相關文章:
.NET 反向代理-YARP
.NET 反向代理-YARP 根據域名轉發
分享一個基于Abp 和Yarp 開發的API網關項目
使用 Yarp 做網關
YARP(Yet Another Reverse Proxy)是使用 .NET 構建的高度可定制的反向代理
C# 開源一個基于 yarp 的 API 網關 Demo,支持綁定 Kubernetes Service
微軟的反向代理項目 ReverseProxy 更名為 Yarp.ReverseProxy
? ? ?YARP 作為反向代理中間件,那就無可避免需要使用到 Https 去部署項目,那 YARP 要怎么去實現呢,本來以為?YARP 會有一套自己的實現,在翻閱了資料后發現,根本不是我想的那樣,按照?YARP 官方文檔的說法,是按照 .Net Core 原本的那一套去實現,好家伙,真的沒想到啊,下面我貼出官方原文,大伙看一看,瞧一瞧

IIS就不多說了,這個畢竟只能在 windows 上使用,下面我說說 在?Kestrel 怎么設置 Https 吧,按照我的慣例,直接貼配置文件
"Kestrel": {"Endpoints": {"MySniEndpoint": {"Url": "https://*:5209","SslProtocols": [ "Tls11", "Tls12" ],"Sni": {"test1.ysmc.net.cn": {"Certificate": {"Path": "[path]\\test1.ysmc.net.cn_server.pfx","Password": "pfx密碼"}},"test2.ysmc.net.cn": {"Certificate": {"Path": "[path]\\test2.ysmc.net.cn_server.pfx","Password": "pfx密碼"}}}}},//,默認配置,當沒有配置的時候,默認回落到這個配置 "Certificates": {"Default": {"Path": "[path]\\test1.ysmc.net.cn_server.pfx","Password": "pfx密碼"}}因為我們需要配置多個域名,所以使用到了 Sni,下面是官方對一 Sni 的部分介紹,感興趣的小伙伴可以過去看看,傳送門:https://learn.microsoft.com/zh-cn/aspnet/core/fundamentals/servers/kestrel/endpoints?view=aspnetcore-6.0#sni-in-configuration-1
SNI in configuration
Kestrel supports SNI defined in configuration. An endpoint can be configured with an?object that contains a mapping between host names and HTTPS options. The connection host name is matched to the options and they are used for that connection.Sni
The following configuration adds an endpoint named?that uses SNI to select HTTPS options based on the host name:MySniEndpoint
HTTPS options that can be overridden by SNI:
Certificate?configures the?certificate source.Protocols?configures the allowed?HTTP protocols.SslProtocols?configures the allowed?SSL protocols.ClientCertificateMode?configures the?client certificate requirements.
The host name supports wildcard matching:
Exact match. For example,?matches?.
a.example.orga.example.orgWildcard prefix. If there are multiple wildcard matches then the longest pattern is chosen. For example,?matches?and?.
*.example.orgb.example.orgc.example.orgFull wildcard.?matches everything else, including clients that aren't using SNI and don't send a host name.
*
The matched SNI configuration is applied to the endpoint for the connection, overriding values on the endpoint. If a connection doesn't match a configured SNI host name then the connection is refused.
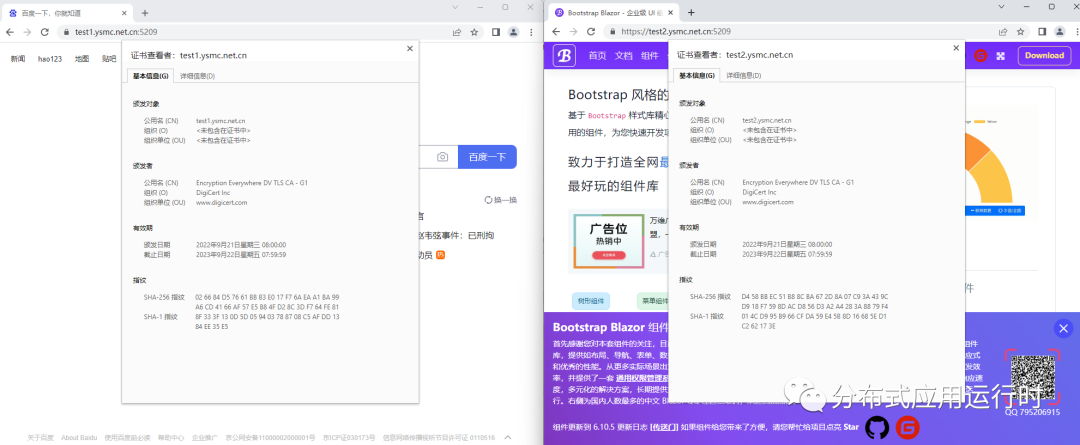
下面一起看看配置后的效果吧,非常的完美
? 整個完整的配置文件我也貼出來吧,至于證書怎么申請的,大家有域名的可以到域名服務商里申請免費1年期的,沒有域名的話,可以自己改一下hosts 文件 然后自己自簽名一個,都是可以的
appsettings.json
{"Logging": {"LogLevel": {"Default": "Information","Microsoft.AspNetCore": "Warning"}},"Kestrel": {"Endpoints": {"MySniEndpoint": {"Url": "https://*:5209","SslProtocols": [ "Tls11", "Tls12" ],"Sni": {"test1.ysmc.net.cn": {"Certificate": {"Path": "[path]\\test1.ysmc.net.cn_server.pfx","Password": "pfx密碼"}},"test2.ysmc.net.cn": {"Certificate": {"Path": "[path]\\test2.ysmc.net.cn_server.pfx","Password": "pfx密碼"}}}}},"Certificates": {"Default": {"Path": "[path]\\test1.ysmc.net.cn_server.pfx","Password": "pfx密碼"}}},"ReverseProxy": {"Routes": {"baidu": {"ClusterId": "baidu","Match": {"Hosts": [ "test1.ysmc.net.cn" ],"Path": "{**catch-all}"}},"blazor": {"ClusterId": "blazor","Match": {"Hosts": [ "test2.ysmc.net.cn" ],"Path": "{**catch-all}"}}},"Clusters": {"baidu": {"LoadBalancingPolicy": "RoundRobin","Destinations": {"baidu": {"Address": "https://www.baidu.com/"}}},"blazor": {"LoadBalancingPolicy": "RoundRobin","Destinations": {"blazor": {"Address": "https://www.blazor.zone/"}}}}}
}?原文鏈接:https://www.cnblogs.com/ysmc/p/16717580.html







)
)

 新增19年阿里面題(反向拓展技術棧))








