
wi-fi共享大師免廣告

Insecure Wi-Fi is the easiest way for people to access your home network, leech your internet, and cause you serious headaches with more malicious behavior. Read on as we show you how to secure your home Wi-Fi network.
不安全的Wi-Fi是人們訪問您的家庭網絡,竊取您的Internet并通過更多惡意行為使您嚴重頭痛的最簡單方法。 請繼續閱讀,我們會向您展示如何保護家庭Wi-Fi網絡。
為什么要保護您的網絡? (Why Secure Your Network?)
In a perfect world you could leave your Wi-Fi networks wide open to share with any passing Wi-Fi starved travelers who desperately needed to check their email or lightly use your network. In reality leaving your Wi-Fi network open create unnecessary vulnerability wherein non-malicious users can sponge up lots of our bandwidth inadvertently and malicious users can pirate using our IP as cover, probe your network and potentially get access to your personal files, or even worse. What does even worse look like?? In the case of Matt Kostolnik it looks like a year of hell as your crazy neighbor, via your hacked Wi-Fi network, uploads child pornography in your name using your IP address and sends death threats to the Vice President of the United States. Mr. Kolstolnik was using crappy and outdated encryption with no other defensive measures in place; we can only imagine that a better understanding of Wi-Fi security and a little network monitoring would have saved him a huge headache.
在理想的環境中,您可以將Wi-Fi網絡保持開放狀態,以便與任何急需查看電子郵件或輕度使用您的網絡的過往Wi-Fi饑餓的旅行者共享。 實際上,讓您的Wi-Fi網絡保持開放狀態會造成不必要的漏洞,其中非惡意用戶可能會無意間吞噬我們的大量帶寬,惡意用戶可能會使用我們的IP進行盜版,探測您的網絡并有可能訪問您的個人文件,甚至更差。 更糟的是什么樣? 對于馬特·科斯托尼克(Matt Kostolnik)來說,當您瘋狂的鄰居通過被入侵的Wi-Fi網絡,使用您的IP地址以您的名義上傳兒童色情內容并將其發送給美國副總統的威脅時,看起來就像是一個地獄的一年。 Kolstolnik先生使用的是笨拙且過時的加密,沒有其他防御措施。 我們只能想象,對Wi-Fi安全性的更好了解以及對網絡的一點監控將使他免于頭痛。
保護您的Wi-Fi網絡 (Securing Your Wi-Fi Network)

