8acc471dc903518d1
client version: 10.8.3
architecture: amd64
cpu model: AMD EPYC 9754 128-Core Processor
boot time: 37 minutes ago
kernel unsupported?kernel is not covered by Livepatch?
呃…我應該沒做什么騷操作吧。什么也別說了,我還是先重啟一下系統吧(自我安慰一下)。
不過這次重啟我特別留意了一下內核版本,如下圖:
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 6.6.16-060616-generic x86_64)* Documentation: https://help.ubuntu.com* Management: https://landscape.canonical.com* Support: https://ubuntu.com/proSystem information as of Wed Jul 10 10:58:45 AM CST 2024...
GNU/Linux 6.6.16-060616-generic x86_64?我印象中 Ubuntu 最新內核應該是 5.15.x 才對(我開發電腦也是使用 22.04 的 Ubuntu Desktop)。后面找了客戶方運維了解得知這個 6.6.16 版本是他從 kernel.org 手動下載升級的。原因是他們集團發公告告知需要升級,如下圖:
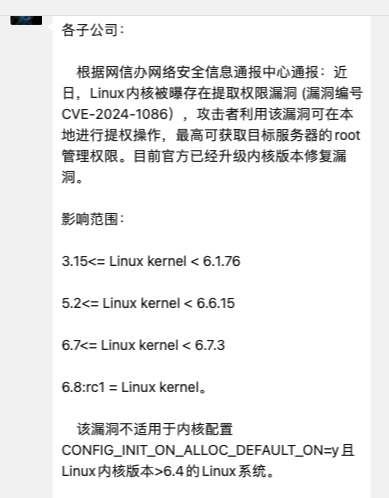
如公告所示,內核升級主要是為了解決 CVE-2024-1086 漏洞,但如果直接按照公告提示升級,內核就需要升級到 6.6.15 版本以上。但事實真的是這樣嗎?
通過 Canonical 安全小組發布的公告得知 CVE-2024-1086 漏洞已經在 5.15.0 內核版本中得到修復,如下圖:
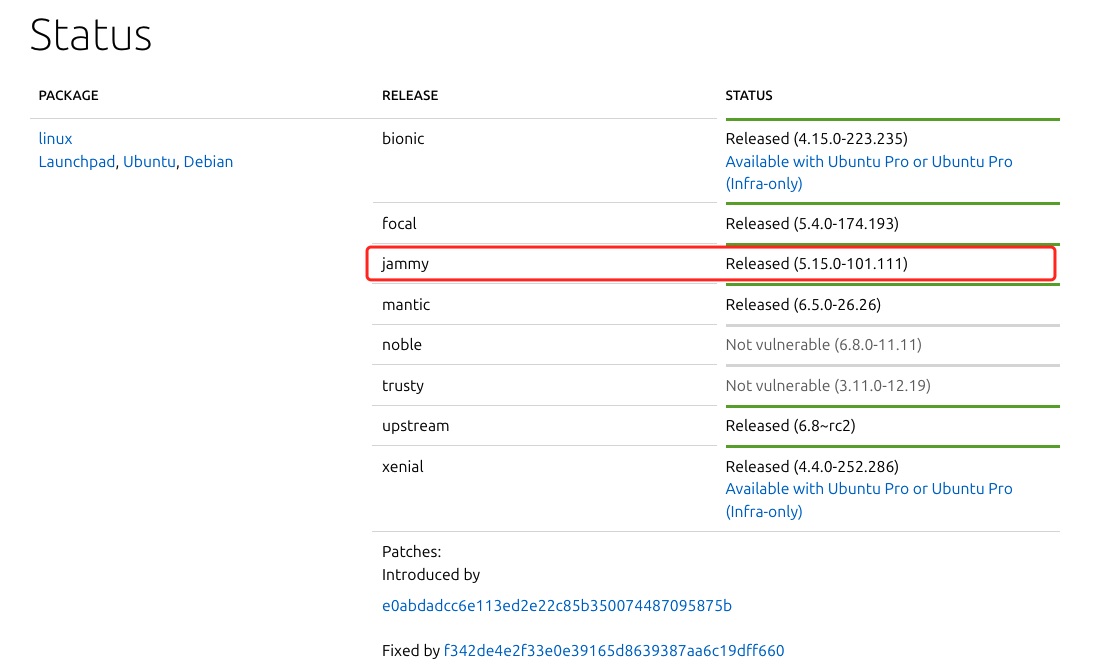
公告地址:https://ubuntu.com/security/CVE-2024-1086
如此一來就沒有必要升級到 6.6.16 版本的內核。
4. 內核降級(吃癟開始)
由于現在使用的是 6.6.16 內核,要先切換到 5.15.x 版本,如下圖:
ubuntu@VM-0-6-ubuntu:~$ dpkg --list | grep linux-image
rc linux-image-5.15.0-101-generic 5.15.0-101.111 amd64 Signed kernel image generic
rc linux-image-5.15.0-105-generic 5.15.0-105.115 amd64 Signed kernel image generic
ii linux-image-5.15.0-107-generic 5.15.0-107.117 amd64 Signed kernel image generic
ii linux-image-5.15.0-113-generic 5.15.0-113.123 amd64 Signed kernel image generic
ii linux-image-generic 5.15.0.113.113 amd64 Generic Linux kernel image
pi linux-image-unsigned-6.6.16-060616-generic 6.6.16-060616.202402051536 amd64 Linux kernel image for version 6.6.16 on 64 bit x86 SMP
如上圖所示,使用 dpkg --list | grep linux-image 指令查看可用的內核版本。再使用 update-initramfs 更新使用內核版本,如下圖:
ubuntu@VM-0-6-ubuntu:~$ sudo update-initramfs -u -k 5.15.0-113-generic
update-initramfs: Generating /boot/initrd.img-5.15.0-113-generic
再之后使用 update-grub 更新引導
ubuntu@VM-0-6-ubuntu:~$ sudo update-grub
Sourcing file `/etc/default/grub'
Sourcing file `/etc/default/grub.d/init-select.cfg'
Sourcing file `/etc/default/grub.d/kdump-tools.cfg'
Generating grub configuration file ...