Securing your Wi-Fi network is a multi-step affair. You need to weigh each step and decide if the increased security is worth the sometimes increased hassle accompanying the change. To help you weigh the benefits and drawbacks of each step we’ve divided them up into relative order of importance as well as highlighted the benefits, the drawbacks, and the tools or resources you can use to stress test your own security. Don’t rely on our word that something is useful; grab the available tools and try to kick down your own virtual door.
保護Wi-Fi網絡安全是一個多步驟的過程。 您需要權衡每一步,并確定增加安全性是否值得(有時伴隨變更而增加的麻煩)值得。 為了幫助您權衡每個步驟的利弊,我們將它們分為重要性的相對順序,并重點介紹了利弊,以及可用于壓力測試自己的安全性的工具或資源。 不要依靠我們的話說有用的東西; 抓住可用工具,然后嘗試打開自己的虛擬門。
Note: It would be impossible for us to include step-by-step instructions for every brand/model combination of routers out there. Check the brand and model number on your router and download the manual from the manufacturer’s website in order to most effectively follow our tips. If you have never accessed your router’s control panel or have forgotten how, now is the time to download the manual and give yourself a refresher.
注意:我們不可能為每個品牌/型號的路由器組合都提供分步說明。 檢查路由器上的品牌和型號,然后從制造商的網站下載手冊,以最有效地遵循我們的提示。 如果您從未訪問過路由器的控制面板,或者忘記了操作方法,那么現在該下載手冊并重溫一下自己了。
Update Your Router and Upgrade to Third Party Firmware If Possible: At minimum you need to visit the web site for the manufacture of your router and make sure there are no updates. Router software tends to be pretty stable and releases are usually few and far between. If your manufacturer has released an update (or several) since you purchased your router it’s definitely time to upgrade.
更新路由器并升級到第三方固件(如果可能) :至少您需要訪問制造路由器的網站,并確保沒有更新。 路由器軟件往往非常穩定,發布的版本通常很少。 如果您的制造商自購買路由器以來發布了一個(或多個)更新,那么絕對是時候進行升級了。
Even better, if you’re going to go through the hassle of updating, is to update to one of the awesome third-party router firmwares out there like DD-WRT or Tomato. You can check out our guides to installing DD-WRT here and Tomato here.? The third party firmwares unlock all sorts of great options including an easier and finer grain control over security features.
更好的是,如果您要經歷更新的麻煩,那就可以更新到其中一種出色的第三方路由器固件,例如DD-WRT或Tomato 。 您可以在此處查看有關安裝DD-WRT的指南,在此處查閱番茄的指南。 第三方固件可解鎖各種出色的選擇,包括對安全功能進行更輕松,更精細的控制。
The hassle factor for this modification is moderate. Anytime you flash the ROM on your router you risk bricking it. The risk is really small with third-party firmware and even smaller when using official firmware from your manufacturer. Once you’ve flashed everything the hassle factor is zero and you get to enjoy a new better, faster, and more customizable router.
此修改的麻煩因素是中等的。 每當您刷新路由器上的ROM時,您都有可能對其進行砌塊。 使用第三方固件的風險確實很小,而使用制造商提供的官方固件的風險則更小。 刷新所有內容后,麻煩因素為零,您將可以享用新的更好,更快,更可定制的路由器。
Change Your Router’s Password: Every router ships with a default login/password combination. The exact combination varies from model to model but it’s easy enough to look up the default that leaving it unchanged is just asking for trouble. Open Wi-Fi combined with the default password is essentially leaving your entire network wide open. You can check out default password lists here, here, and here.
更改路由器的密碼:每臺路由器都附帶默認的登錄名/密碼組合。 確切的組合因模型而異,但是可以很容易地查找默認值,即保持不變只是自找麻煩。 與默認密碼結合使用的開放式Wi-Fi本質上使整個網絡保持開放狀態。 您可以在此處,此處和此處簽出默認密碼列表。
The hassle factor for this modification is extremely low and it’s foolish not to do it.
修改的麻煩因素非常低,不這樣做是很愚蠢的。
Turn On and/or Upgrade Your Network Encryption: In the above example we gave, Mr. Kolstolnik had turned on the encryption for his router. He made the mistake of selecting WEP encryption, however, which is the lowest encryption on the Wi-Fi encryption totem pole. WEP is easy to crack using freely available tools such as WEPCrack and BackTrack. If you happened to read the entire article about Mr. Kolstolnik’s problems with his neighbors you’ll note that it took his neighbor two weeks, according to the authorities, to break the WEP encryption. That’s such a long span of time for such a simple task we have to assume that he also had to teach himself how to read and operate a computer too.
打開和/或升級您的網絡加密:在上面給出的示例中,Kolstolnik先生已為其路由器打開了加密。 他選擇了WEP加密時犯了一個錯誤,這是Wi-Fi加密圖騰柱上最低的加密。 使用WEPCrack和BackTrack等免費工具可以輕松破解WEP。 如果您偶然閱讀了整篇有關Kolstolnik先生與鄰居的問題的文章,您會注意到,根據當局的說法,他的鄰居花了兩個星期才破解WEP加密。 對于這樣一個簡單的任務來說,這是很長的時間,我們必須假設他也必須自學如何閱讀和操作計算機。
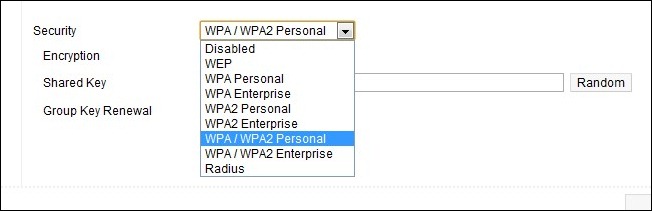
Wi-Fi encryption comes in several flavors for home use such as WEP, WPA, and WPA2. In addition WPA/WPA2 can be further subdivided as WPA/WPA2 with TKIP (a 128-bit key is generated per packet) and AES (a different 128-bit encryption). If possible you want to use WP2 TKIP/AES as AES is not as widely adopted as TKIP. Allowing your router to use both will enable to use the superior encryption when available.
Wi-Fi加密具有多種家用用途,例如WEP , WPA和WPA2 。 此外,WPA / WPA2可以進一步細分為具有TKIP (每個數據包生成128位密鑰)和AES (不同的128位加密)的WPA / WPA2。 如果可能的話,您想使用WP2 TKIP / AES,因為AES沒有像TKIP那樣被廣泛采用。 如果允許路由器同時使用這兩種功能,則可以使用高級加密(如果可用)。
The only situation where upgrading the encryption of your Wi-Fi network may pose a problem is with legacy devices. If you have devices manufactured before 2006 it’s possible that, without firmware upgrades or perhaps not at all, they will be unable to access any network but an open or WEP encrypted network. We’ve phased out such electronics or hooked them up to the hard LAN via Ethernet (we’re looking at you original Xbox).
升級Wi-Fi網絡的加密可能會造成問題的唯一情況是舊設備。 如果您的設備在2006年之前制造,則可能沒有固件升級,或者根本沒有升級,則它們將無法訪問任何網絡,但不能訪問開放或WEP加密的網絡。 我們已經淘汰了此類電子設備,或者通過以太網將它們連接到了硬LAN(我們正在尋找原始的Xbox)。
The hassle factor for this modification is low and–unless you have a legacy Wi-Fi device you can’t live without–you won’t even notice the change.
進行此修改的麻煩性很低,并且-除非您擁有無法缺少的傳統Wi-Fi設備-您甚至都不會注意到這一變化。
Changing/Hiding Your SSID: Your router shipped with a default SSID; usually something simple like “Wireless” or the brand name like “Netgear”. There’s nothing wrong with leaving it set as the default. If you live in a densely populated area, however, it would make sense to change it to something different in order to distinguished it from the 8 “Linksys” SSIDs you see from your apartment. Don’t change it to anything that identifies you. Quite a few of our neighbors have unwisely changed their SSIDs to things like APT3A or 700ElmSt . A new SSID should make it easier for you to identify your router from the list and not easier for everyone in the neighborhood to do so.
更改/隱藏您的SSID :您的路由器附帶默認的SSID; 通常是簡單的“無線”或品牌名稱“ Netgear”。 將其設置為默認值沒有錯。 但是,如果您居住在人口稠密的地區,則可以將其更改為其他名稱,以區別于您在公寓中看到的8個“ Linksys” SSID。 請勿將其更改為可以識別您身份的任何內容。 我們的一些鄰居不明智地將其SSID更改為APT3A或700ElmSt之類的東西。 新的SSID應該更容易讓你從列表中找到您的路由器,而不是更容易為大家在附近這樣做。
Don’t bother hiding your SSID. Not only does it provide no boost in security but it makes your devices work harder and burn more battery life. We debunked the hidden SSID myth here if you’re interested in doing more detailed reading. The short version is this: even if you “hide” your SSID it is still being broadcast and anyone using apps like inSSIDer or Kismet can see it.
不要麻煩隱藏您的SSID。 它不僅不能提高安全性,而且可以使您的設備更努力地工作,并消耗更長的電池壽命。 如果您有興趣進行更詳細的閱讀,我們在這里揭穿了隱藏的SSID神話。 簡短的版本是這樣的:即使您“隱藏” SSID,它仍在廣播,并且使用inSSIDer或Kismet之類的應用程序的任何人都可以看到它。
The hassle factor for this modification is low. All you’ll need to do is change your SSID once (if at all) to increase recognition in a router-dense environment.
此修改的麻煩因素很低。 您需要做的就是一次更改SSID(如果有的話),以在路由器密集的環境中提高識別度。