Found linux image: /boot/vmlinuz-5.15.0-113-generic
Found initrd image: /boot/initrd.img-5.15.0-113-generic
Found linux image: /boot/vmlinuz-5.15.0-107-generic
Found initrd image: /boot/initrd.img-5.15.0-107-generic
Warning: os-prober will not be executed to detect other bootable partitions.
Systems on them will not be added to the GRUB boot configuration.
Check GRUB_DISABLE_OS_PROBER documentation entry.
done
之后就能夠使用 dpkg -r 來刪除內核
sudo dpkg -r linux-image-unsigned-6.6.16-060616-generic
sudo dpkg --purge linux-image-unsigned-6.6.16-060616-generic
重啟之后就能看到內核版本已經恢復到 5.15.x 版本,如下圖:
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 5.15.0-113-generic x86_64)* Documentation: https://help.ubuntu.com* Management: https://landscape.canonical.com* Support: https://ubuntu.com/proSystem information as of Wed Jul 10 11:52:19 AM CST 2024...
再執行 dpkg --list | grep linux-image 會發現原 6.6.16 內核已經刪除,如下圖:
ubuntu@VM-0-6-ubuntu:~$ dpkg --list | grep linux-image
rc linux-image-5.15.0-101-generic 5.15.0-101.111 amd64 Signed kernel image generic
rc linux-image-5.15.0-105-generic 5.15.0-105.115 amd64 Signed kernel image generic
ii linux-image-5.15.0-107-generic 5.15.0-107.117 amd64 Signed kernel image generic
ii linux-image-5.15.0-113-generic 5.15.0-113.123 amd64 Signed kernel image generic
ii linux-image-generic 5.15.0.113.113 amd64 Generic Linux kernel image
5. 吃癟結果
接下來再重新執行 upgrade 和 dist-upgrade 的更新指令,在更新完成后再進行一次掃描,結果炸裂:
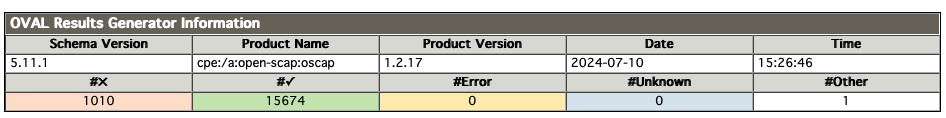
這…這…內核降級后漏洞激增,從原來 127 個 CVE 漏洞上升到 1010 個。通過報告中提供的鏈接得知這些漏洞 Canonical 安全小組也在積極修復中,但大部分漏洞目前還處于 pending 狀態。
雖然這樣…也不全是壞消息,如下圖:
ubuntu@VM-0-6-ubuntu:~$ sudo canonical-livepatch status --verbose
last check: 1 minute ago
kernel: 5.15.0-113.123-generic
server check-in: succeeded
kernel state: ? kernel series 5.15 is covered by Livepatch
patch state: ? no livepatches available for kernel 5.15.0-113.123-generic
tier: updates (Free usage; This machine beta tests new patches.)
machine id: e0fd450343fa48d8acc471dc903518d1
client version: 10.8.3
architecture: amd64
cpu model: AMD EPYC 9754 128-Core Processor
boot time: 1 minute ago
內核降級后 canonical-livepatch 已經能識別當前內核并提供實時保護。
至此,我也沒有辦法了,將情況反饋給項目經理。項目經理與客戶溝通后決定先暫時使用 5.15.x 內核,主要是基于以下原因:
- 目前 5.15.x 內核是受到 canonical-livepatch 保護的,新的安全補丁發布后可以“一鍵修復”且不用重啟,這個大大減少客戶方運維的工作量;
- 目前掃描出來的漏洞基本都是 low 級別漏洞,對系統使用影響不大;
- 最最重要的是客戶方運維不想攬活,而我又沒有時間了,等有時間再幫他們修復吧;








補題)
)




)