Filter Network Access by MAC Address:
通過MAC地址過濾網絡訪問:
Media Access Control addresses, or MAC address for short, is a unique ID assigned to every network interface you’ll encounter. Everything you can hook up to your network has one: your XBOX 360, laptop, smartphone, iPad, printers, even the Ethernet cards in your desktop computers. The MAC address for devices is printed on a label affixed to it and/or on the box and documentation that came with the device. For mobile devices you can usually find the MAC address within the menu system (on the iPad, for example, it’s under the Settings –> General –> About menu and on Android phones you’ll find it Settings –> About Phone –> Status menu).
媒體訪問控制地址(簡稱MAC地址)是分配給您將遇到的每個網絡接口的唯一ID。 您可以連接到網絡的所有內容都有一個:XBOX 360,筆記本電腦,智能手機,iPad,打印機,甚至臺式計算機中的以太網卡。 設備的MAC地址印在其粘貼的標簽上和/或設備隨附的包裝盒和說明文件上。 對于移動設備,通常可以在菜單系統內找到MAC地址(例如,在iPad上,位于“設置”->“常規”->“關于”菜單下,而在Android手機上,則可以找到“設置”->“關于手機”->“狀態”菜單)。
One of the easiest ways to check the MAC addresses of your devices, besides simply reading the label on them, is to check out the MAC list on your router after you’ve upgraded your encryption and logged all your devices back in. If you’ve just changed your password you can be nearly certain the iPad you see attached to the Wi-Fi node is yours.
除了簡單地閱讀設備上的標簽外,檢查設備MAC地址的最簡單方法之一就是在升級加密并重新登錄所有設備后檢查路由器上的MAC列表。剛剛更改了密碼,您幾乎可以肯定看到連接到Wi-Fi節點的iPad是您的。
Once you have all the MAC addresses you can set up your router to filter based on them. Then it won’t be enough for a computer to be in range of the Wi-Fi node and have the password/break the encryption, the device intruding on the network will also need to have the MAC address of a device on your router’s whitelist.
擁有所有MAC地址后,您可以設置路由器以基于它們進行過濾。 這樣一來,只要計算機位于Wi-Fi節點的范圍內并擁有密碼/破壞加密是不夠的,侵入網絡的設備還需要將設備的MAC地址列入路由器的白名單中。
Although MAC filtering is a solid way to increase your security it is possible for somebody to sniff your Wi-Fi traffic and then spoof the MAC address of their device to match one on your network. Using tools like Wireshark, Ettercap, and Nmap as well as the aforementioned BackTrack. Changing the MAC address on a computer is simple. In Linux it’s two commands at the command prompt, with a Mac it’s just about as easy, and under Windows you can use a simple app to swap it like Etherchange or MAC Shift.
雖然MAC過濾是增加你的安全有可能有人嗅您的Wi-Fi流量,然后欺騙他們的設備的MAC地址匹配一個網絡上的可靠的方法。 使用Wireshark , Ettercap和Nmap等工具以及上述BackTrack 。 在計算機上更改MAC地址很簡單。 在Linux中,命令提示符下有兩個命令,在Mac上則非常簡單,而在Windows下,您可以使用簡單的應用程序來交換它,例如Etherchange或MAC Shift 。
The hassle factor for this modification is moderate-to-high. If you use the same devices on your network over and over with little change up then it’s a small hassle to set up the initial filter. If you frequently have guests coming and going that want to hop on your network it’s a huge hassle to always be logging into your router and adding their MAC addresses or temporarily turning off the MAC filtering.
此修改的麻煩因素是中等到很高。 如果您一遍又一遍地在網絡上使用相同的設備而幾乎沒有變化,那么設置初始過濾器將很麻煩。 如果您經常有來來去去的來賓希望跳入網絡,那么總是登錄到路由器并添加其MAC地址或暫時關閉MAC過濾非常麻煩。
One last note before we leave MAC addresses: if you’re particularly paranoid or you suspect someone is messing around with your network you can run applications like AirSnare and Kismet to set up alerts for MACs outside your white list.
在我們離開MAC地址之前,請注意的最后一點是:如果您特別偏執狂,或者您懷疑有人在與您的網絡糾纏不清,則可以運行AirSnare和Kismet之類的應用來為白名單之外的MAC設置警報。
Adjust the Output Power of Your Router: This trick is usually only available if you’ve upgraded the firmware to a third party version. Custom firmware allows you to dial up or down the output of your router. If you’re using your router in a one bedroom apartment you can easily dial the power way down and still get a signal everywhere in the apartment. Conversely if the nearest house is 1000 feet away, you can crank the power up to enjoy Wi-Fi out in your hammock.
調整路由器的輸出功率:僅當將固件升級到第三方版本時,此技巧通常才可用。 自定義固件允許您向上或向下撥打路由器的輸出。 如果您在一間臥室的公寓中使用路由器,則可以輕松撥掉電源,仍然可以在公寓中的任何地方獲得信號。 相反,如果最近的房子在1000英尺外,您可以啟動電源以在吊床上享受Wi-Fi的服務。
The hassle factor for this modification is low; it’s a one time modification. If your router doesn’t support this kind of adjustment, don’t sweat it. Lowering the output power of your router is just a small step that makes it necessary for someone to be physically closer to your router to mess with it. With good encryption and the other tips we’ve shared, such a small tweak has a relatively small benefit.
此修改的麻煩因素很低; 這是一次修改。 如果您的路由器不支持這種調整,請不要費力。 降低路由器的輸出功率只是一小步,這使得必須有人在物理上更接近路由器才能將其弄亂。 通過良好的加密和我們分享的其他技巧,進行這樣的小調整將帶來相對較小的收益。
Once you’ve upgraded your router password and upgraded your encryption (let alone done anything else on this list) you’ve done 90% more than nearly every Wi-Fi network owner out there.
升級路由器密碼并升級加密功能(更不用說執行此列表上的其他任何操作)后,您完成的工作幾乎比幾乎每個Wi-Fi網絡所有者都要多90%。
Congratulations, you’ve hardened your network enough to make almost everyone else look like a better target! Have a tip, trick, or technique to share? Let’s hear about your Wi-Fi security methods in the comments.
恭喜,您已經加強了網絡,可以使幾乎所有其他人看起來像是更好的目標! 有技巧,竅門或技巧可以分享嗎? 讓我們在評論中了解您的Wi-Fi安全方法。
翻譯自: https://www.howtogeek.com/68403/how-to-secure-your-wi-fi-network-against-intrusion/
wi-fi共享大師免廣告




)

![[Erlang 0004] Centos 源代碼編譯 安裝 Erlang](http://pic.xiahunao.cn/[Erlang 0004] Centos 源代碼編譯 安裝 Erlang)




![轉]MATLAB 與 C 語言的接口](http://pic.xiahunao.cn/轉]MATLAB 與 C 語言的接口)



)



